This morning, I was told that my computer got hacked by Search.youremailhub.com virus. I was shocked. Why did I get this virus into my computer? The most important thing is that how I get rid of this virus from my computer right now? None of my antivirus program can make it worked! Please help!
Search.youremailhub.com can infect all kinds of browsers (i.g. Internet Explorer, Google Chrome, Mozilla Firefox, Safari etc.) on your computer after it gets into your computer. This virus may get into your computer secretly. So, when you notice this virus, it is on your computer. All your browser settings will be changed automatically. All the default homepage on your browsers will be modified as Search.youremailhub.com without your approval. Countless advertisements and pop-ups will be showing on your computer screen so as to take up a large percentage of your computer resource. Hence, this browser hijacker must be eliminated as early as you can when you find it making chaos on your computer.
Search.youremailhub.com may get into your computer, when you download some applications and problems from some unfamiliar websites, which you think it is for “free”. When you click on a unknown websites and links, you may get the virus into your computer. Besides, when you read the junk emails as well as its attachments, you may give the chance for the virus entering your system. Once this virus infected your computer, your computer may act unusual. Otherwise, it will take over your online activities immediately. Then it will change your system setting like your browser settings as well as DNS settings. Your default homepage will be changed to its domain, so that it can monitor you to its domain when you start to go online. Later then, countless of ads and pop-ups will come into your computer and then take a large part of your resource. The performance of your system will be infected so greatly. You may find that your web page keeps crashed or stuck so frequently. Search.youremailhub.com must be removed as soon as possible before it messes up your whole computer system.
1. It can be added to Internet Explorer, Mozilla Firefox or Google Chrome browsers without your notification.
2. You are rerouted to some unknown sponsored websites that you have never seen before when you surfing online.
3. You can get a bunch of popup ads show on the webpage which you are browsing.
4. It can be installed on your computer slightly.
5. This browser hijacker can introduce various infections and unwanted programs onto your system,
6. It can investigate your browsing behavior and gather your input information online.
7. It is also responsible for collecting computer user’s private information like IP address and online traces for unethical using of online marketing.
Note: If one of symptoms mentioned above is found in your computer, then you must know that your computer is being attacked by the browser hijacker. Since the browser hijacker is so dangerous, once your computer is infected, you should take actions to delete the hijacker. If you are not a computer expert, in case you lose your important data or damage your system, please welcome to contact Yoocare/Yoosecurity Online Expert for help now!
