I am unable to surf the Internet normally, because I am always being redirected to some unwanted web sites. I have Yahoo as my homepage in Internet Explorer, but now the homepage is changed into an unknown site called Worldwebfind.net. I can’t seem to get rid of this website that takes over my browser. How embarrassing! How can I make my Internet Explorer work as usual?
Worldwebfind.net seems to be a common domain like tens of thousands of other web sites. But it is indeed a browser hijacker which can bring a lot of troubles to the computer user. Yes, this special site can collect computer user’s valuable information for its developers to promote ads. Because Worldwebfind.net is widely released on the Internet, computers from around the world can be infected by it. In addition to stop you from surfing the Internet normally, it is able to modify your default homepage as well as search engine forcedly and show you a lot of unnecessary ads constantly, which is to benefit the developers.
There is an online search engine on the web page of this browser hijacker Worldwebfind.net, which seems to be able to help you get more resources from the Internet. When it gets in your computer, you can’t bypass this particular site Worldwebfind.net, because the hijacker modifies your browser settings so as to occupy the browser completely. By doing so, it tries to control your online activities. Be careful! You will be redirected to some false or even corrupted websites and the search results provided by the hijackers are unreliable. The vulnerable infected computer may also suffer from more different viruses and malware hiding in those corrupted websites. At the same time, by recording your online activities, Worldwebfind.net will help its developers benefit from analyzing your browsing history and search keywords.
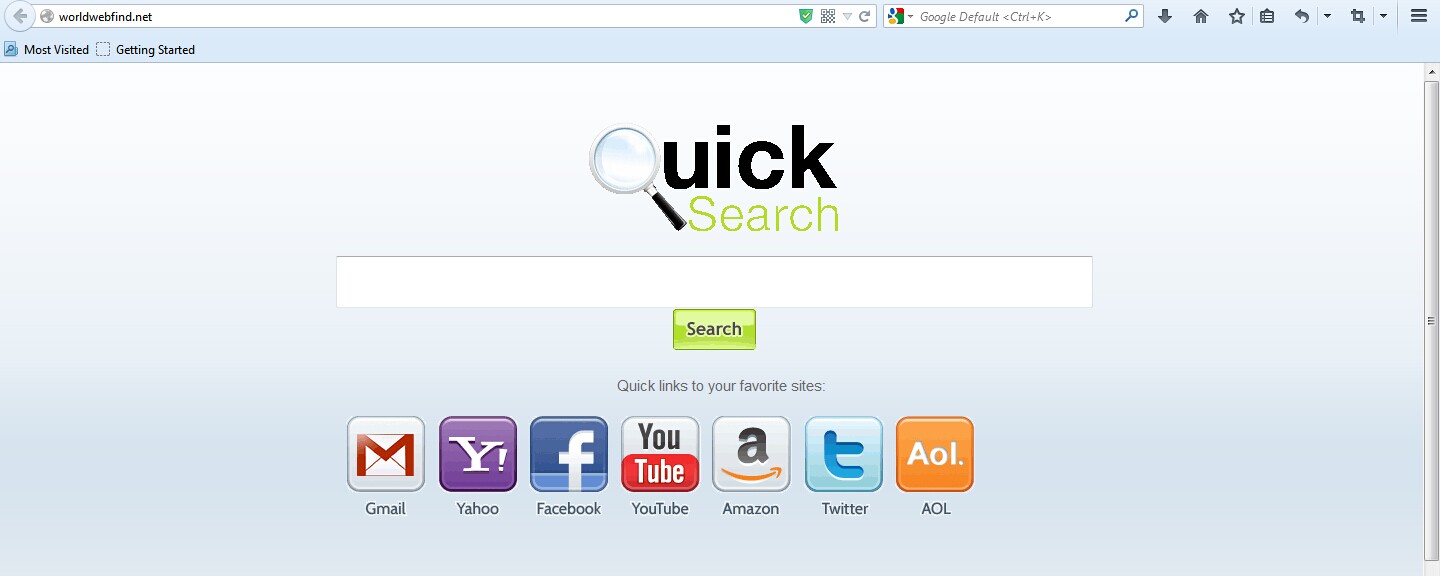
1. It is able to become the startup page of your web browser via modifying browser settings. No matter which browser you are using (Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera), you can see the browser is occupied by it completely.
2. It may also install plug-ins, extensions and toolbars in the browser so as to record your search history as well as cookies.
3. You need to wait for a long time when visiting websites because the browser always gets stuck and is slow in reaction.
