You do not know why Tikotin.com always shows up as the default homepage each time you open the web browser? The default search engine is also changed? Many ads continue to pop up, which is very abhorrent but you have no way to stop them? How to remove Tikotin.com from your computer? You can have a look at this blog.
Tikotin.com is a browser hijacker that has the ability to take over your browser completely. When you open the affected web browser, it immediately shows up. Those famous browsers, including Mozilla Firefox, Google Chrome, Internet Explorer and Opera, can be influenced by it. It is usually connected to some free programs to realize mutual promotion agreement. Spam email attachments and plug-in of some unsafe sites may also contain this browser hijacker.
In addition to the browser homepage, you are forced to use Tikotin.com as the search engine to search for information. However, it can only give you some useless information, including a variety of software products and a lot of commercial ads. If you click on the ads, you will be redirected to some strange websites or activate some suspicious program downloads. This hijacker may also add some annoying applications or toolbars on your computer to slow down your computer’s running speed and occupy many CPU resources. What is more, it has the ability to collect your sensitive information through online history review. In this way, your privacy, such as bank account information and credit card password, may be acquired by some unknown guys. Uninstalling Tikotin.com in the control panel cannot get rid of it successfully, therefore, many users have no idea of what to do. Some users try to remove it by antivirus programs, but they can’t even detect it out. Hence, you should manually delete all its files and registry entries to make sure it is completely removed.
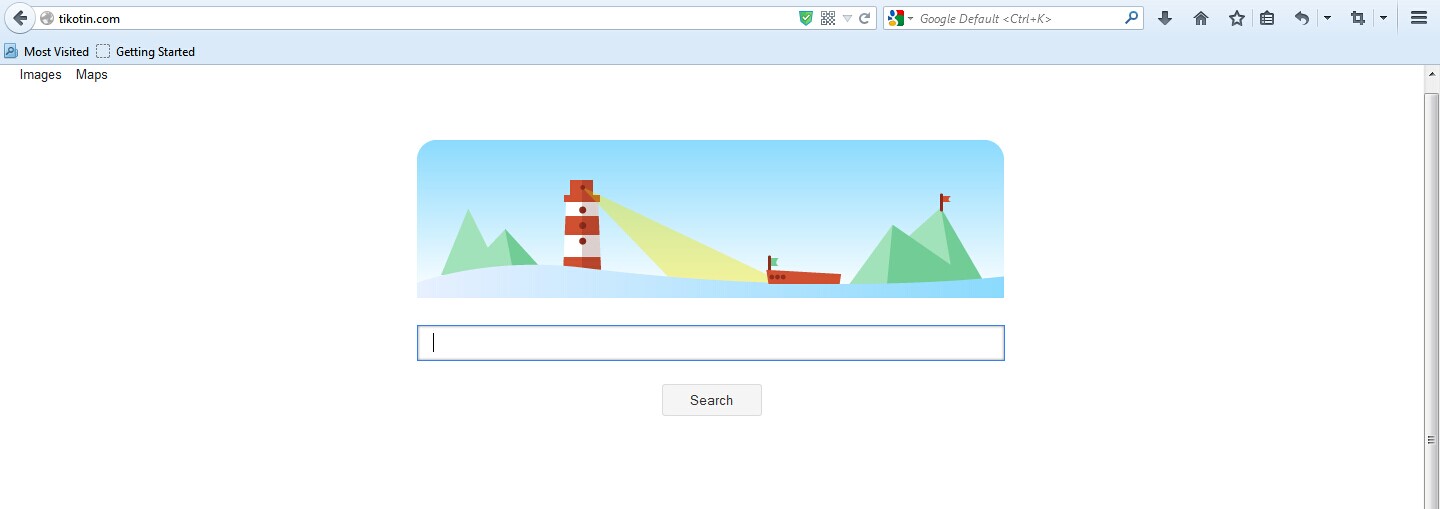
1. Tikotin.com is able to become the startup page of your web browser via modifying browser settings. No matter which browser you are using (Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera), you can see the browser is occupied by it completely.
2. It may also install plug-ins, extensions and toolbars in the browser so as to record your search history as well as cookies.
3. You need to wait for a long time when visiting websites because the browser always gets stuck and is slow in reaction.
4. This annoying redirect may also result in unstable Internet connection and system freezes frequently.
5. You are forced to receive many advertisement windows when the computer is connected to the Internet.
Do not want to experience those negative effects? Because your antivirus program fails to catch Tikotin.com, manual removal is suggested here. Please note that manual removal needs advanced computer skills and knowledge to look for variable files. Any wrong operation during the removal process may result in unpredictable damages to the computer.
