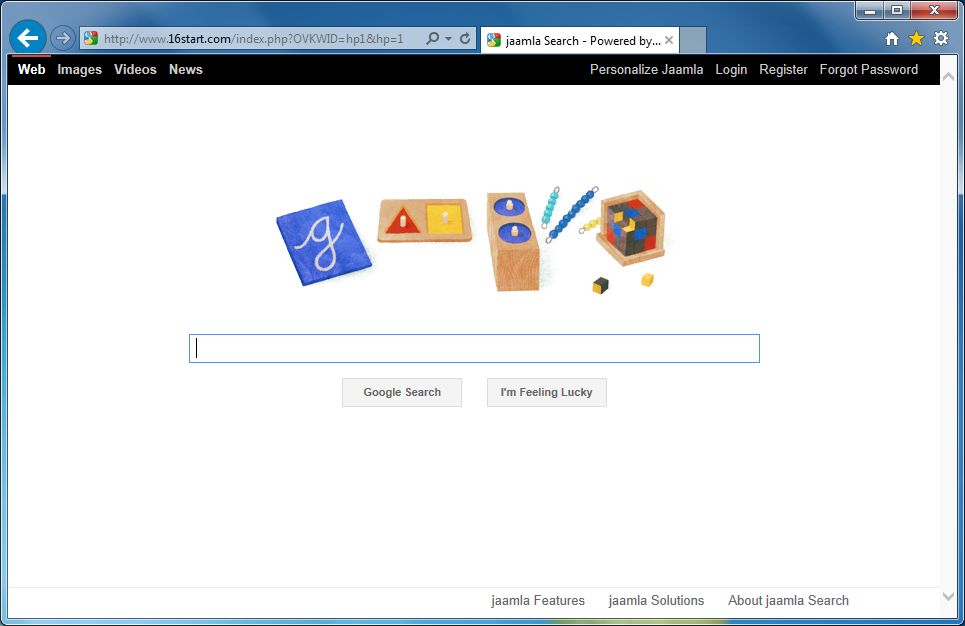
What happened to my browser? I cannot surf the Internet as usual. Each time I start my homepage, I always redirected by a browser hijacker named 16Strat.com. What’s wrong with this annoying website? What is it? After I searched the Google for it, I got to know that many victims around the world have suffered the same problem as mine. It is a browser hijacker. I didn’t know how did this nasty hijacker sneak into my computer and change my default browser and homepage. How can I get rid of this annoying hijacker? How can I get back my default homepage and the original settings in my computer? Why did my computer performance slow down ever since this malicious hijacker attacked my computer? Any recommendation will be highly appreciated!
16Strat.com is categorized to the family of the browser hijacker. It is an ad-supported domain which has been treated as a kind of redirect virus as well. It is created by the cyber criminal to do the criminal actions on the aimed computer. It can increase the website traffic by its scoundrel and aggressive marketing tactics once it accessed your computer. This malicious browser hijacker attacks the usual browsers, such as, Google Chrome, Internet Explorer, and Mozilla Firefox, etc. The majority of people maybe think that this website is a usual web. However, when you open a new tab from your homepage, there is a redirection occurring. This malicious hijacker has the ability to rule the compromised computer and then modify the default homepage and the browser’s settings of the computer. Be similar to Websearch.fixsearch.info and Searchpge.com, it can use the same tactic to trick the ignorant victims to follow its guide. It is a very dangerous kind of browser hijacker. If your computer gets this kind of infection, this malicious hijacker will record all your online behaviors and then send them to the cyber criminal by remote. Thus, once you have noticed that your homepage have changed and you are always redirected by 16Strat.com, this means that your computer gets infected by this browser hijacker. You should take measures to remove it without hesitation, or you’ll lose your confidential data, or even more damage your operating system.