4. This annoying redirect may also result in unstable Internet connection and system freezes frequently.
5. You are forced to receive many advertisement windows when the computer is connected to the Internet.
Manually removing the Worldwebfind.net hijacker is recommended here for those advanced computer users to process, because a lot of computer skills are required. If any unnecessary mistake occurs in the removal, the computer may be damaged. At the same time, the backup of important data beforehand is very necessary, if you don’t want to put them at risk. Then you can start by the following steps:
1. Clean Add-ons and Extensions
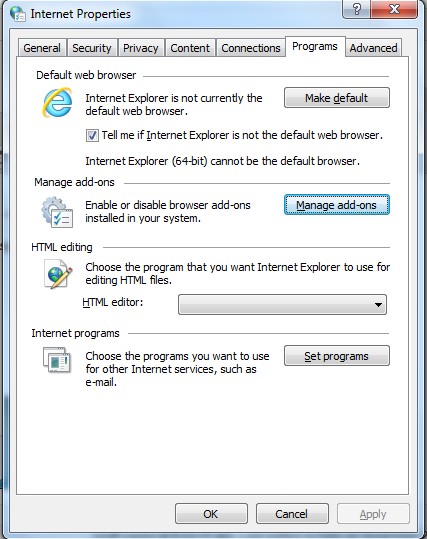
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
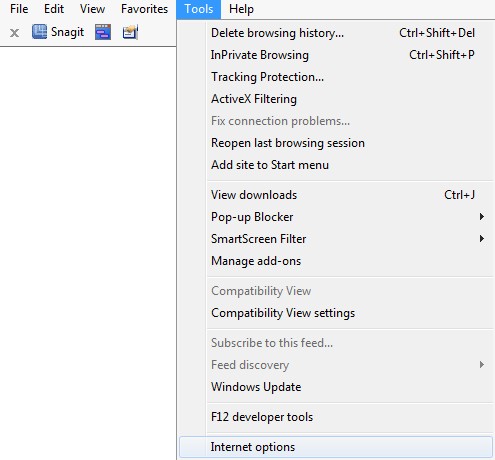
(3). Click Programs tab, click Manage add-ons and disable the suspicious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
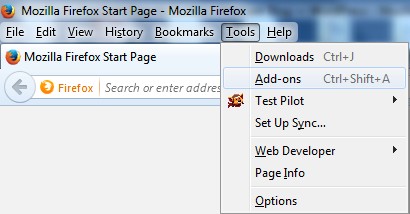
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
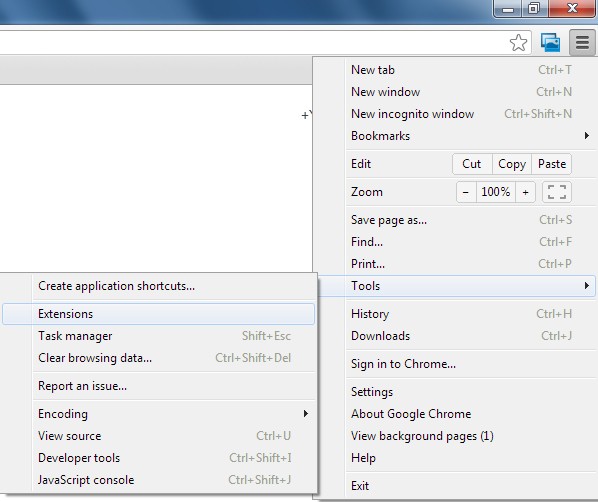
(2). Disable the extensions of Worldwebfind.net