1. Clean Add-ons and Extensions
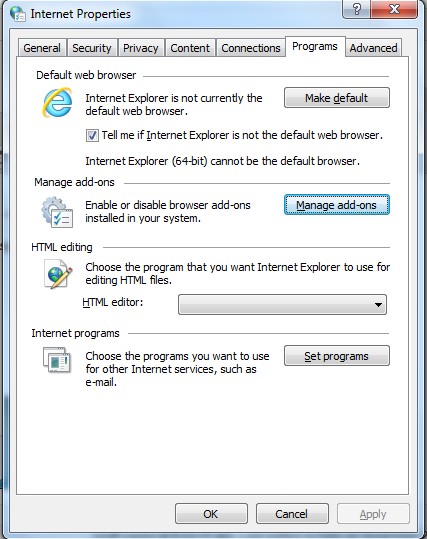
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
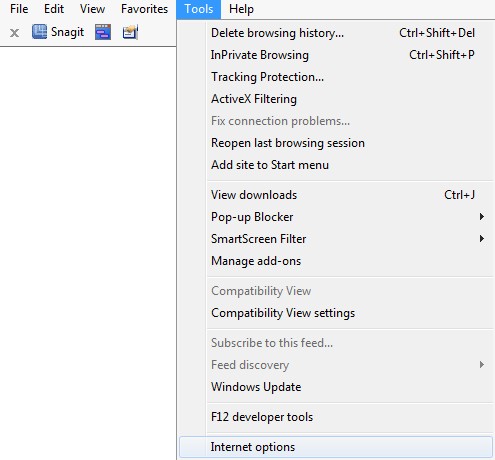
(3). Click Programs tab, click Manage add-ons and disable the suspicious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
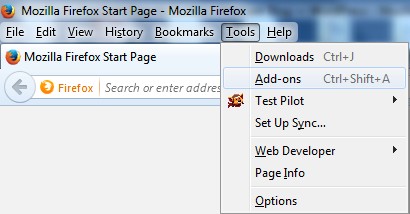
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
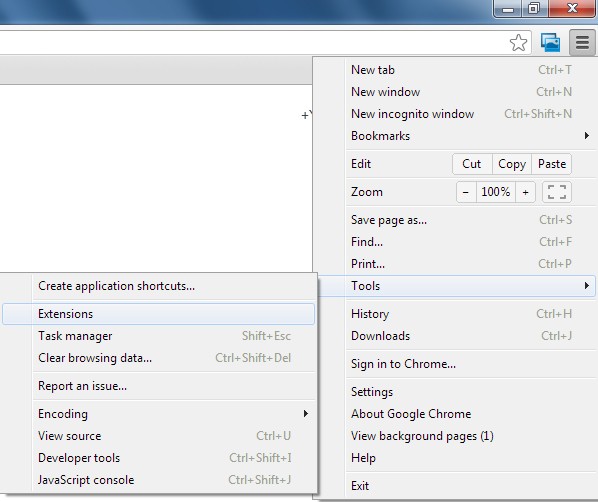
(2). Disable the extensions of Tikotin.com
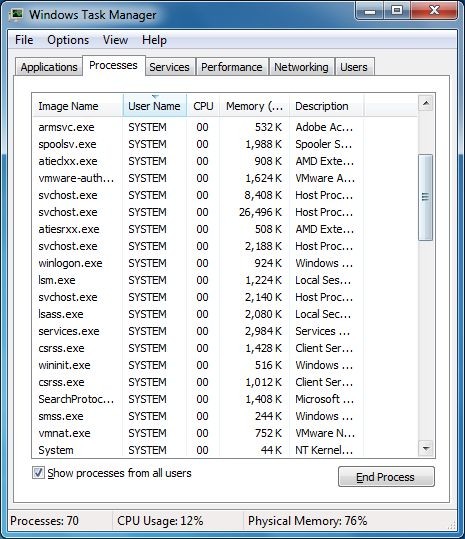
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
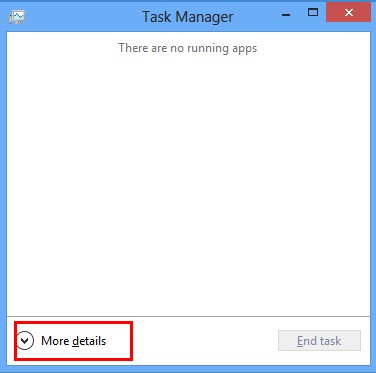
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
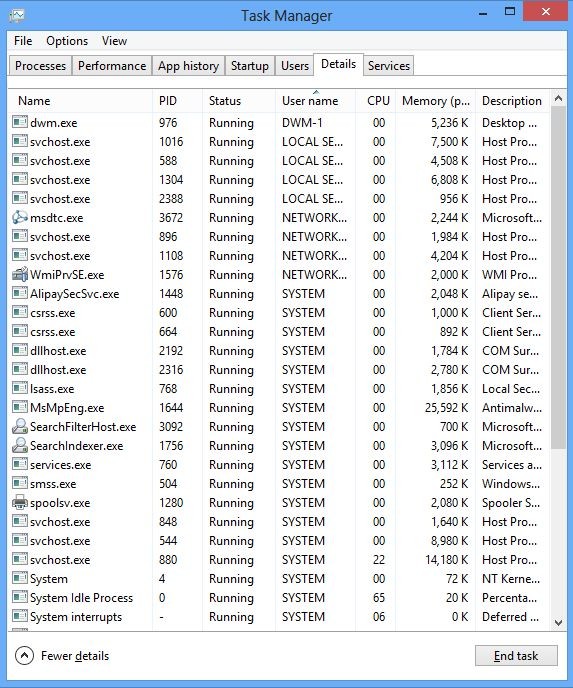
(2). Find out and end Tikotin.com’s processes
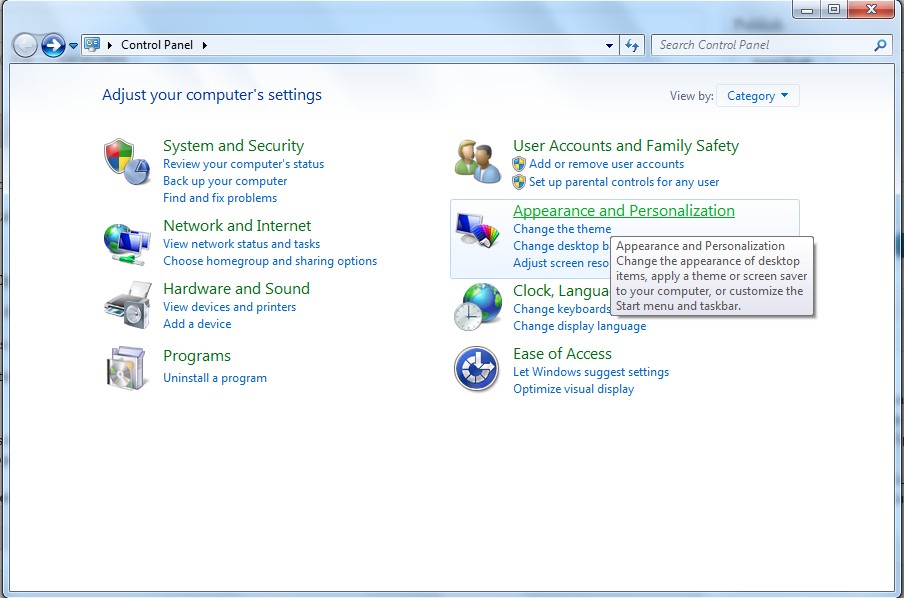
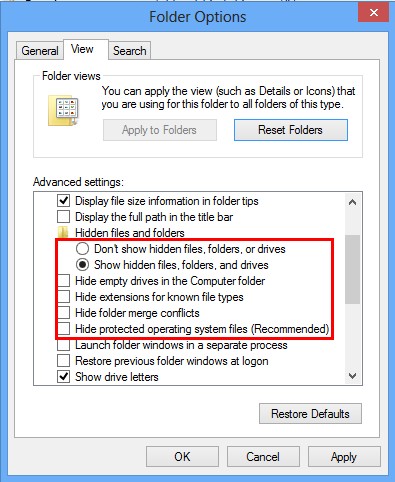
3. Show Hidden Files