It is so clear that this baleful browser hijacker will become a visual threat for the computer system and the confidential information which is stored in the browser. You maybe confuse about how this annoying browser hijacker sneaks into your computer without your approval. 16Strat.com is a tricky and risky browser hijacker, which is designed by the hacker in order to conduct their illegal activities on the targeted computer. With the high development of network technology, this cunning browser hijacker can be found in anywhere on the Internet, such as some free software programs, spam emails, unnecessary email attachments, some dubious website links and porn websites, etc. Therefore, you should pay more attention to the behaviors online for protecting your computer from being infected by this malicious browser hijacker. Because this crafty browser hijacker can run away from the detecting of any antivirus program when it is sneaking into the targeted computer, therefore, even thought there is an AVG or a Norton installed on your computer, it is not advisable to go online with careless attention on your activities. Once this malicious hijacker gets into the aimed computer successfully, it will disguise itself as a normal website browser and then rule your computer immediately. After that it will modify your default homepage and browser settings. You will always redirect by this hijacker when you go online. Kinds of popups will keep popping up on the screen and you cannot close them. This nasty browser hijacker will keep yourself from surfing the Internet normally and make you angered about it. Hence, once your computer attacked by 16Strat.com, you should take any action to get rid of this malicious browser hijacker as soon as you can.
1. It will slow down your computer performance.
2. It will pop up many unwanted ads on the screen when you are working on the computer.
3. It will become the homepage of your website browser by changing settings of your default browser. As a consequence, you can see only one browser that is 16Strat.com which can rule your computer totally, no matter you use what kind of browsers ((Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera).
4. Lots of plug-ins, extensions and toolbars will be installed in the browser in order to record all your online activities.
Note: If one of symptoms mentioned above is found in your computer, then you must know that your computer is being attacked by the browser hijacker. Since the browser hijacker is so dangerous, once your computer is infected, you should take actions to delete the hijacker. If you are not a computer expert, in case you lose your important data or damage your system, please welcome to contact Yoocare/Yoosecurity Online Expert for help now!
