Hi, there? Please help me. I think I have been hacked. There is a thing named Startjoytabsearch.com stay on my Microsoft edge all the time. You don’t know how nasty it is. My homepage domain has been replaced, and so is the search engine of Google. It brings me a lot of inconveniences and troubles because I get used to the Google search engine and my original homepage is the one I have to visit a lot every day. I don’t know how this domain sneaks into my computer. I believe I have done nothing wrong. Anyway, I want to remove it out of my computer completely without any delay. Because I search information about it online that it is a browser hijacker and will causes a lot of problems. But the issue now is no matter how hard I tried to remove it all by myself, just failed. I am so disappointed. Please help me. Much appreciated!!
Startjoytabsearch.com is a browser extension that becomes the focus of the reviewers recently. As a matter of fact, the word “reported” will be a more accurate wording to sum up the reviews involved with the program. Startjoytabsearch.com has been classified into the category of browser hijacker since it was put forward. How does this happen? There are three aspects that can help ascertain this judge. The Startjoytabsearch.com is actually a mediator between to the victim and a world famous search engine. When you try to search items on the internet with the search facility the Startjoytabsearch.com provides, a changed yahoo webpage will be displayed as the outcome of your search operation. On the Startjoytabsearch.com page, a bunch of links are provided. Anytime you click on one of them, you will be redirected to a popular site. Besides, when infected with the latter version, the default homepage of the victim will be changed into something related to the Startjoytabsearch.com and all this is done by default without victim’s control over them. Finally, the fact that the Startjoytabsearch.com is also a potentially unwanted application adds to the classification of the extension into the category of the browser hijacker. It is reported that the Startjoytabsearch.com is developed to help advertise some specific content of its sponsors or partners.
One aspect about browser hijacker known to many people is that these kinds of unwanted programs are generally spreaded with other ad-supported applications. Together with these adware programs, they are usually bundled within the installers of freeware or shareware. While, to decide which specific freeware or shareware installer will contain the Startjoytabsearch.com is , in fact, a really difficult task to carry out. On some occasions, it even becomes impossible. However, there is a highly effective and efficient method that will help prevent the Startjoytabsearch.com browser hijacker and any other similar hijacker form infecting your computer. If you can’t tell whether there is malicious program like the Startjoytabsearch.com included in to installer of a piece of freeware or shareware, you are recommended to make full use of the Advanced/Custom mode of the installation wizard. It is an easy way to help both computer newbies and experts to protect their devices from the Startjoytabsearch.com-like infections.
Startjoytabsearch.com hijacks your browser to redirect your web search results and changes the homepage and browser settings. To completely uninstall it from an infected system, manual removal is the first choice because sometimes antivirus software cannot pick up the exact computer threat timely or remove it permanently. Now most browser hijackers are quite similar to spyware and adware threats and therefore cannot be removed with the help of popular antivirus products. Users can follow the manual guide here to get rid of this browser hijacker completely.
1. Clear all the cookies of the Startjoytabsearch.com from your affected browsers.
Since this tricky Startjoytabsearch.com virus is able to use cookies for tracing and tracking the internet activity of users, it is suggested users clean up all the cookies before a complete removal.
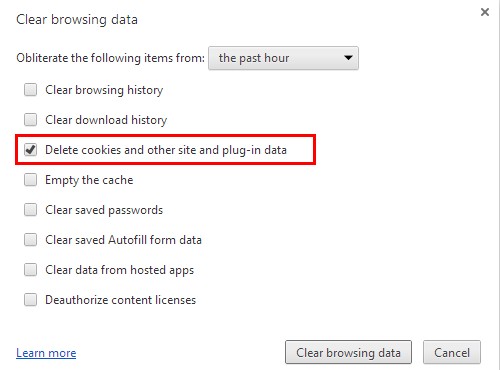
Google Chrome:
Click on the “Tools” menu and click the “Clear browsing data” button.
Select “Delete cookies and other site data” to delete all cookies from the list.