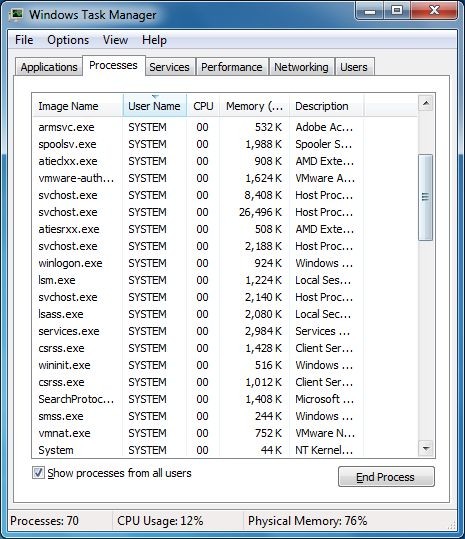
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
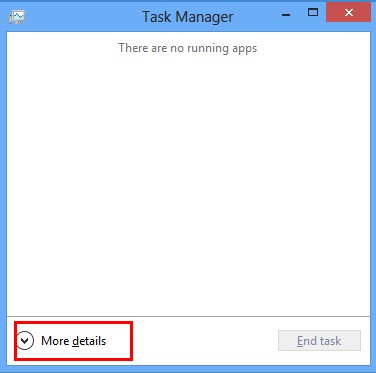
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
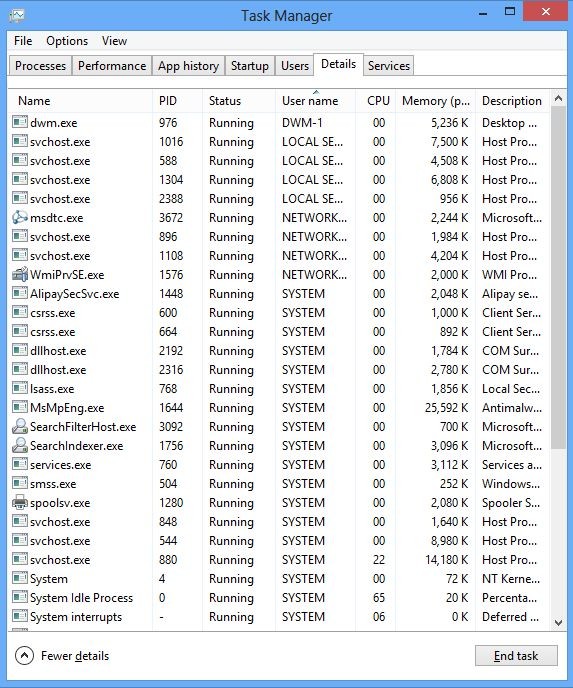
(2). Find out and end Worldwebfind.net’s processes
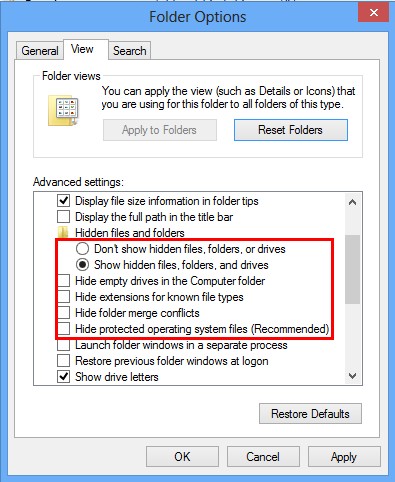
3. Show Hidden Files
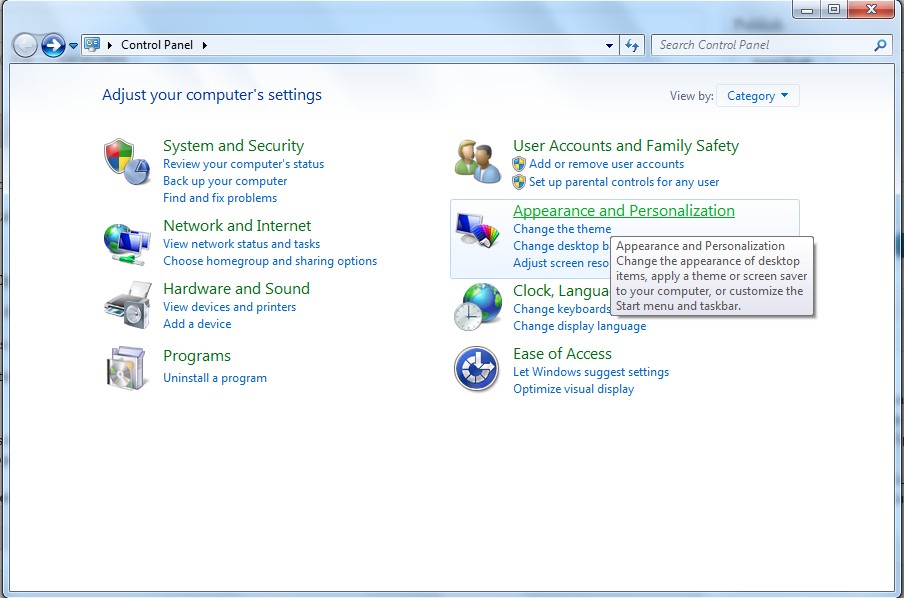
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
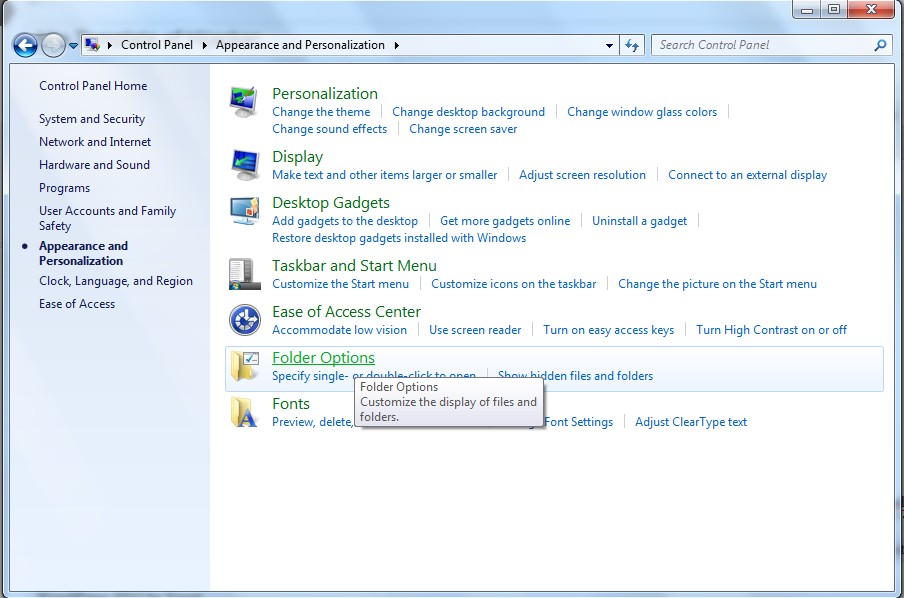
(3). Click on Folder Options
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
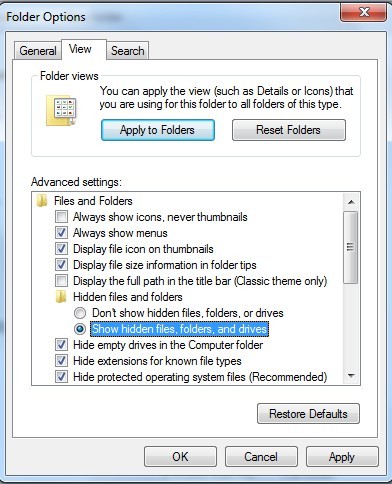
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
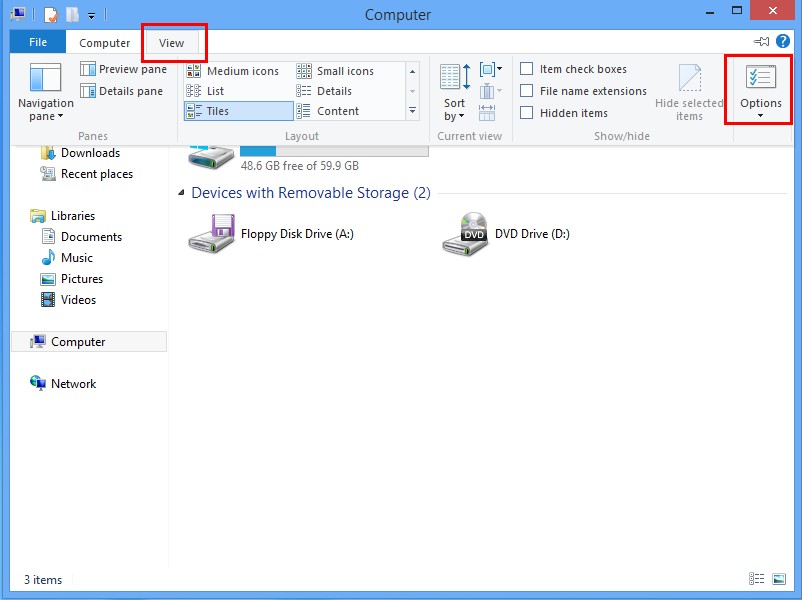
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to Worldwebfind.net through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
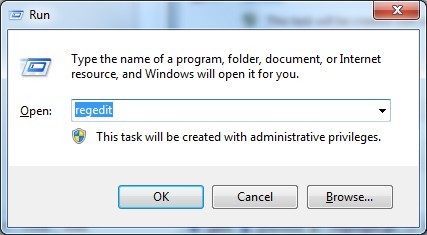
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\~random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Worldwebfind.net has the ability to escape the antivirus programs in your computer. The computer is still not 100% safe even if it has the protection from antivirus programs. You need to know that antivirus programs just can provide basic protection for computers. However, in these days, browser hijackers have the ability to continue to create chaos in many computers, because they are specially designed. There are some subjective reasons leading to the unstable environment in your computer and Worldwebfind.net will seize every opportunity to get into the computer. For example, you may have accessed to pornographic web sites or downloaded an unknown free program. Some consequences of the hijacker include: 1) the network connection is cut off every once for a while; 2) many pop-up windows appear; 3) some other malicious programs are implanted into the computer. Therefore, it is best to get rid of Worldwebfind.net as soon as possible.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on October 20, 2014 7:57 pm, last updated on October 20, 2014 7:57 pm



Leave a Reply
You must be logged in to post a comment.