16Strat.com hijacker hijacks your default browser to redirect your web search results and modifies your default homepage and browser settings. Manual removal is the most effective way to completely uninstall it from an infected computer’s operating system, for the season that this hijacker is so cunning and dangerous, antivirus programs cannot get rid of it permanently. Here are the manual guides for users to remove the annoying hijacker.
1. Clean Add-ons and Extensions
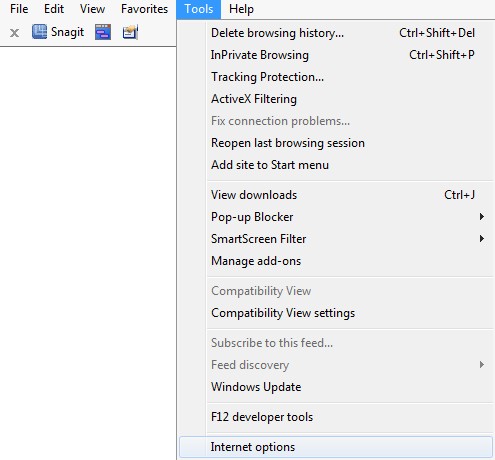
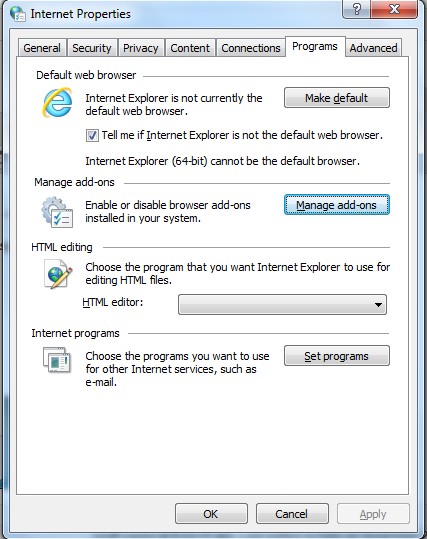
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
(2). Click Programs tab, click Manage add-ons and disable the dubious add-ons
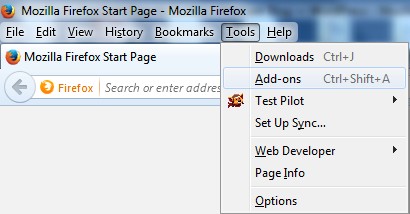
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
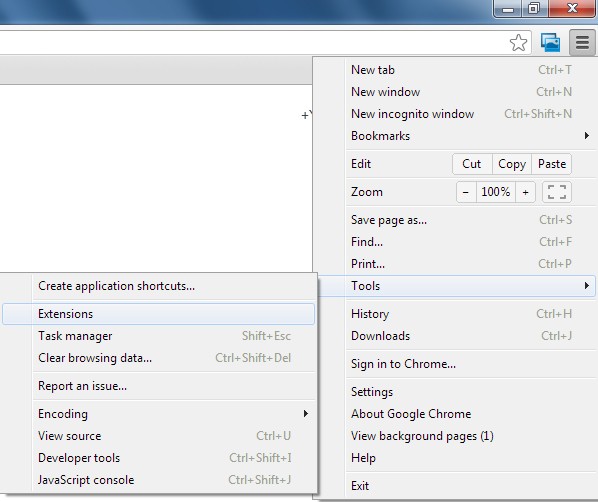
(2). Disable the extensions of 16Strat.com
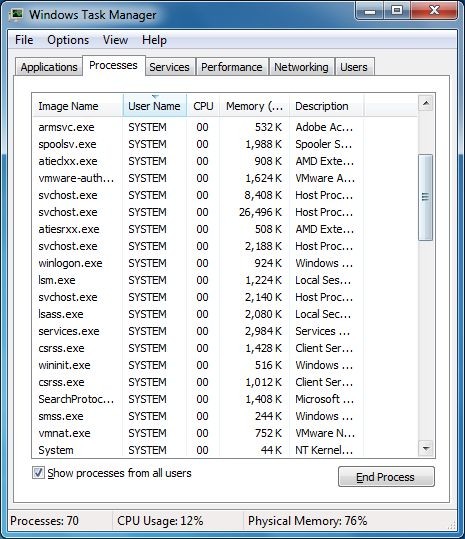
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
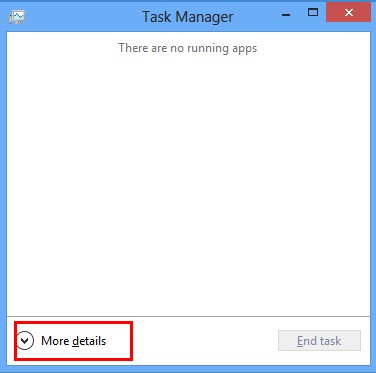
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
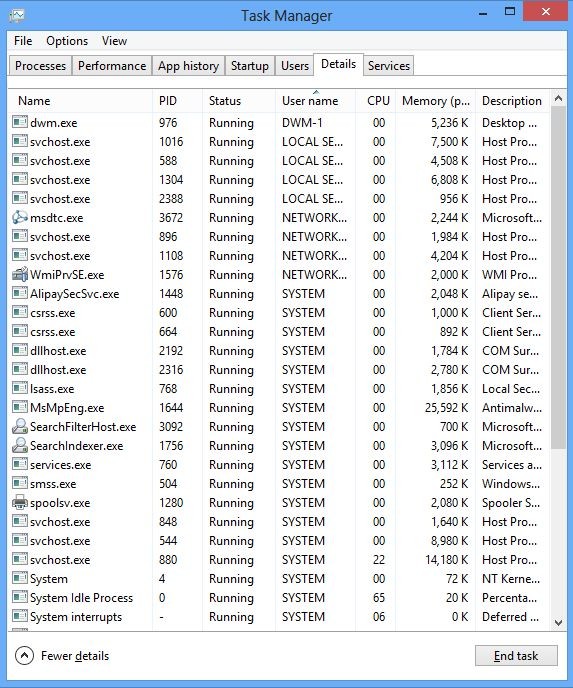
(2). Find out and end 16Strat.com’s processes
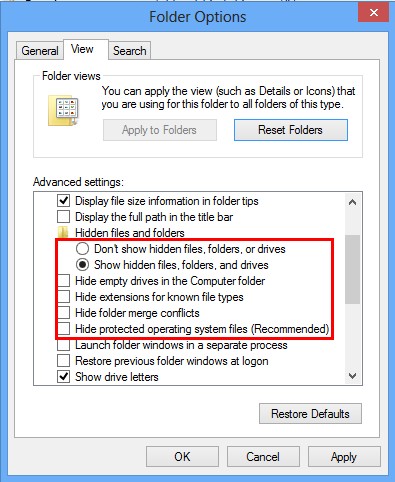
3. Show Hidden Files
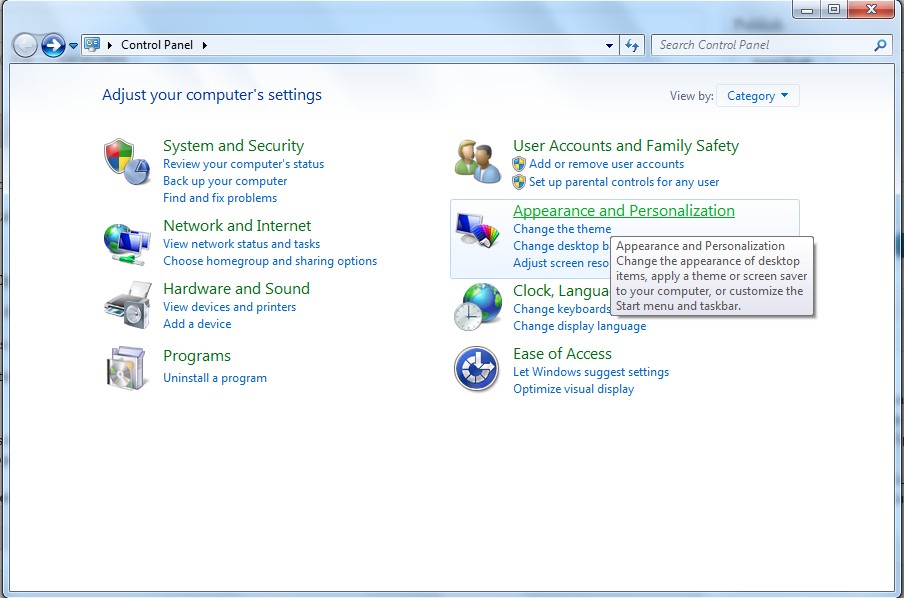
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
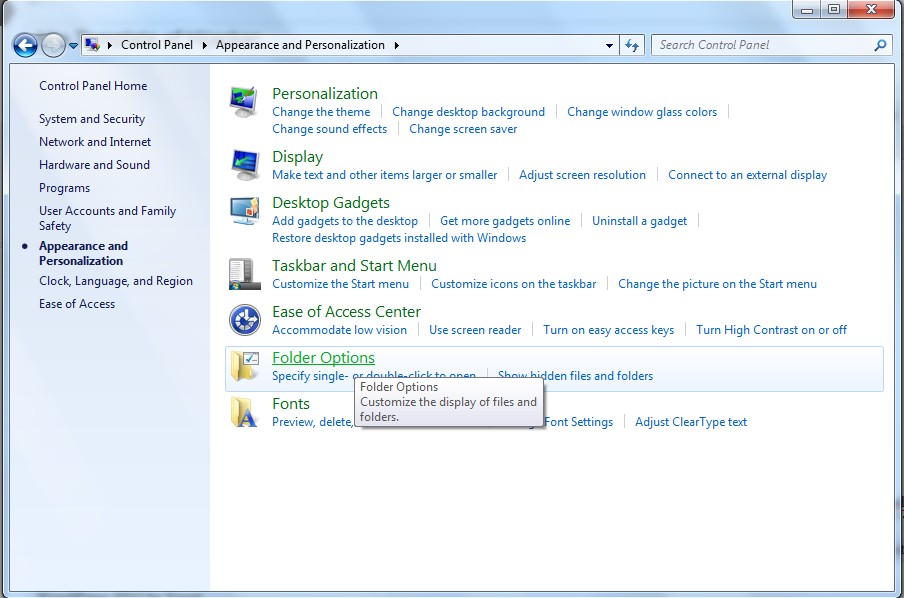
(3). Click on Folder Options
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
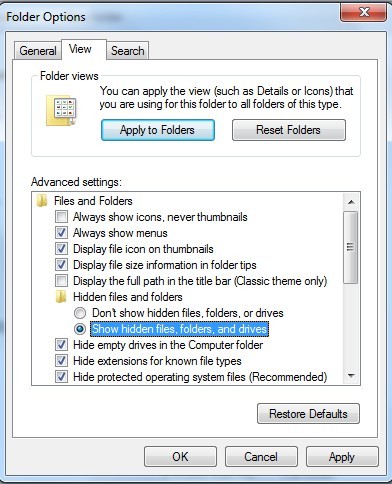
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users: Press Win+E together to open Computer window, click View and then click Options
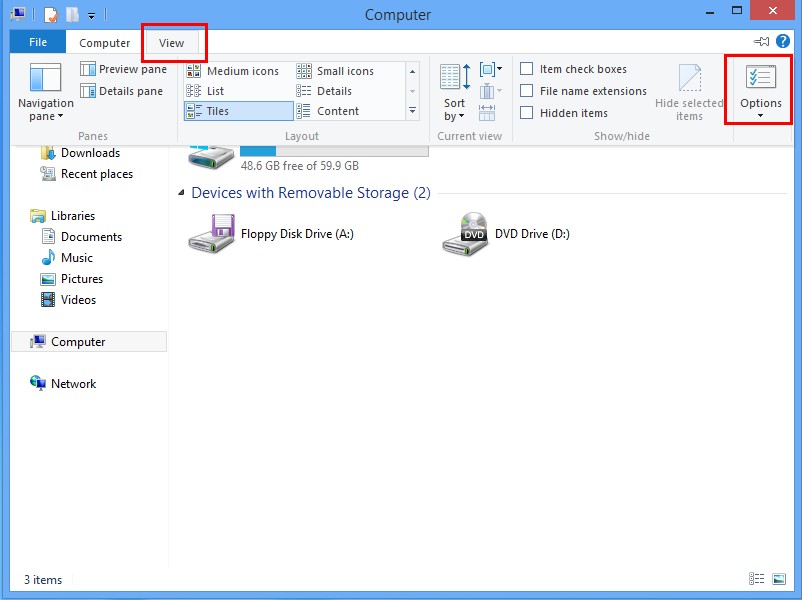