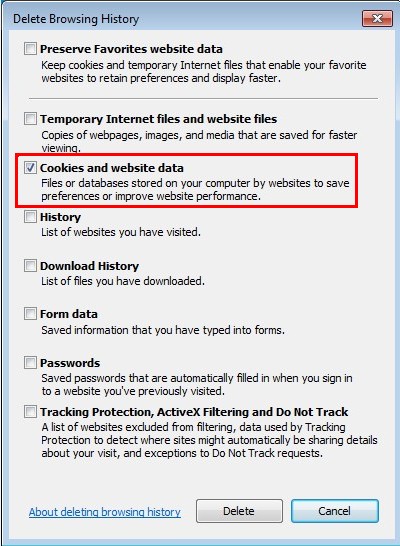
Internet Explorer:
Open Internet explorer window
Click the “Tools” button
Point to “safety” and then click “delete browsing history”
Tick the “cookies” box, then click “delete”
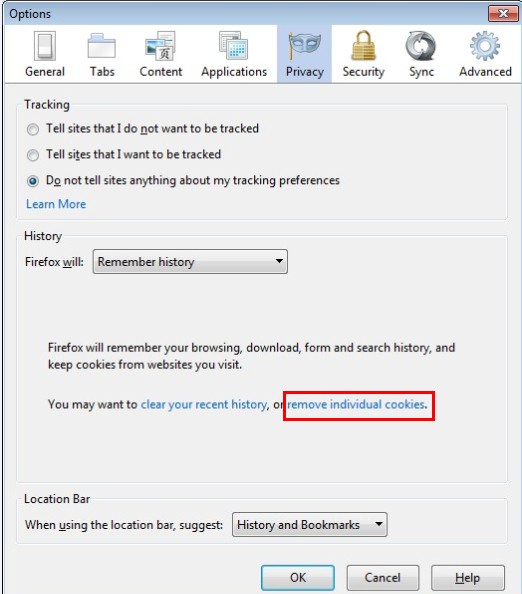
Mozilla Firefox:
Click on Tools, then Options, select Privacy
Click “Remove individual cookies”
In the Cookies panel, click on “Show Cookies”
To remove a single cookie click on the entry in the list and click on the “Remove Cookie”
To remove all cookies click on the “Remove All Cookies” button
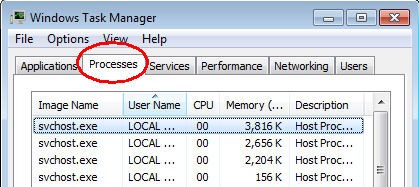
2. End the malicious process of the Startjoytabsearch.com from Task Manager.
Once Startjoytabsearch.com hijacker is installed, computer user may notice that CPU usage randomly jumps to 100 percent. At any time Windows always has many running processes. A process is an individual task that the computer runs. In general, the more processes, the more work the computer has to do and the slower it will run. If your system’s CPU spike is constant and remain at a constant 90-95%, users should check from Task Manager and see if there is a suspicious process occupying the system resources and then end it immediately.
(The name of the virus process can be random.)
Press Ctrl+Shift+Esc to quickly bring up Task Manager Window:
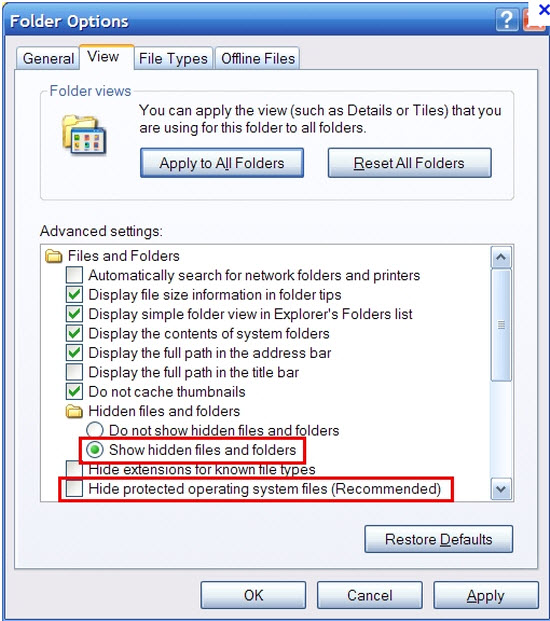
3. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
4. Delete all the malicious files related to Startjoytabsearch.com hijacker manually.
%AppData%Local[random].exe
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\*.exe
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main StartPage
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Startjoytabsearch.com has been categorized into the kind of virus of browser hijacker. It has been reported that, many web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, Safari browser or Microsoft Edge and so on can be locked as targets of the Startjoytabsearch.com virus. Like any other browser hijacker, after infection, the Startjoytabsearch.com will try every effort to get control over the victim by replacing the default homepage domain and search facility of the web browser without the victim’s permission. And the Startjoytabsearch.com is accused of causing many suspicious and annoying advertisements and redirections that will bring about tons of inconveniences and may help introduce more violent viruses into the victim’s computers. When it speaks to the removal of the Startjoytabsearch.com virus, it is reported many antivirus applications prove to be useless on these occasions while manual removal carried out by an expert turns out to be most effective and efficient. So when you find such an infection like the Startjoytabsearch.com on your system, it is recommended to talk to a professional as soon as possible.
Note: If you have little knowledge about computer and do not know how to operate the removal, please contact experts from YooCare Online Tech Support for further help.
Published by on January 1, 2017 4:37 am, last updated on January 1, 2017 4:37 am



Leave a Reply
You must be logged in to post a comment.