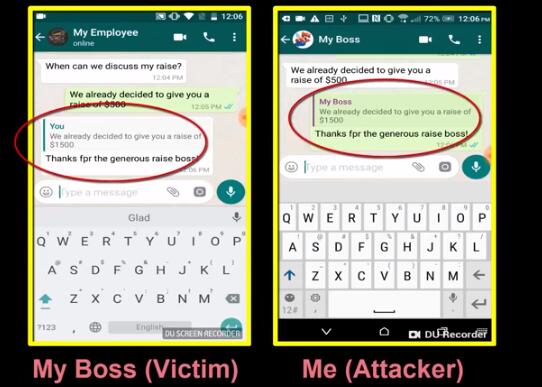
A high-risk vulnerability was exposed on WhatsApp, a Facebook-based instant messaging app for about 1.5 billion users worldwide. It could enable an attacker to use the platform to manipulate or tamper with chat messages, in both public conversations mode and private conversations.
According to Check Point, the vulnerability “could allow threat actors to intercept and manipulate messages sent in both private and group conversations, giving attackers immense power to create and spread misinformation from what appear to be trusted sources.”
Security vendor Check Point noted that its researchers have identified three ways to change user conversations. Firstly, they use the “reference” function in the group conversation to change the identity of the sender of the message. Secondly, it allows the hacker to change the text replied by others. Thirdly, it allows one person to send a private message to another group participant, pretending to be a public information person sent to everyone. This way, when the target individual replies, everyone in the conversation can see it. Currently, the third bugs have been fixed.
Odle Vanunu, head of vulnerability research at Check Point, believes that these vulnerabilities could have major consequences because WhatsApp has about 1.5 billion users and is widely used for personal conversations, business communications, and political messaging.
Check Point also said that they notified WhatsApp of those vulnerabilities at the end of last year, but WhatsApp believed only one of them was the real vulnerability, namely the one could disguise private information as public information that can be viewed by the entire chat group. The vulnerability later was fixed.
Check Point is currently working with WhatsApp to fix those vulnerabilities. The problem is it is difficult to fix them due to the encryption of the messaging application. We expect that the vulnerabilities will be fixed timely, so all users can use this app to communicate at ease mind.
Published by on August 14, 2019 2:48 am, last updated on August 14, 2019 2:54 am



Leave a Reply
You must be logged in to post a comment.