Hey, there. I was fooled into installing this thing called Search.safefinderformac.com. When I first see it, I thought it should be as good as it looks. What is more, it looks like a thing developed by the Apple company or its joint company or something like that. It turns out to be wrong. When I saw the advertisements targeted my hobbies and preference on every website I visited. I was surprised and scared. I am worrying about its reliability now. I hope everything is fine and it is not too late to remove it completely for the moment. Please help! I will be thankful if you can help!
Before we go ahead in this article, you may show great interest in the Search.safefinderformac.com program because of its simple but charming and elegant appearance design. Yes, it looks pretty good. But it is, specifically for Mac users, actually a malicious browser hijacker designed to work in all suspicious sorts of ways to endangering your benefits by Linkury company. For this reason, it is not difficult for you to find many removal guides that can walk you through to get rid of the suspicious Search.safefinderformac.com add-on. The safari browser is a more attractive target for the Search.safefinderformac.com hijacker. The first reason why this add-on is classified into the category of browser hijacker is the way how it sneaks into a user’s computer. According to reliable reports, the Search.safefinderformac.com add-on usually get itself installed on a user’s browser automatically and secretly. The second reason that makes the Search.safefinderformac.com ill-known is its suspicious behavior of replacing the default search engine of a computer user. For users who very much get accustomed to a particular search facility, for example, the Google search engine, this will cause plenty of inconveniences and result in annoying experience of using the browser. The most questionable issue involved with the Search.safefinderformac.com program is its features as a potentially unwanted program. Many victims notice there are many unbelievably accurate personalized advertising content targeted their preferences and interests on the webpages they are browsing. Because by taking advantage of the tracking technology, the Search.safefinderformac.com is able to accurately get to know about your likes and dislikes, and accordingly insert the content that will interest you. This will undoubtedly greatly shock a prudent person like me. How do they get to know my interests and preferences? And how about my other personal information like credit card details, login credentials and banking information? Are these information still safe or stolen? Yes, I know, it is totally a nightmare. What is worse, unfortunately, the answer to what you are worrying about is something that will make you frightened. The designer of this program may legally and easily collect all kinds of your personal information by making unfair statements in their Privacy Policy.
How to get your Mac or other computers safe from being infected with such a malicious program like the Search.safefinderformac.com add-on in the daily use of a computer? This is the most common and most frequently asked question when talking about computer issues relating to security. In my opinion, the best way is nothing but never let your computer get used in these ways as follow. First, stay away from suspicious websites such as pornographic or gambling sites. Second, bid farewell to the shareware or freeware program. If you have to install such a program, great attention is needed to pay to the installing process of the program. Finally, learn more about how to properly operate a computer in the daily use of a computer and establish yourself a good habit.
Search.safefinderformac.com hijacks your browser to redirect your web search results and changes the homepage and browser settings. To completely uninstall it from an infected system, manual removal is the first choice because sometimes antivirus software cannot pick up the exact computer threat timely or remove it permanently. Now most browser hijackers are quite similar to spyware and adware threats and therefore cannot be removed with the help of popular antivirus products. Users can follow the manual guide here to get rid of this browser hijacker completely.
1. Clear all the cookies of the virus from your affected browsers.
Since this tricky virus is able to use cookies for tracing and tracking the internet activity of users, it is suggested users clean up all the cookies before a complete removal.
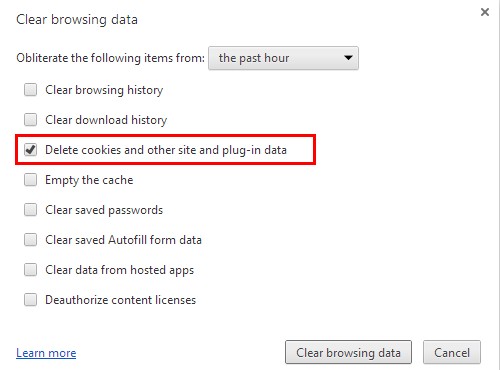
Google Chrome:
Click on the “Tools” menu and click the “Clear browsing data” button.
Select “Delete cookies and other site data” to delete all cookies from the list.
