What is Rocket Tab? Today when I tried to run the web browser as usual, I was surprised to see it appearing as my default homepage! I wanted to search for something about it by Google and Yahoo, but I was always redirected to its site. And it blocked me from visiting my favorite websites too. This nasty thing makes me feel very uncomfortable. I have tried many ways to stop it but failed. Can anyone help me with this problem? The answer is positive. Now you can read this article to learn more.
Rocket Tab is regarded as a typical browser hijacker which is used by its developers to obtain benefits online. Once installed, it redirects users to various malicious websites full of unwanted pages and you will never get the desired results. The virus has the ability to make the system become vulnerable rapidly, providing an opportunity for cyber criminals to enter into your computer in the backdoor. Once it has completed the installation on the computer, it changes the default homepage as well as search engine and destroys the system files and windows registry files of the computer. Each time you open the browser and whatever site addresses or search items you input, you are redirected to its website instead of what you really want. As a matter of fact, it increases its visiting volume and search ranking in this way.
After Rocket Tab Browser Hijacker enters your computer, it stays in the computer memory and automatically performs its malicious tasks every time you access the system. It has a great chance to intrude into your Windows PC when you visit suspicious web sites, open Spam email attachment, download unwanted freeware, use infected USB devices and etc. It may flood you with tons of pop-up ads when you visit websites. The virus has the ability to track your online browsing history and cookies like keeping track of the web pages you visit, videos you watch and so on in order collect confidential data for their evil goal. And they can disable any security tool on your computer to avoid detection and removal. Therefore, when you see this redirect on your computer, you should remove it timely in case of further damages. It is not advisable to leave it in on the computer.
1. It can not only change your web pages, but also alter other settings to add toolbars, pop-up advertisements, and bookmarks that you did not create.
2. It can modify the homepage settings of your web browser, more commonly by reducing your internet security options. And the worse thing is it prevents you from changing them back.
3. New toolbars or Favorites are installed that give you icons and links to web pages that you don’t want.
4. It may block you from visiting certain website you’d like to visit and show an error page instead.
5. It will display constant pop-up ads, sometimes in such large amounts that you are not able to close neither the ads nor the browser.

Rocket Tab hijacks your browser to redirect your web search results and changes the homepage and browser settings. To completely uninstall it from an infected system, manual removal is the first choice because sometimes antivirus software cannot pick up the exact computer threat timely or remove it permanently. Now most browser hijackers are quite similar to spyware and adware threats and therefore cannot be removed with the help of popular antivirus products. Users can follow the manual guide here to get rid of this browser hijacker completely.
1. Clear all the cookies of your affected browsers.
Since this tricky hijacker virus has the ability to use cookies for tracing and tracking the internet activity of users, it is suggested users delete all the cookies before a complete removal.
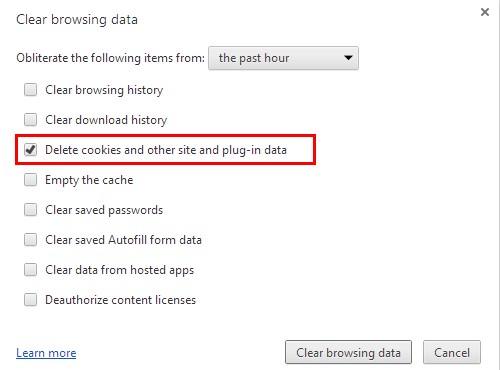
Google Chrome:
Click on the “Tools” menu and click the “Clear browsing data” button.
Select “Delete cookies and other site data” to delete all cookies from the list.
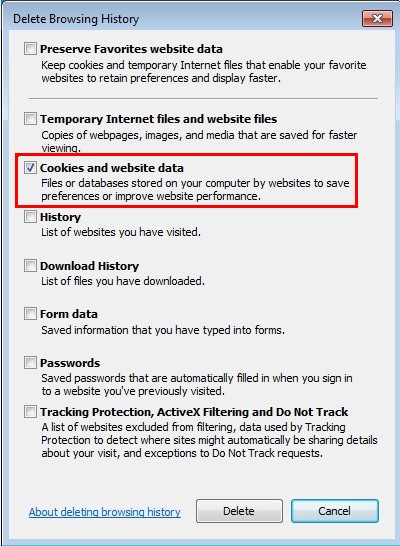
Internet Explorer:
Open Internet explorer window
Click the “Tools” button
Point to “safety” and then click “delete browsing history”
Tick the “cookies” box, then click “delete”
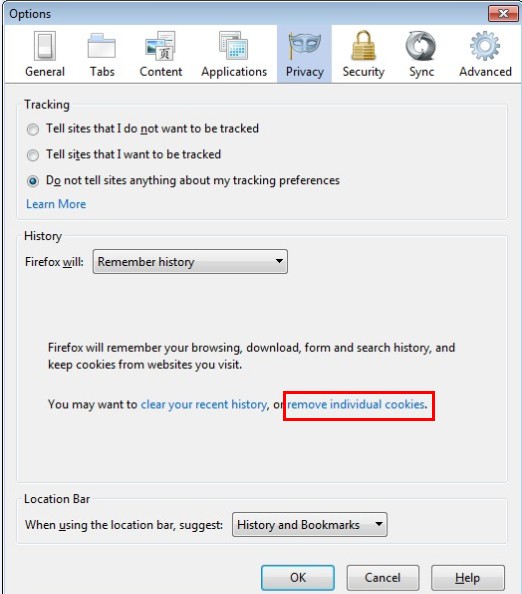
Mozilla Firefox:
Click on Tools, then Options, select Privacy
Click “Remove individual cookies”
In the Cookies panel, click on “Show Cookies”
To remove a single cookie click on the entry in the list and click on the “Remove Cookie”
To remove all cookies click on the “Remove All Cookies” button
2. End the malicious process from Task Manager.
Once Rocket Tab redirect is installed, computer user may notice that CPU usage randomly jumps to 100 percent. At any time Windows always has many running processes. A process is an individual task that the computer runs. In general, the more processes, the more work the computer has to do and the slower it will run. If your system’s CPU spike is constant and remain at a constant 90-95%, users should check from Task Manager and see if there is a suspicious process occupying the system resources and then end it immediately.
(The name of the virus process can be random.)
Press Ctrl+Shift+Esc to quickly bring up Task Manager Window:
3. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
4. Remove all the malicious files related to Rocket Tab hijacker manually.
%AppData%Local[random].exe
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\*.exe
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main StartPage
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Rocket Tab is a nasty browser hijacker that slips into the computer secretly and changes your browser settings. If you visit some unsafe sites accidentally or download suspicious free programs, you may activate the virus hidden in them and then the virus will automatically add itself to your computer without your consent. The hijacker can mess up the browsers such as IE, Google Chrome, Firefox, Safari and Opera. Thus, you cannot use browsers normally as you keep suffering from annoying redirect issues. And a lot of deceptive message will pop up to trap you to buy their useless products. Furthermore, cyber criminals can use it to access your computer to record your online behaviors. Actually computer will become more fragile if it keeps staying in your computer. Therefore, you should remove timely if you want to protect the computer from threats.
Note: If you are not a computer expert and have no idea how to perform the removal, please contact experts from YooCare Online Tech Support for further help.
Published by on October 10, 2014 5:39 am, last updated on October 10, 2014 6:21 am



Leave a Reply
You must be logged in to post a comment.