Search.youremailhub.com Hijacker hijacks your default browser to redirect your web search results and modifies your default homepage and browser settings. Manual removal is the most effective way to completely uninstall it from an infected computer’s operating system, for the season that this hijacker is so cunning and dangerous, antivirus programs cannot get rid of it permanently. Here are the manual guides for users to remove the annoying hijacker.
1. Clean Add-ons and Extensions
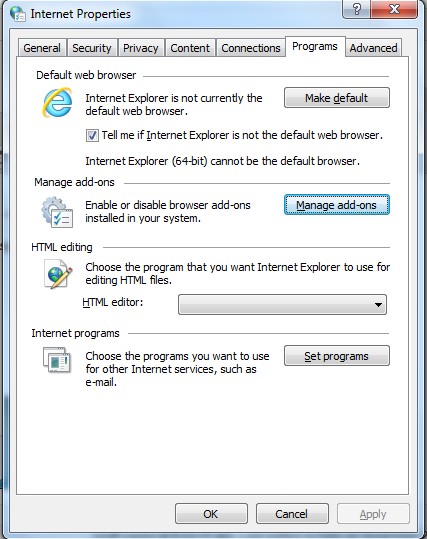
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
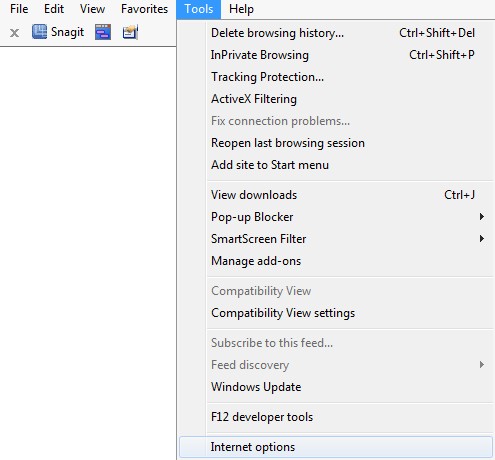
(2). Click Programs tab, click Manage add-ons and disable the dubious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
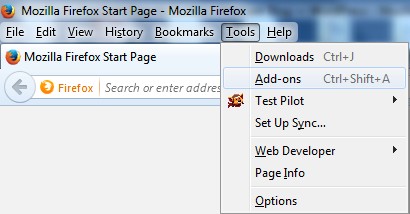
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
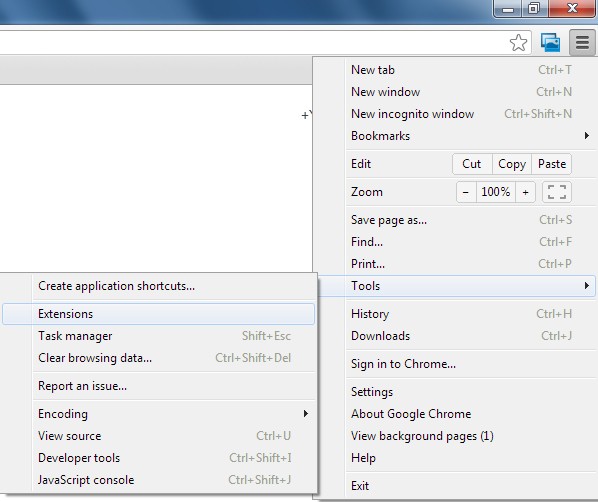
(2). Disable the extensions of this virus
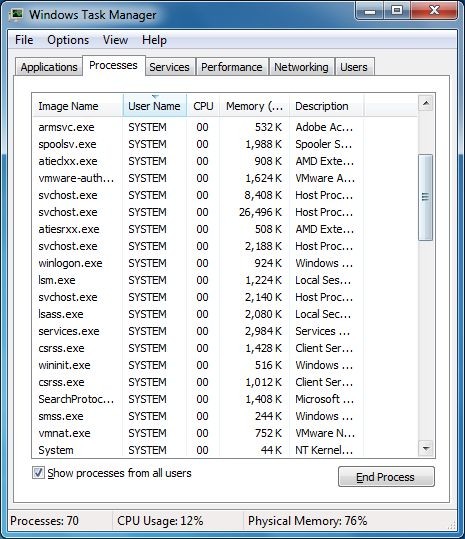
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
*For Win 8 Users:
Click More details when you see the Task Manager box
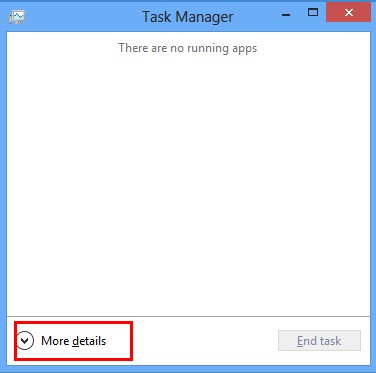
And then click Details tab
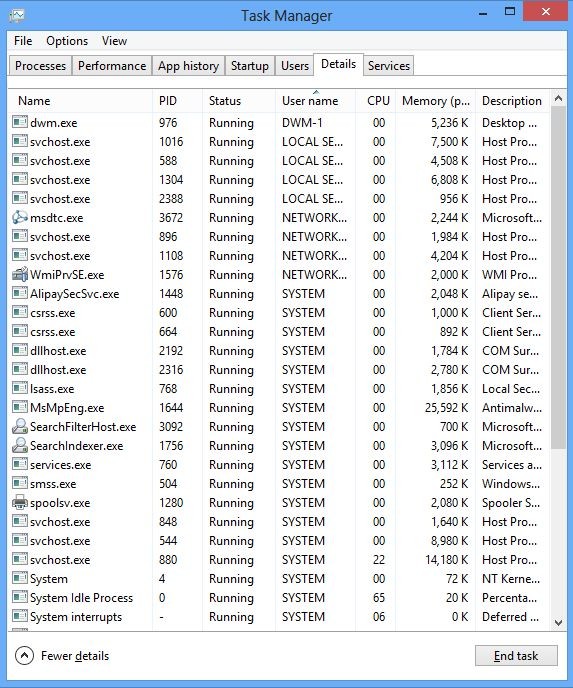
(2). Find out and end this hijacker’s processes
3. Show Hidden Files
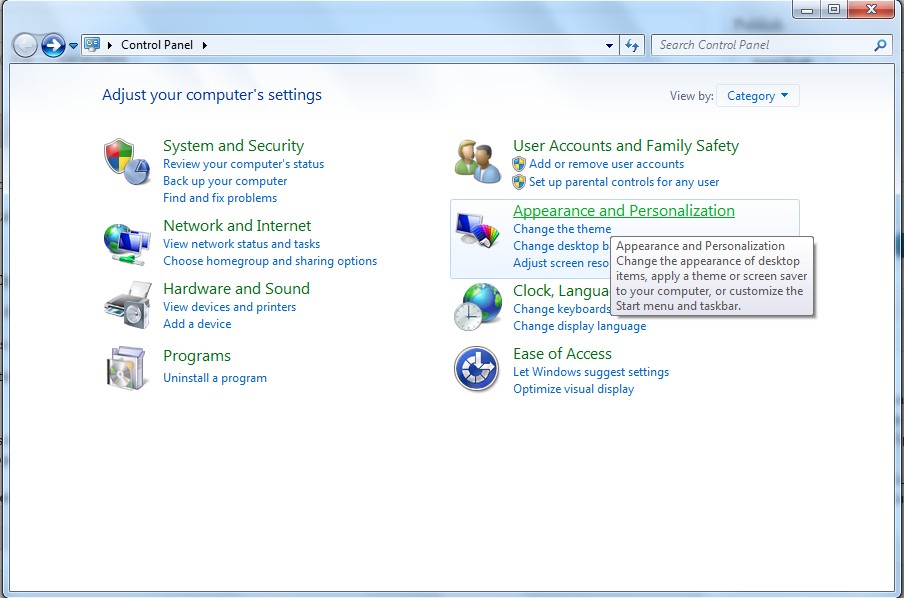
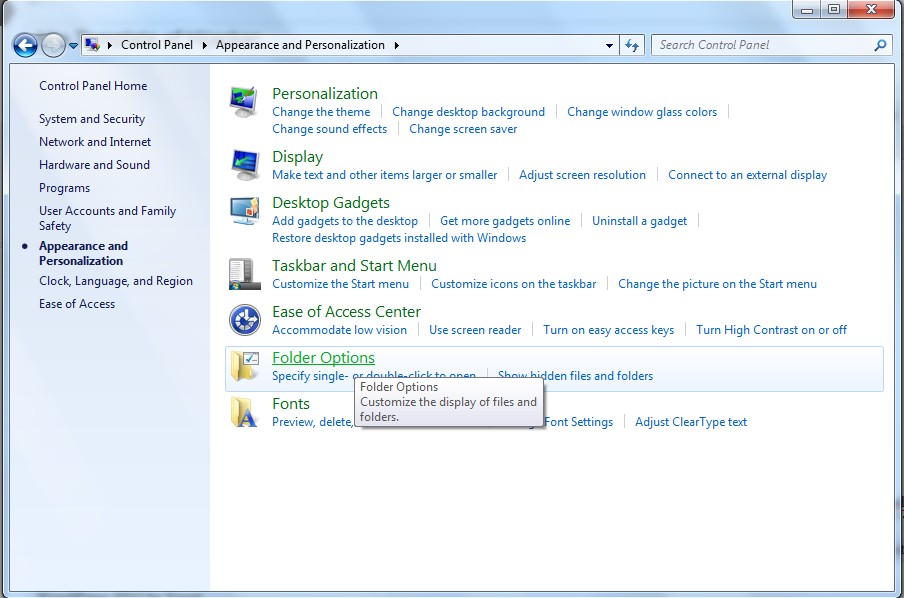
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
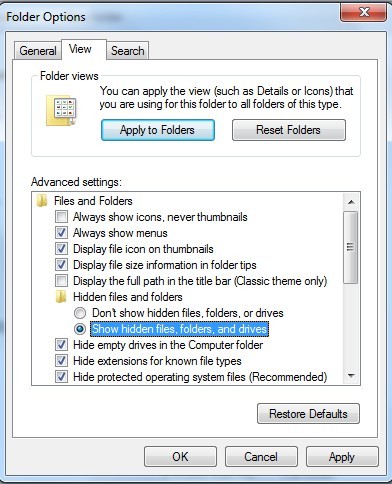
(6). Click OK at the bottom of the Folder Options window
