Hey, there? I have a problem about my Mac computer. It is not a very urgent issue. I am able to use it now. The story is that my son used my computer to see porn things some time ago and the computer got this thing named Search.useaget.com. I didn’t blame him hard for this matter. He is still young. And he promised to never do it again. But I really want to get this thing out of my Mac computer in case more unknown potential risks are caused. Anybody can help? Much appreciated!
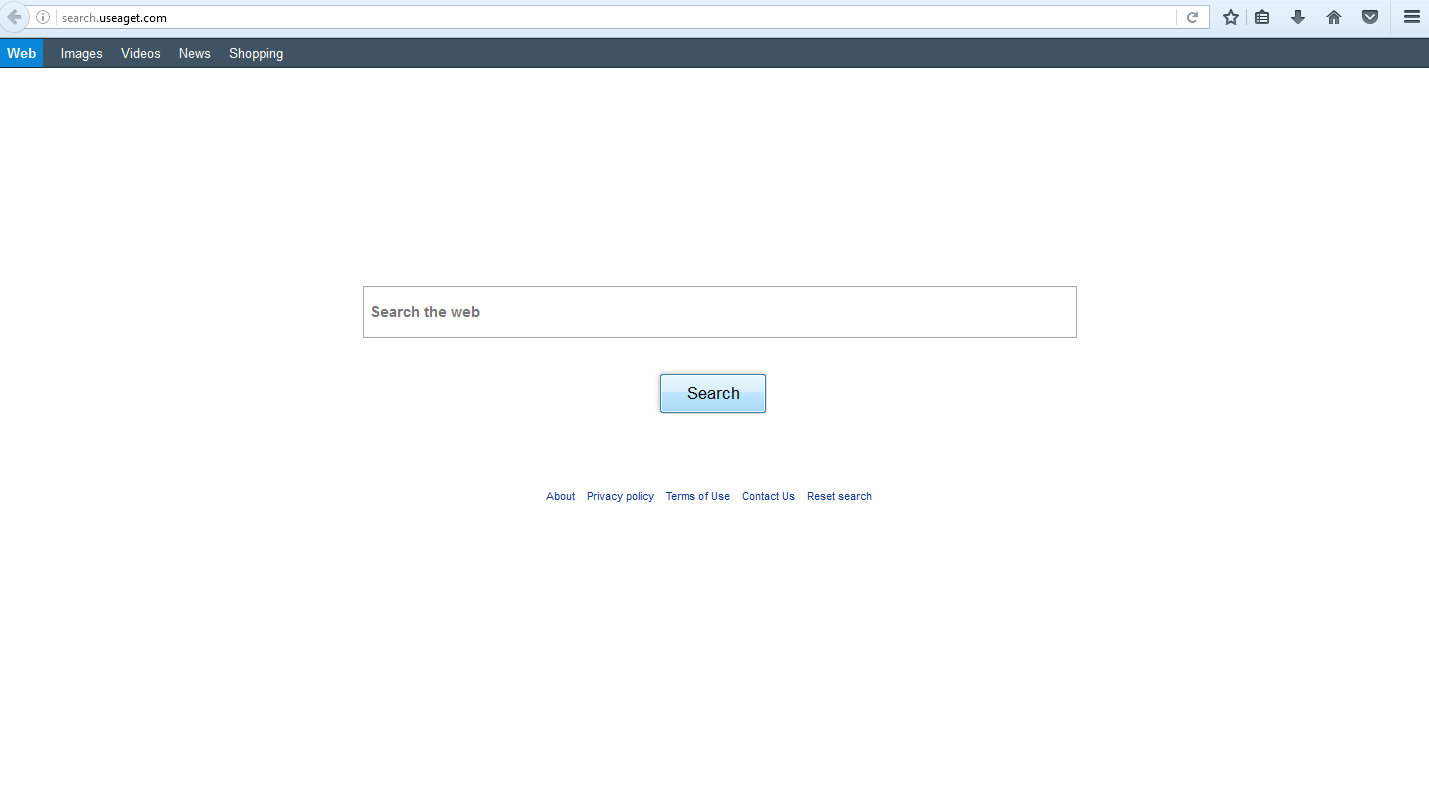
The Search.useaget.com is a browser hijacker that provides Yahoo search results. With the help of an innocent look, and the brand of Yahoo, which is credible and well-known all around the world, the Search.useaget.com has succeeded in infecting many computers such as Macbooks of Apple company. This is one of the tricks that a browser hijacker like Search.useaget.com usually play to fool computer users into its trap. If you are a careful computer user, you should be able to find that it is a MODIFIED Yahoo result page that is full of useless and questionable ads or sponsored links by looking at the tab name while typing anything into the Search.useaget.com box to search things on the internet. According to reliable reports from reliable sources, the tab name should say something together with “Genieo”. And “Genieo Yahoo Search.” is what we find in our test. As for what is the “Genieo”, it is something that is malicious you can get confirmation from articles on the internet.
