My computer got a nasty Trojan named Backoff yesterday. Now numerous ads pop up when I surf the internet and the computer runs extremely slow. My Norton cannot get rid of this Trojan virus. Even though I have tried many ways to try to delete it but I failed. Will this virus corrupt my personal files or do other harmful activities? I am frustrated and I want to see if there is anything other way to deal with this hateful Trojan once and for all. I would appreciate any help you can offer!
Backoff is categorized as a malicious Trojan horse which is able to invoke various harmful traits to the target computer. Once the invasion of your computer is accomplished, the Trojan virus will mess up your computer rapidly. For instance, it can change the settings of the system and you will get tons of rubbish ads constantly when you go online. It can also degrade your computer’s performance and the computer runs extremely slow. In addition, the creepy Trojan would redirect you to some commercial websites which promote online sales by displaying malicious pop-up ads to annoy your online activities. Furthermore, Backoff has the ability to provide a back door for remote IRC server and let the cyber criminals access to the infected computer to steal the stored files and privacy information. As a matter of fact, it is propagated on your computer if you visit suspicious web sites, read Spam email attachment, download freeware or fake anti-spyware program using infected media or USB devices and etc.
Once Backoff gets installed successfully, the system would become very vulnerable because the Trojan can make full use of the loophole of the system to help other infections such as spyware, malware and more redundant files to invade your computer. It would often consume your system space by dropping many unwanted files to the system and the computer may