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to 16Strat.com through Registry Editor Press Win+R to bring up the Run window, type “regedit” and click “OK”
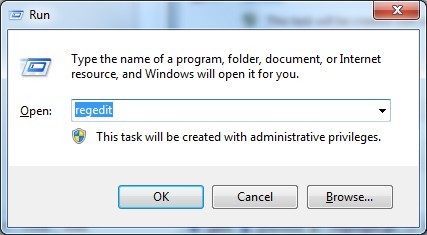
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe %AppData%\Roaming\Microsoft\Windows\Templates\random.exe %AllUsersProfile%\Application Data\~random %AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Conclusion
From the mentioned passage, you have known that 16Strat.com is a browser hijacker which is designed by hackers in order to process the illegal actions on the targeted computer. Thus, this problem should be solved as soon as possible when your computer is redirected by this vicious browser hijacker. Once your computer sets in this kind of trouble, you do not be nervous and mislead yourself by the trouble. In order to get rid of this annoying hijacker from your computer, you should take any action to remove it. As you know, once this hijacker attacks your computer, it will rule your computer and then alter your default homepage and browser settings. It is a big threat for your operating system and your confidential data. It is not a wise choice to leave it on your computer with the passage of time. Manual removal is recommended to be the most effective way to delete this malicious hijacker.
Suggestion: The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on September 17, 2014 1:56 pm, last updated on September 22, 2014 9:10 am



Leave a Reply
You must be logged in to post a comment.