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
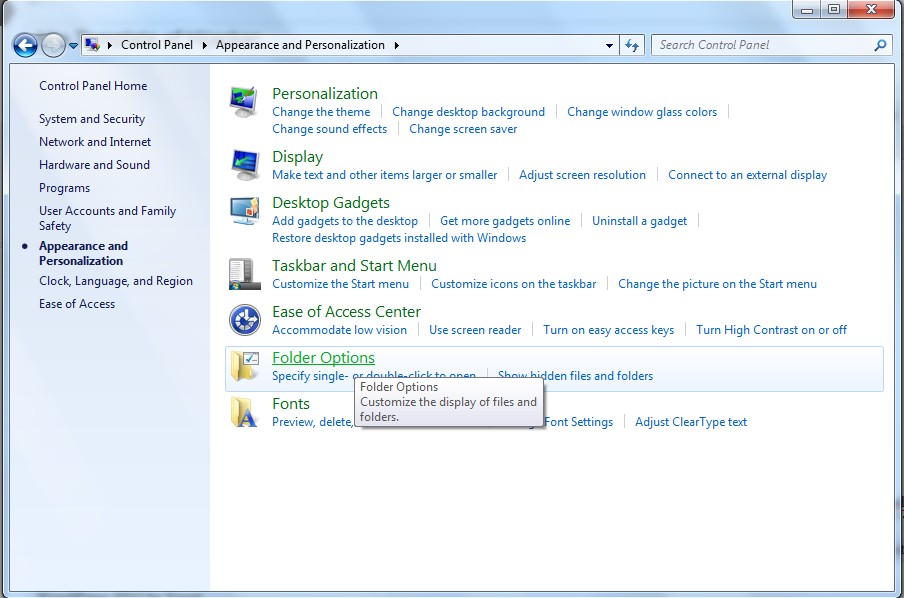
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
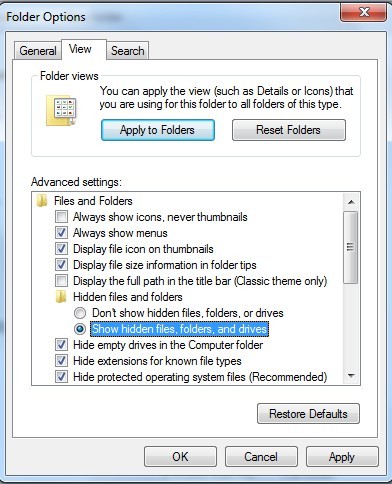
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
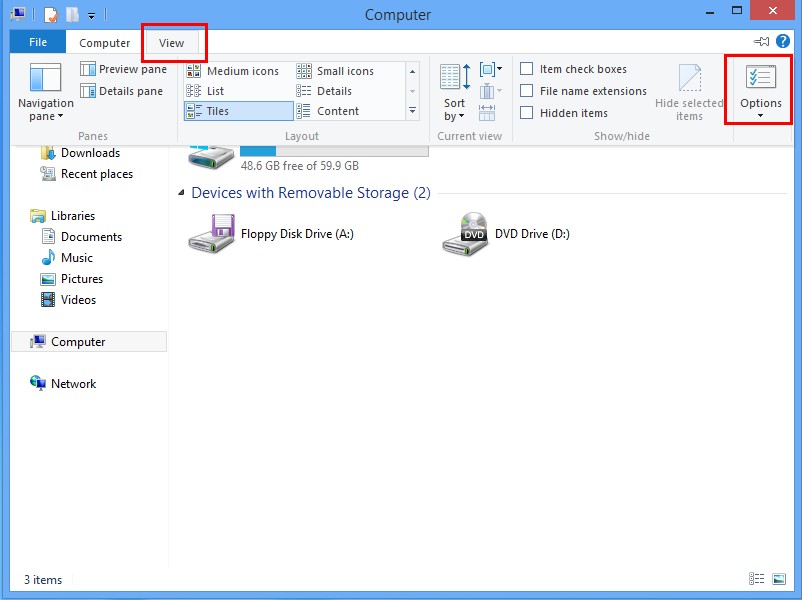
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to Tikotin.com through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
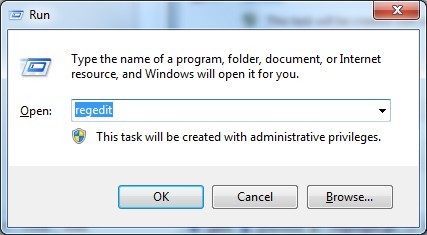
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Tikotin.com is a suspicious web site which is considered to be an unwanted browser hijacker. It mimics those legitimate and useful search engines in order to attract more computer users to use it or click on the ads on its page. Usually, opening junk e-mail attachments, accessing insecure web sites and downloading unknown free software help it to access your computer. If your computer is entangled by the hijacker, you will encounter a lot of computer problems. First of all, it changes your homepage and search engine to completely control the browser. In addition, Tikotin.com is also responsible for some other annoying problems, such as the lower computer performance and unstable network connection. The worst thing is that it may be used by the cyber criminals to master your confidential information if you let it stay in the computer for a long time. You may want to use the antivirus software to remove it. However, all attempts are futile. In this case, only manual removal can ensure that Tikotin.com will be deleted thoroughly.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on October 13, 2014 9:03 am, last updated on October 13, 2014 9:03 am



Leave a Reply
You must be logged in to post a comment.