Your computer is invaded by TR/Crypt.ZPACK.Gen8? It makes your computer become very terrible? Computer users should know that Trojan horse is the most common method for cyber criminals to infect your computer and collect your personal information. Therefore, if your computer is infected with this Trojan virus, you must remove it manually because it is able to evade security tools and destroy your computer system. If you do not have any clues, please read this article.
TR/Crypt.ZPACK.Gen8 is a Trojan virus that you should not scorn. Trojan infections are all very hazardous since they have the ability to bring other malicious computer threats to further damage the infected computer. This Trojan we focus on now is one of them. In general, it spreads in the Internet world. If you click unknown links and open spam email attachments accidentally, you are likely to activate its download. In addition, it also can spread through the infected files in shared folders, USB devices and other unsafe external devices.
In order to create a good living environment for itself, TR/Crypt.ZPACK.Gen8 keeps bringing various risky worms, spyware or fake antivirus software into your computer. Because your computer is full of all kinds of restless things, the response speed of the computer is very slow. Boot time is longer than usual and you can do nothing but wait. After all, shutting down the computer forcedly when the computer system is loading will cause hardware damages. The Trojan is used by cyber criminals to achieve a variety of evil goals. Once it gets into your computer, you should be careful about your computer operations because it is a great threat to your personal data. It opens a door in the infected computer, allowing cyber criminals to access your computer system as well as stealing your social and financial information while you know nothing. Moreover, it is capable of reducing the performance of your computer and eventually leading to system collapse. Now, you should be absorbed in removing it. It puts malicious files into your hard drive secretly and changes registry entries of your operating system, which provides convenience for it to process self-replicate, disable many important functions of security software and modify system settings.
TR/Crypt.ZPACK.Gen8 is a very malicious Trojan virus that has the ability to download additional components and other infections in the target computer in order to fully complete its penetration. It will be activated after the computer user opens unknown email attachments or visits phishing websites. In addition, it is also able to sniff computer system vulnerabilities and then initiate the attack immediately. It can be detected by antivirus software, but, according to the complaints from the victims, it can escape from the removal of antivirus software, which is ascribed to its compulsive modifications to the system database. As a result, delaying getting rid of it may lead to: a). It is able to cause system crash and destroy some of your programs in the infected computer. b). It facilitates the virus makers to intrude your computer remotely without letting you know. c). It brings in some other threats including ransomware, adware parasites, spyware and worms. d). It is capable of collecting your browsing history and other private data.