even get stuck as all the CPU resources have been eaten up. This Trojan virus can stay tough in the infected computer so it takes a long time to open a program stored in the computer. And it is capable to start itself automatically whenever the computer system starts up and then cause many unexpected problems. Once entered in users’ computer, it is capable to monitor your browsing activities and steal precious personal information like passwords, credit card, bank account information etc for commercial use. You should take steps to get rid of Trojan Backoff immediately if you want to protect your computer.
Backoff allows cyber-criminals to break into the infected computer without being noticed and it could disable executable programs installed on your computer and cause system crash. Also it will change important settings on your computer to allow remote control from cyber criminals. Other than that, Backoff will modify your registry settings and important key value to make it difficult to be removed.
Manual removal is suggested here if the antivirus program in your computer can’t deal with it. The most guaranteed way to get rid of the Backoff without reinstalling the system or formatting the hard disk is manual removal. Here are some basic steps to achieve this point. However, removing the Backoff virus manually requires high skills in order to determine which files to delete for the Trojan infection is changing with the passage of time. You are also suggested to do a backup before starting.
1. End Relevant Processes
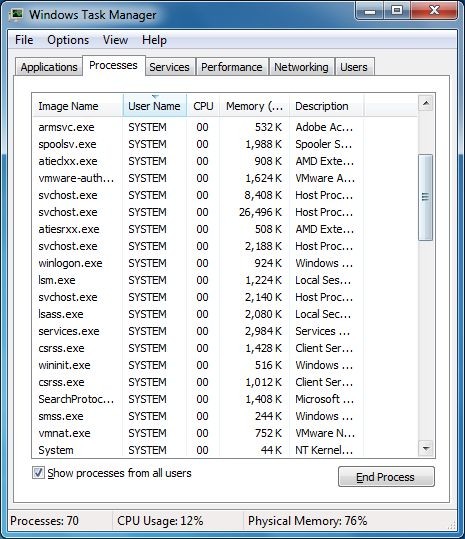
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
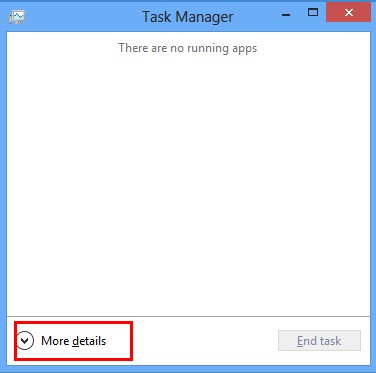
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
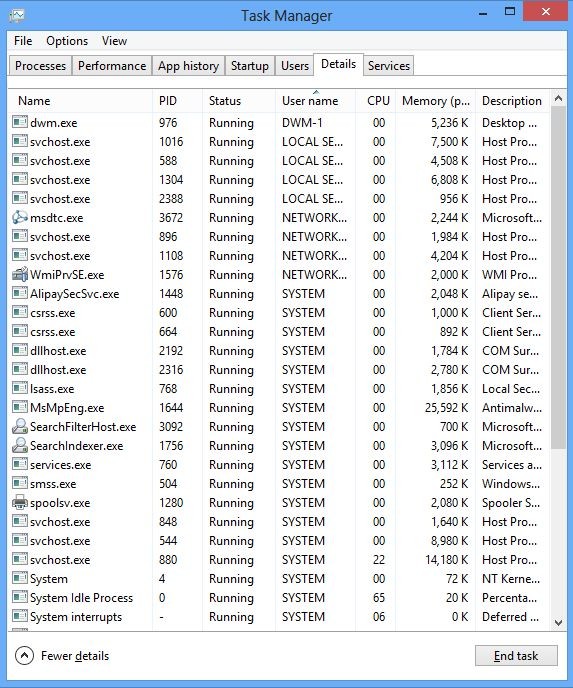
(2). Find out and end the processes of Backoff
2. Show Hidden Files
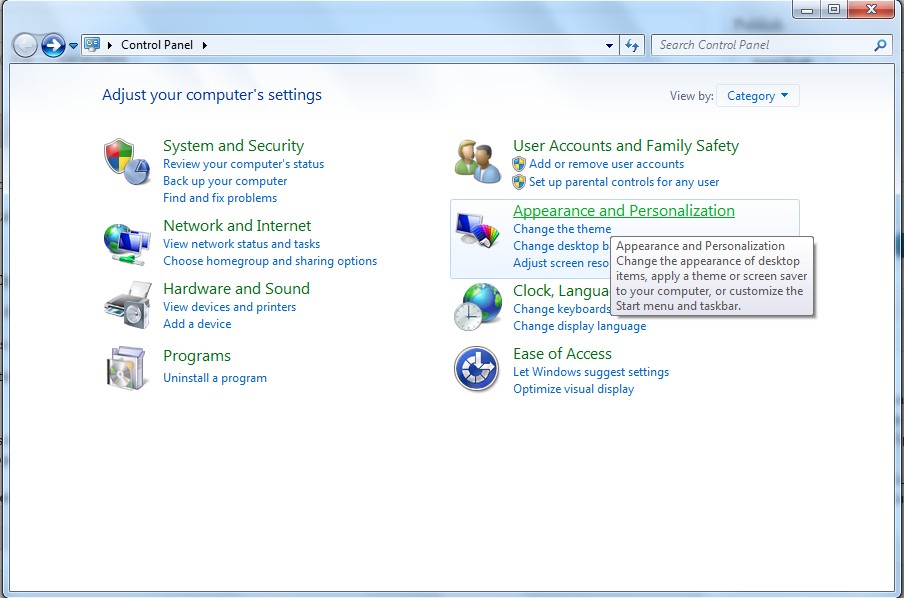