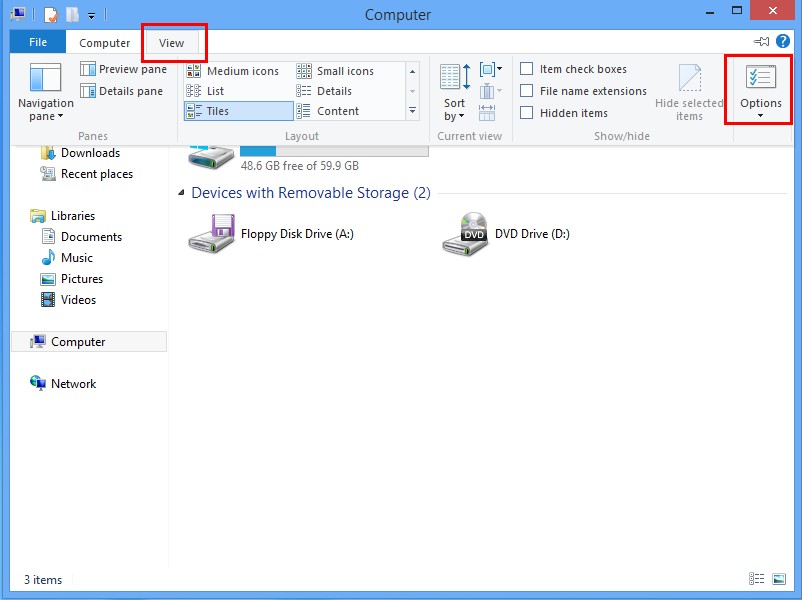
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
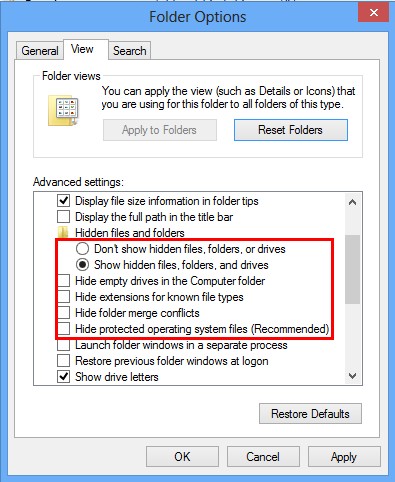
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
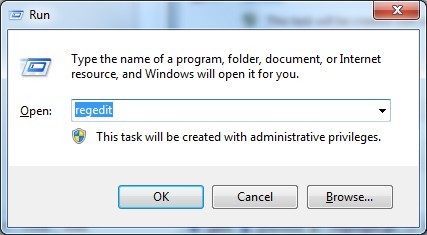
(1). Delete the registry entries related to this browser hijacker through Registry Editor Press Win+R to bring up the Run window, type “regedit” and click “OK”
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe %AppData%\Roaming\Microsoft\Windows\Templates\random.exe %AllUsersProfile%\Application Data\~random %AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Conclusion
Search.youremailhub.com is dangerous and annoying browser hijacker which is responsible for displaying lots of pop-up ads on your infected computer. Once it infected your computer, it has the ability to allow unwanted applications installed onto your computer without your permission. Your computer system will be frozen or black-out with a sudden. You can’t use your programs normally at all. It may inform your variety of fake security alerts, exceptions and warnings. The most important thing is that it is capable of pilfering your sensitive data by tracking your cookies and browsing habits. This infection will be a great threat to your computer security and privacy. It is strongly recommended to remove this infection from your compromised computer immediately.
Suggestion: The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on May 6, 2016 6:42 am, last updated on May 6, 2016 6:42 am



Leave a Reply
You must be logged in to post a comment.