Need help removing computer encryption scam virus! It encrypts all of my photos, videos and important business documents asking for $500. Luckily, I backed up all of my important files last Friday. I still have them on my external disk. But the problem is that I have no idea how to remove this virus in a safe way. I need computer experts’ help. I am not willing to put my files back to computer until I get this evil virus removed.
Computer Encryption scam virus is a recent computer threat which corrupts users’ important files. It is different from those fake police scam viruses. It does not try to convince its victims that their device is involved in using copyrighted content or initiated other illegal activities on the Internet. Instead of blocking user’s computer system, it encrypts user’s sensitive files, like photos, videos, documents etc. To get your files back, you need to pay $ 500 or $1,000 ransom via Moneypak, Ukash, or Bitcoin. Do not pay ransom to the hackers. There is no guarantee that your will get a decryption code for your files. This type of virus mainly targets on businesses. As we all know, business files are very important and precious. Business file lose can cause huge financial lose. You need to protect your files well. Also, you can back up your precious files frequently in case computer encryption scam virus attacks your computer. This type of virus becomes common in those days. You ought to stay alert to keep your private files safe from virus.
On one hand, computer encryption scam virus is widely spread via spam. The hackers design the spam with virus attachment like an official email from a reliable company, like Amazon, eBay etc. It usually states that you failed to go through a payment, taxes process or other similar activities. You need to click on the given link or attachment to sort things out in time. Do not trust those messages. You should have a second thought. Did you hear of those companies before? Did you have a business with those companies? Are those companies reliable? If your answer is “No”, do not click on the link, or it will redirect you to malicious websites and pick up virus. Besides, attachment from a spam contains virus itself. If you open the attachment, you are installing a virus. On the other hand, fake pop-up is another form of tool that the hackers use to trick people into installing program with computer encryption virus. Malicious pop-up bought by browser hijacker may tell you that your Java, Flash Player or other applications are out of date. To enjoy the convenience of the latest version of that application, it invites you to click on that notification to download. We do not suggest you do this in a rush. You ought to figure it out if this message is from the official website. Typically, official message from Java, Flash Player or other applications will not pop up suddenly from unknown websites. You had better update your applications when your security program informs you. Those fake notifications are asking you to download virus to install. It is not a regular application at all. It is very important for you to note the transformation of computer encryption virus and prevent it effectively. Therefore, keep this information in mind.
Computer encryption scam virus is pretty aggressive. This type of virus will not block your system because you can access your system and remove the virus in safe mode which makes it difficult for the cyber hackers to steal money from you. The cyber hackers just change its function. After this virus sneak into your system, it scans your computer system and chooses predetermined files to encrypt. To make it effectively, your business files, precious photos and videos are its main targets. After it encrypts your files, it displays a warning telling you that your files have been encrypted. It asks for ransom to restore your files within 48/72 hours. Otherwise, the decryption code for your files will be destroyed. According to our customers, sometimes, the hackers just do not give up after the 48/72 hours run out. They double the ransom. If computer users do not pay $500 as it requires, the ransom will increase to $ 1,000. As the virus says, you are not able to access your photos, videos and other important files. However, you should not pay ransom following its guide. Do not support the cyber criminals by giving them money. They will continue to attack other people’s computer to make more illegal money. You must stop them now. Ignore this warning and remove the computer encryption scam virus as soon as possible instead of paying non-existed ransom. In addition, this virus can enable your regular programs including your security program. In this way, you are allowed to remove this nasty virus with the help your security program. Manual virus removal is the most effective method by now. You can locate all the related files and delete them one by one.
Removing the computer encryption scam virus seems to be difficult for ordinary computer users, even those famous antivirus programs cannot do that successfully. Hence, manual removal can ensure that the stubborn virus will be gone completely. As mentioned above, manual removal needs professional knowledge, because the lack of experience may cause errors resulting in some other unpredictable problems. The following guide provides a general concept of the removal. You may not be able to find out some certain files for the virus can be changed. If you fear the loss of important data, please consider making a backup before starting the computer encryption scam virus removal.
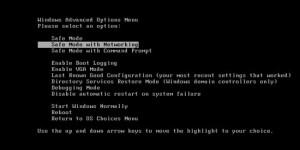
1. Restart the Infected Computer into Safe Mode with Networking
(* Usually the malware will be temporarily disabled in Safe Mode which will provide users a chance to get this problem fixed. If you are still getting the virus popup in safe mode with networking, please try safe mode with command prompt instead.)
Restart your computer, immediately, quickly and repeatedly hit F8 key before the Windows start-up screen shows. Select “Safe Mode with Networking”, and then press Enter key.
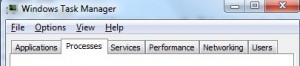
2. Stop the Processes Related to computer encryption scam virus in Windows Task Manager
Press Ctrl+Shift+Esc keys together and end the virus processes in the Processes tab of Windows Task Manager.
3. Show Hidden Files
(1). Press Win+R to get Run window
(2). Type Control Panel in the Run window and hit enter to get Control Panel
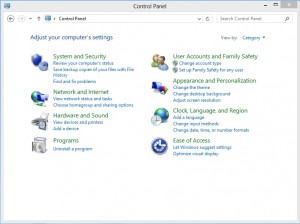
(3). Click on Appearance and Personalization
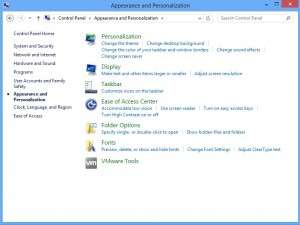
(3). Click on Folder Options
(4). Click on View tab in Folder Options window
(5). Tick Show hidden files, folders, and drives under Hidden files and folders tab

(6). Click Apply to take effect, then click OK at the bottom of the Folder Options window
4. Delete Virus Files
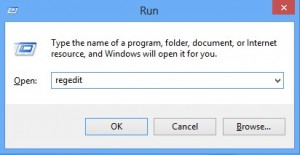
(1). Using Registry Editor to delete or adjust all the related registry entries of computer encryption scam virus
*Guides to open Registry Editor:
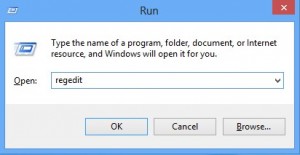
Press Win+R key together to get the Run box, type in ‘regedit’ then click OK, Registry Editor window will pop up
(2). Find out and remove the associated files of this fake Antivirus
Computer encryption scam virus is much more complicated than you can image. It is almost impossible for you to restore your encrypted files. Luckily, this virus is not able to infect the files that you backed up before. You can just remove the virus completely and place your backup files back to your computer. Virus infection is very common in this hi-tech society. Who knows which day your computer will be infected with virus unexpectedly. It is a wise choice to back up your important files as frequently as possible. You can store your files without connecting them to network which will definitely keep them away from virus infection. If your precious files have been encrypted unfortunately, remove computer encryption scam virus completely right! Do not leave it on your computer to encrypt more files!
Published by on April 16, 2016 6:08 am, last updated on May 26, 2016 8:34 am



Leave a Reply
You must be logged in to post a comment.