It is not the worst situation if no further potential risks can be caused by the Search.useaget.com virus. Unfortunately, we do have serious issues to worry about. First, your work efficiency will be greatly affected in a negative way. All computer users would like its search engine to provide useful and accurate results in an organic way rather than a result page that is full of useless or suspicious ad links whenever they are entering any search query to search what they desire on the internet. But such a modified result page is not avoidable for any user whose browser has been hijacked by the Search.useaget.com virus. Secondly, the safety of those ad links is another issue that should be seriously regarded. A browser hijacker like Search.useaget.com is usually sponsored by companies or individuals whose reliability is not known to make more profits. Well-known or ill-known, reliable or suspicious are no longer the factors taken into consideration to evaluate a sponsor in this case. To maximize the profit margin to the greatest degree in a short period of time is what they are in pursuit. So, some malicious links may hide themselves among the sponsored links. One click on them may direct you to visit a malware-laden websites such as a pornographic site, and a more violent virus may thus take the advantage to sneak into your computer. And your system will soon be put into complete danger.
There are some common ways to keep away from a virus like Search.useaget.com. If you can take some time to closely study the ways provided here and keep practicing what you have learned in the daily use of your computer, you will be able to block such a browser hijacker as Search.useaget.com from being downloaded into your system or avoid installing it in the process of installing a program. On the contrary, your computer will undoubtedly and more possibly, be exposed to threats like the Search.useaget.com and other viruses because of your little knowledge about how a virus distributes itself. First, we don’t recommend to visit any suspicious website to download any freeware or shareware. Because suspicious websites such as pornographic sites and freewares or sharewares are popular methods taken advantage by the Search.useaget.com-like viruses. Secondly, when you install a program, however the program looks like, suspicious or reliable, well-known or ill-known, never forget to select the “Advanced” or similar options to check whether there is malicious programs bundled to the desired program. If not, you can continue to install the program on your system. These two ways are easy to understand and to help stay away from the Search.useaget.com and other viruses, it just requires you to practice something like establishing proper habits in the daily use of your computer.
The virus hijacks your browser to redirect your web search results and changes the homepage and browser settings. To completely uninstall it from an infected system, manual removal is the first choice because sometimes antivirus software cannot pick up the exact computer threat timely or remove it permanently. Now most browser hijackers are quite similar to spyware and adware threats and therefore cannot be removed with the help of popular antivirus products. Users can follow the manual guide here to get rid of this browser hijacker completely.
1. Clear all the cookies of the the virus from your affected browsers.
Since this tricky virus is able to use cookies for tracing and tracking the internet activity of users, it is suggested users clean up all the cookies before a complete removal.
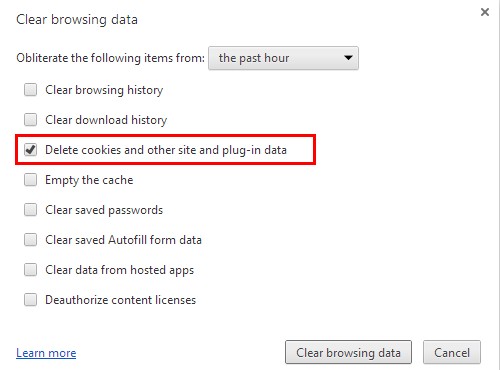
Google Chrome:
Click on the “Tools” menu and click the “Clear browsing data” button.
Select “Delete cookies and other site data” to delete all cookies from the list.
