Hello. Is somebody there? I need help. Here is my problem. My Google Chrome is infected with a piece of malware named Yourwebing.com browser hijacker. It compromises my by browser and makes a big change on it. Every time I start Chrome, I see Yourwebing.com instead of the homepage of Google. I didn’t pay much attention to it in the beginning as I thought that it was one of Google’s components. However, this search engine provides useless and weird information. I always have been forced to visit websites that I am not familiar with. My computer runs slow. But I don’t know how to remove this malware. Is there a way that you can help me fix the problem here?
Yourwebing.com browser hijacker is one of the unwanted ad-supported programs. Once it infects your browser, it replaces your homepage and installs plug-ins to support itself without your knowledge or permission. At the first sight, you may think that it is a useful domain just like Yahoo and Google search engine. Until one day, you find that something goes wrong. Frequent website redirects and endless pop-up ads will have your attention. We need to tell you that Yourwebing.com is not a normal search engine. According to the report, its developers create it as a tool to promote related products. For this reason, ads about their product will pop up on your computer all the time. Though you don’t want to visit ad websites, Yourwebing.com browser hijacker will redirect you to its sponsored websites without giving any hint. A bunch of useless programs will be installed to damage and slow down your computer. If your browser is infected, we suggest you remove all related files of Yourwebing.com out of your system as soon as possible.
Yourwebing.com pretends to be a useful search tool to achieve your trust. It hides itself deep in your system which makes it very difficult for you to detect with your naked eyes. In fact, it performs malicious activities on computer instead of enhancing your browsing experience. For marketing purpose, it monitors your online activities aiming at your precious information. It spares no effort to collect information on your browser which is very important to their product. It mainly targets on your browsing history and private information you enter on the browser. Later, the collected information may be sent to the remote developers. At the same time, it changes your default browser settings arbitrarily. You may find that your homepage is turned into Yourwebing.com or other suspicious domains. Special code is written to prevent you from replacing it. It will allow you to change the settings. Or, it allows you to change it in the beginning. However, it changes Yourwebing.com back soon in order to make sure that it will always run when you launch the browser. When you try to look for information on the Internet, you will find that search results supported by Yourwebing.com are full of ads and have nothing to do what you need. Most of them are ads. They will redirect you to the sponsored websites. Once you click on the website, its developer gain money. Though they are websites that display ads, not all of them are reliable. Some of them may have been hacked and carry malware. You must be careful with those websites. Tons of annoying ads supported by Yourwebing.com will pop up after you connect your computer to the Internet. In this way, its ads have been widely read as you may click on it accidently while you are trying to close the ads.
No.1: illegal movies or music. You may note that lots of illegal movies and music demand a certain media player. The website provides link to download the software, but you need to be careful. The malware like this browser hijacker is embedded in the downloaded software on behalf.
No.2: pop-up ads. The cyber criminals usually design the browser hijacker programs very well and make them pop up in an attractive form. We have to tell you that unexpected clicks on suspicious links or pop-up ads may install this nasty browser hijacker on your computer.
No.3: malicious Trojan programs. Most of the Trojans are spreading via malicious software nowadays. Users who access these malicious programs in conjunction with Trojan virus will severally got infected with this browser hijacker.
No.4: ad-supported programs. Many people would like to download free software from the Internet. You should know that browser hijacker program usually is bundled with free software and shareware. It will be installed along with this kind of software as a plug-in. Cancel the plug-in installation to avoid unwanted programs.
1. Clean Add-ons and Extensions
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
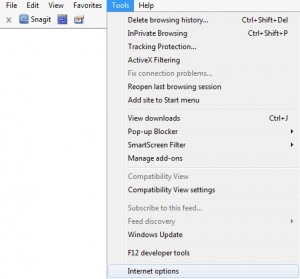
(2). Click Programs tab, click Manage add-ons and disable the suspicious add-ons

* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
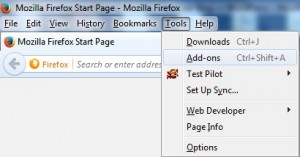
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
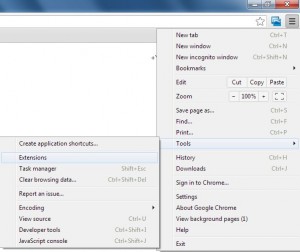
(2). Disable the extensions of Yourwebing.com
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
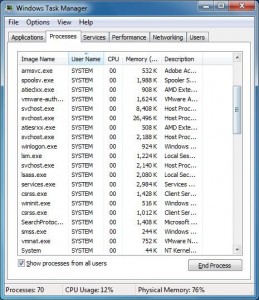
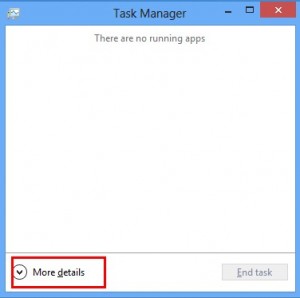
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
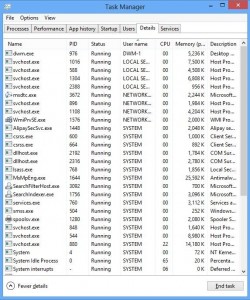
(2). Find out and end Yourwebing.com’s processes
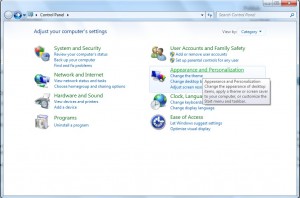
3. Show Hidden Files
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
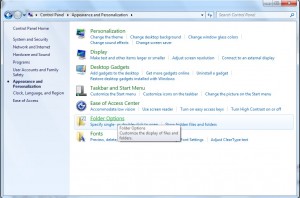
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
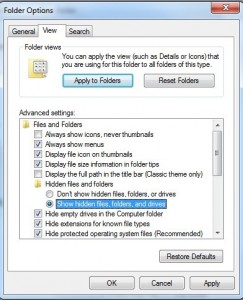
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
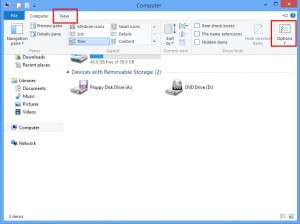
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category

4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to Yourwebing.com through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
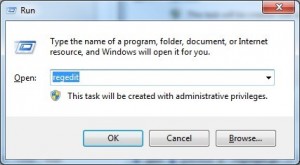
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
To sum up, Yourwebing.com is very tricky. It helps its developer generate revenue in a nasty way. Never trust it and leave it on your browser. If Yourwebing.com stays on your computer for a long time, more and more unwanted programs will be installed. When it installs useless programs on your computer, it does not provide an option to uninstall it. If you right click on the icon of useless software to open file location, it only shows your browser app, such as Google Chrome, Safari, Internet Explorer or Microsoft Edge. You just can’ find the target one. The most important thing is that you must be careful with pop-up ads caused by Yourwebing.com and websites you are redirected to. They may bring you viruses in any minute. Besides, we can’t guarantee that this browser hijacker will not be able to access your bank card detail that you used to do shopping online. Hence, stop it right now. Locate all files of Yourwebing.com and delete them one by one.
Published by on July 28, 2016 5:50 am, last updated on August 26, 2016 9:13 am



Leave a Reply
You must be logged in to post a comment.