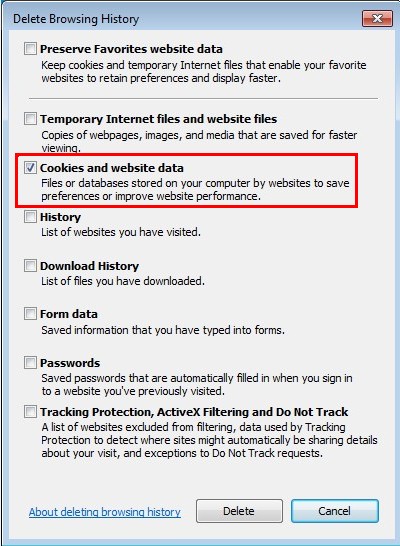
Internet Explorer:
Open Internet explorer window
Click the “Tools” button
Point to “safety” and then click “delete browsing history”
Tick the “cookies” box, then click “delete”
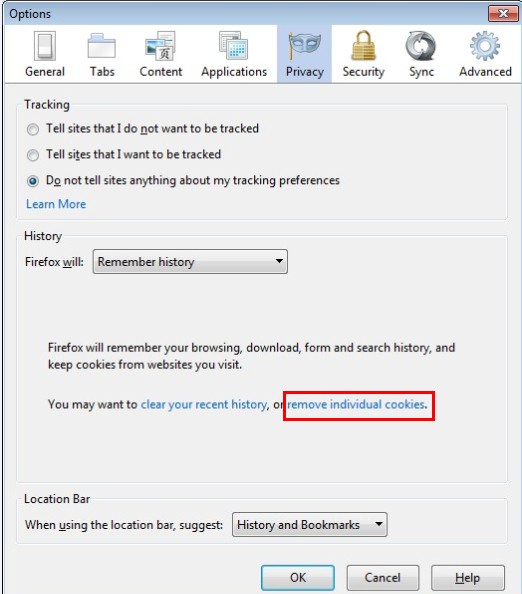
Mozilla Firefox:
Click on Tools, then Options, select Privacy
Click “Remove individual cookies”
In the Cookies panel, click on “Show Cookies”
To remove a single cookie click on the entry in the list and click on the “Remove Cookie”
To remove all cookies click on the “Remove All Cookies” button
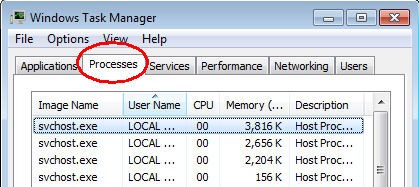
2. End the malicious process of the Search.safefinderformac.com from Task Manager.
Once this hijacker is installed, computer user may notice that CPU usage randomly jumps to 100 percent. At any time Windows always has many running processes. A process is an individual task that the computer runs. In general, the more processes, the more work the computer has to do and the slower it will run. If your system’s CPU spike is constant and remain at a constant 90-95%, users should check from Task Manager and see if there is a suspicious process occupying the system resources and then end it immediately.
(The name of the virus process can be random.)
Press Ctrl+Shift+Esc to quickly bring up Task Manager Window:
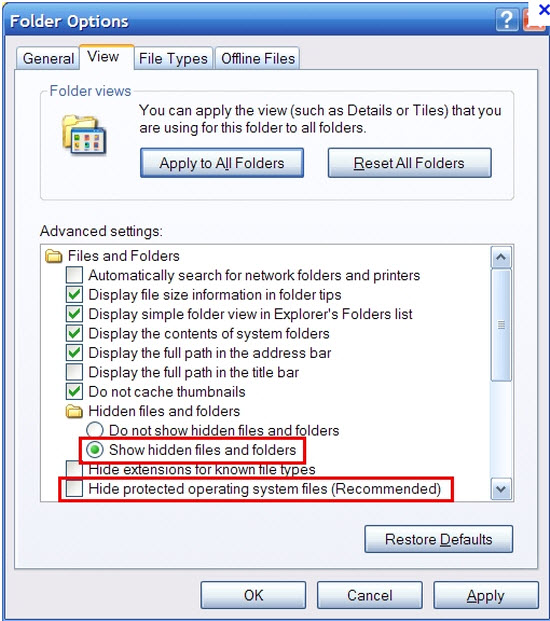
3. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
4. Delete all the malicious files related to this hijacker manually.
%AppData%Local[random].exe
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\*.exe
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main StartPage
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
The Search.safefinderformac.com add-on is just a browser hijacker that can cause all kind of trouble for a computer user, especially for Mac users. If you don’t consider a program that get itself installed on your system without making you informed as safe, if you have your own well accustomed and reliable search engine and never expect to experience any inconvenience caused by a replacement like the Search.safefinderformac.com, if you are a prudent computer user as we mentioned above in this article, if you don’t feel easy or secure to get yourself exposed to a questionable service provider like the Search.safefinderformac.com, you are strongly recommended to completely and seriously get rid of the Search.safefinderformac.com from your computer no sooner than you find it on your browser anytime. And manual removal is more suggested to thoroughly deal with this hijacker. An expert in the field of virus removal is both your best choice and our best recommendation.
Note: If you have little knowledge about computer and do not know how to operate the removal, please contact experts from YooCare Online Tech Support for further help.
Published by on November 23, 2016 6:25 pm, last updated on November 23, 2016 6:25 pm



Leave a Reply
You must be logged in to post a comment.