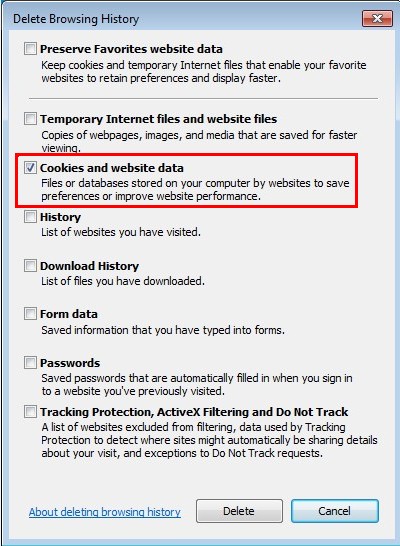
Internet Explorer:
Open Internet explorer window
Click the “Tools” button
Point to “safety” and then click “delete browsing history”
Tick the “cookies” box, then click “delete”
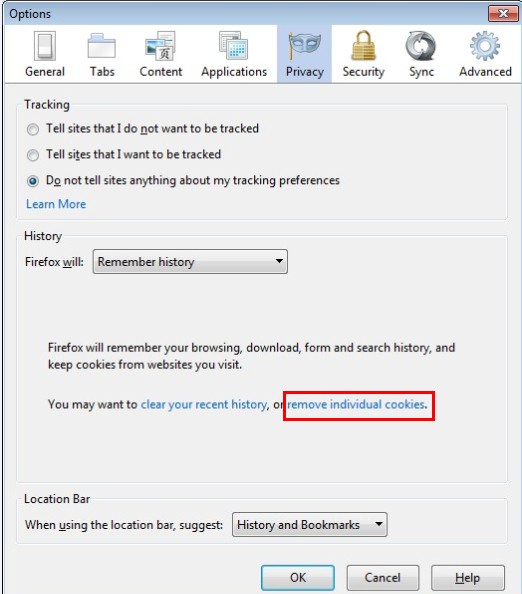
Mozilla Firefox:
Click on Tools, then Options, select Privacy
Click “Remove individual cookies”
In the Cookies panel, click on “Show Cookies”
To remove a single cookie click on the entry in the list and click on the “Remove Cookie”
To remove all cookies click on the “Remove All Cookies” button
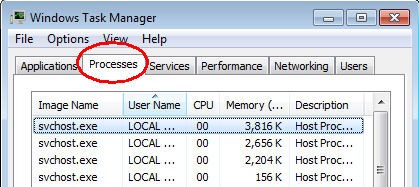
2. End the malicious process of the Search.useaget.com from Task Manager.
Once the hijacker is installed, computer user may notice that CPU usage randomly jumps to 100 percent. At any time Windows always has many running processes. A process is an individual task that the computer runs. In general, the more processes, the more work the computer has to do and the slower it will run. If your system’s CPU spike is constant and remain at a constant 90-95%, users should check from Task Manager and see if there is a suspicious process occupying the system resources and then end it immediately.
(The name of the virus process can be random.)
Press Ctrl+Shift+Esc to quickly bring up Task Manager Window:
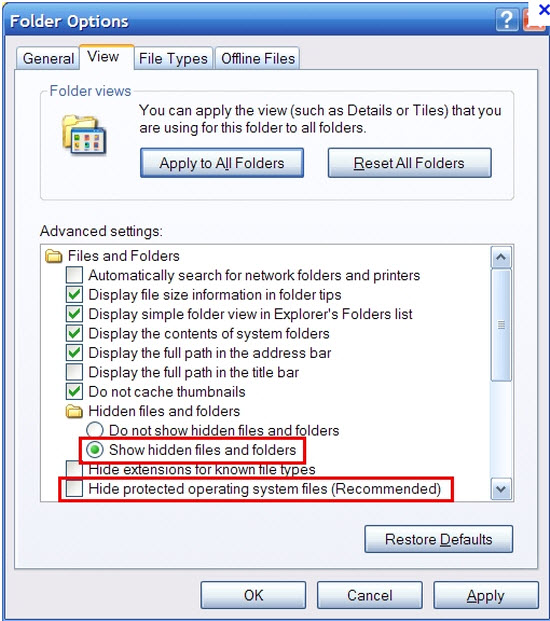
3. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
4. Delete all the malicious files related to the hijacker manually.
%AppData%Local[random].exe
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\*.exe
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main StartPage
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
There is a kind of malicious program or virus named browser hijacker. It is a virus that will be able to cause many inconveniences and bring about really bad surfing experience for computer users who use the infected web browser to start browsing activities on the internet. The program, which is called Search.useaget.com, has been defined as a browser hijacker because of its suspicious and outrageous functionality that is commonly used to judge whether a program is a browser hijacker or not. Therefore, if you determine to select a program as your regular search engine on a daily base, it is strongly recommended to put the Search.useaget.com out of your selection list that includes all brands of search engines available for selecting from. If you find that your Mac computer has been infected with the Search.useaget.com without any knowledge, you are suggested to have it removed at once completely without any delay even though it has a handsome and elegant appearance like the Mac devices’ design and may attract some computer users.
Note: If you have little knowledge about computer and do not know how to operate the removal, please contact experts from YooCare Online Tech Support for further help.
Published by on November 15, 2016 6:47 pm, last updated on November 21, 2016 3:27 am



Leave a Reply
You must be logged in to post a comment.