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
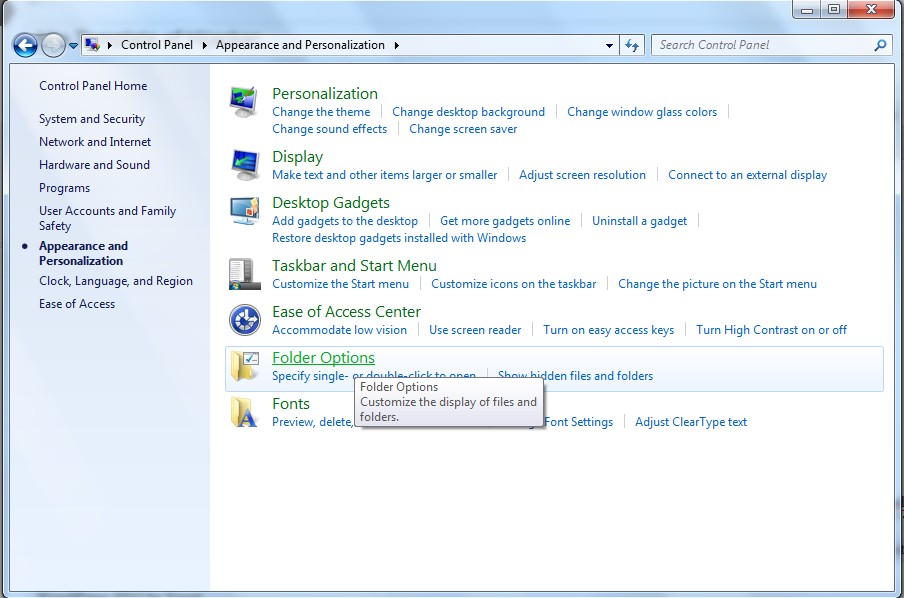
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
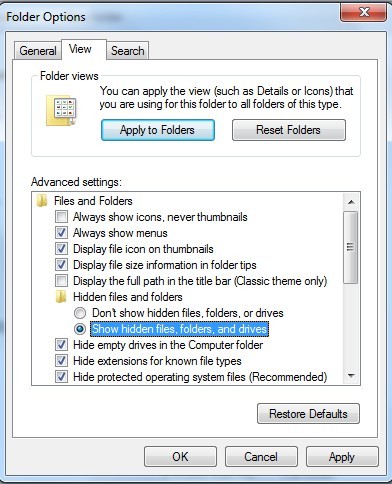
(6). Click OK at the bottom of the Folder Options window
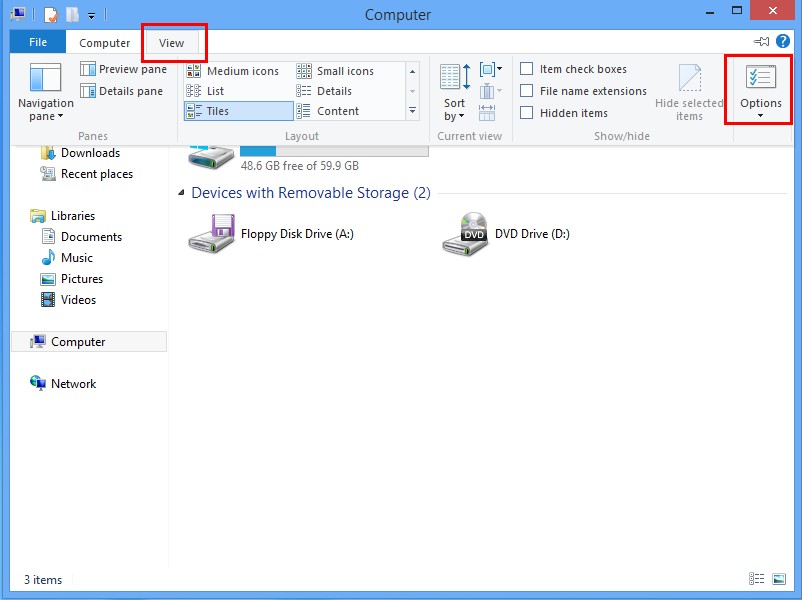
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
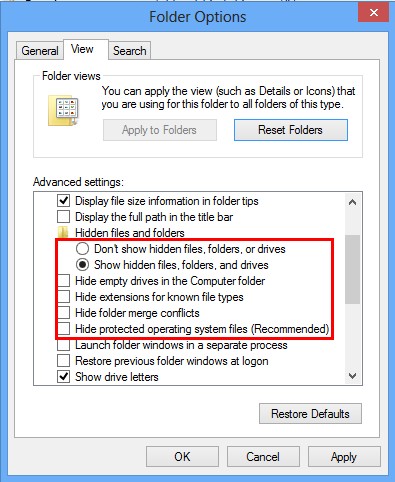
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
3. Delete Relevant Registry Entries and Files
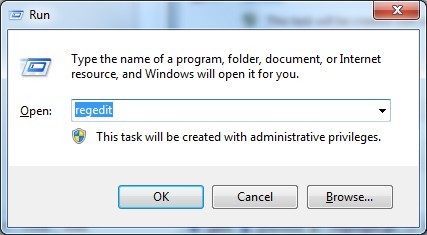
(1). Delete the registry entries of Poweliks through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
While the Registry Editor is open, search and delete the related registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\random
%AllUsersProfile%\Application Data\~random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Backoff can expose your computer to various threats by using the network vulnerabilities. For example, your PC will suffer from poor Internet connection, frequent crash of system and data files corruption. In fact it is created for allowing remote access to the infected computer by cyber criminals whose aim is to gather various key data for misuse. Once installed, it is disguised from the most anti-virus programs to bypass the detection. It is a nasty virus which can cause more damages if it cannot be removed completely. Thus, we strongly recommend you to delete the Trojan to prevent the computer system from any further damage.
The above manual removal is quiet complicated, which needs sufficient professional skills to process. Therefore, only computer users with sufficient computer skills are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on November 17, 2014 6:02 am, last updated on November 18, 2014 1:58 am



Leave a Reply
You must be logged in to post a comment.