This malicious Trojan virus can install itself into the computer system without your consent and awareness. It makes your computer work slowly and implants other nasty infections into the computer. To make things worse, this Trojan is a tool for the cyber criminals to invade the infected computer to steal your information. Through making use of advanced technology, it maintains the ability to combine its components with system files or to generate fake system files, which confuses computer users as well as antivirus programs. They cannot identify it accurately and timely, let alone remove it thoroughly. Therefore, manual removal is the best choice to drive it away from your computer. In this case, you are advised to delete every file generated by it manually so as to spare all later trouble. The manual removal needs to be handled carefully so as to avoid any subsequent damages. Users can follow the manual guide here to have the hijacker removed instantly.
(1). Press Ctrl+Alt+Delete together to bring out Windows Task Manager, click Processes tab
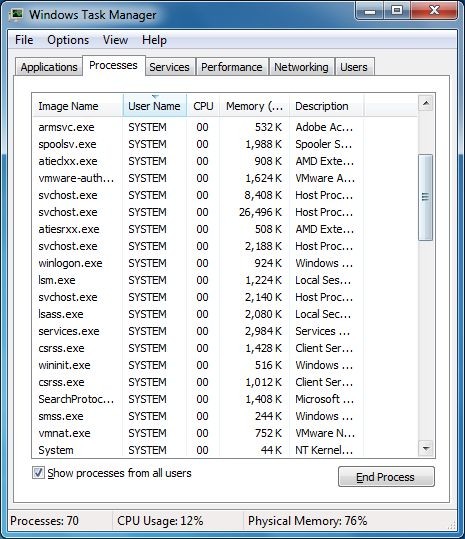
(2). Find out and end the processes of TR/Crypt.ZPACK.Gen8
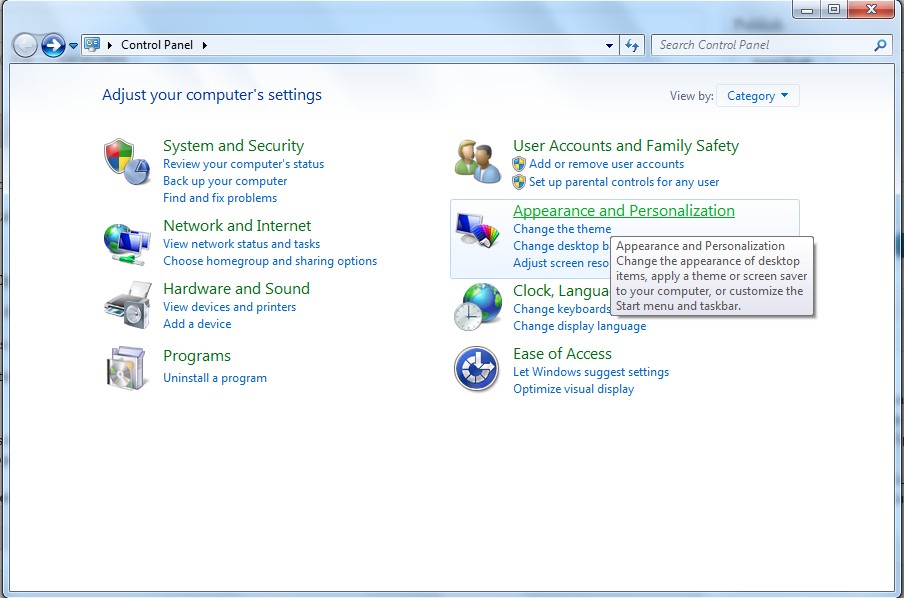
(1). Click on the Start button and then on Control Panel
(2). Click on the Appearance and Personalization
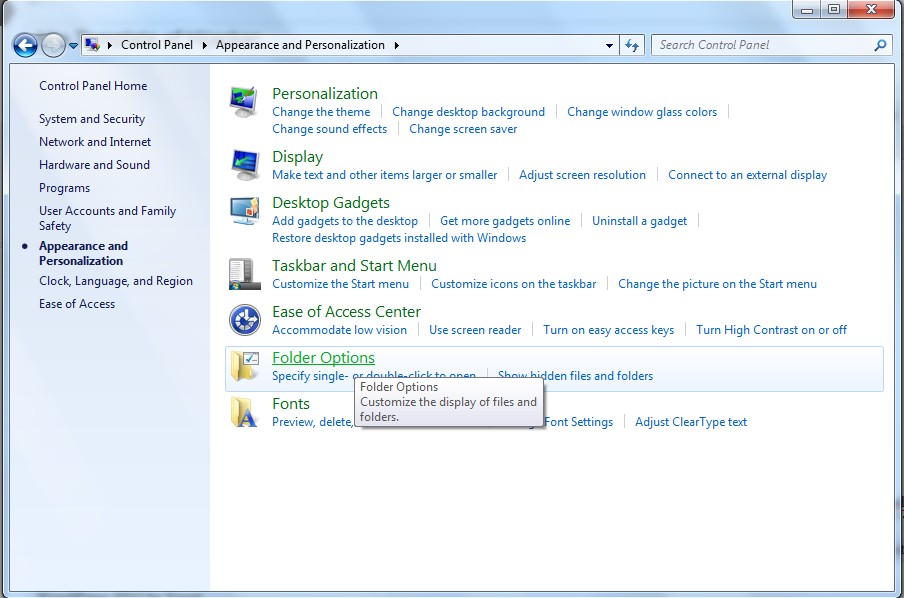
(3). Click on the Folder Options
(4). Click on the View tab in the Folder Options window
(5). Choose the Show hidden files, folders, and drives under the Hidden files and folders category
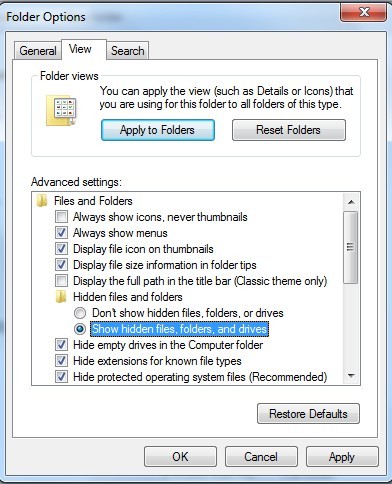
(6). Click OK at the bottom of the Folder Options window.
(1). Delete the registry entries of TR/Crypt.ZPACK.Gen8 through Registry Edit
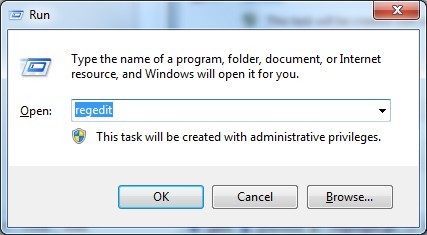
Guides to open registry editor: Click “Start” menu, hit “Run”, then type “regedit”, click “OK”
While the Registry Editor is open, search and delete its registry entries.
(2). Find out and remove the associated files of this virus in the system.
TR/Crypt.ZPACK.Gen8 is classified as a dangerous Trojan horse which is able to sneak into the target computer. This threat is designed by cyber criminals in some time ago, but it is still very popular. Many computer users discover its existence in the computer but do not know how it gets in for it can enter into the computer quietly. This Trojan infects your computer via different ways, such as spam email attachments and websites containing malicious script or fake codec. Like other Trojans, it also brings in other types of infections. Many victims may have tried a lot of antivirus software but still cannot remove it successfully. Its malicious files are scattering in the computer system, preventing antivirus software from clearing off it. Therefore, you should take manual removal so as to drive TR/Crypt.ZPACK.Gen8 away completely.
The above manual removal process is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on December 12, 2013 10:19 am, last updated on December 12, 2013 10:19 am



Leave a Reply
You must be logged in to post a comment.