Have you ever been harassed by browser hijackers like this one Istsearch.com? It not only changes your homepage as well as search engine, but also redirects you to some unwanted websites. It makes your online activities become awful. You should get rid of this browser hijacker as soon as possible.
Istsearch.com is classified as a browser hijacker which is able to affect most of famous browsers on users’ computer in different regions. Websearch.fixsearch.info and Searchpge.com can be put in the same category together with it. The browser hijacker is released by the developers with the purpose of promoting something through taking over your browser. Accessing the resources it offers may even help some bad guys to get in and control the computer control remotely. What is more, it also facilitates the developers to collect as much valuable information as possible from innocent computer users.
Looking like a normal search engine in your browser, Istsearch.com actually is a browser hijacker and has annoyed many computer users. When it gets in the computer, it will prevent you from accessing other websites normally via occupying the browser completely. Everyone should know that legitimate sites won’t tamper with the homepage and search engine in the browser without the permission from the computer users. Some experienced computer users will search the Internet from its webpage for they don’t know it is actually a browser hijacker. The search results listed on Istsearch.com search engine are suspicious, some of which may contain dangerous viruses and malicious software. In other words, the hijacker can be the blasting fuse of these expanded infections in the computer. You will always be redirected to elsewhere on the network instead of the accurate places you want to go to. In general, your system will become more vulnerable to malicious viruses with Istsearch.com in the computer. Therefore, we should have it removed as early as possible.
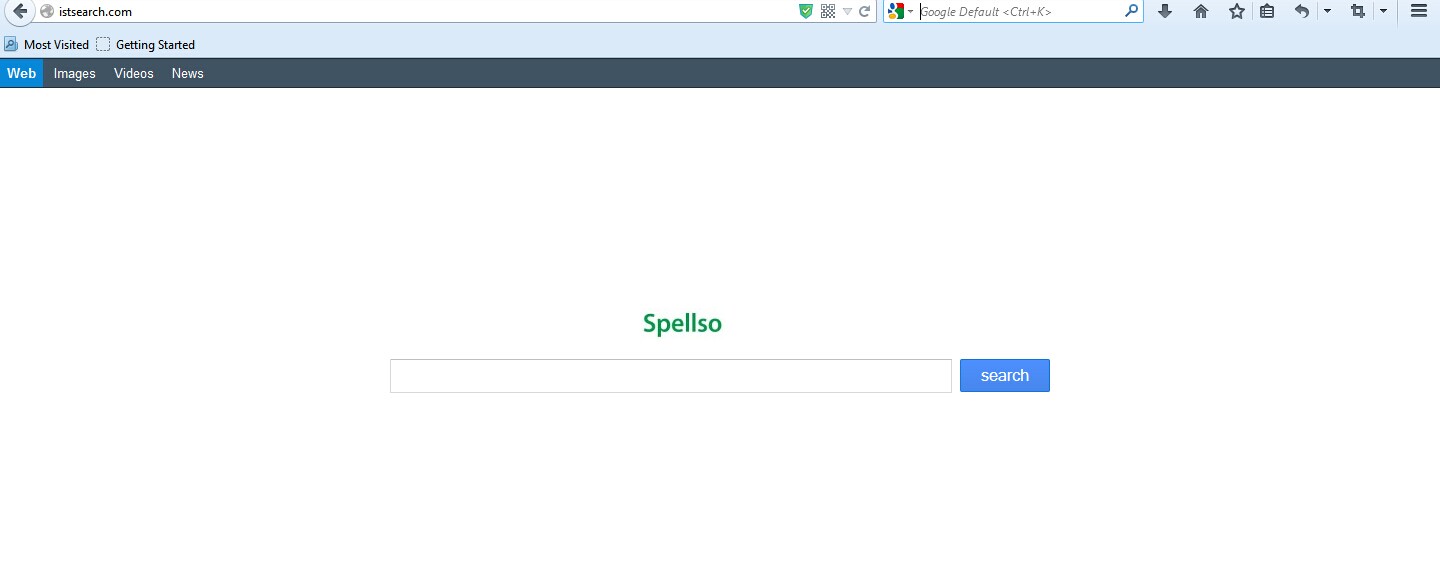
1. Istsearch.com is able to become the startup page of your web browser via modifying browser settings. No matter which browser you are using (Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera), you can see the browser is occupied by it completely.
2. It may also install plug-ins, extensions and toolbars in the browser so as to record your search history as well as cookies.
3. You need to wait for a long time when visiting websites because the browser always gets stuck and is slow in reaction.
4. This annoying redirect may also result in unstable Internet connection and system freezes frequently.
5. You are forced to receive many advertisement windows when the computer is connected to the Internet.
You may want to figure out why your antivirus software is unable to capture this Istsearch.com? The fact is that the hijacker is specially designed so as to stay in the computer firmly. It has the ability to bypass many antivirus tools. In this case, manual removal can be the most effective way to ensure a complete removal. Professional computer skills and knowledge are needed to process the removal safely. You are also recommended to do a system backup beforehand.
1. Clean Add-ons and Extensions
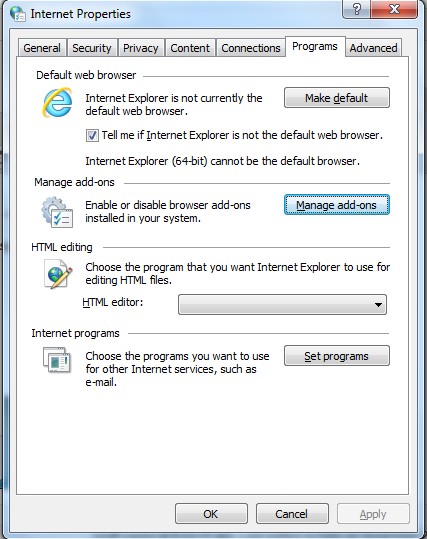
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
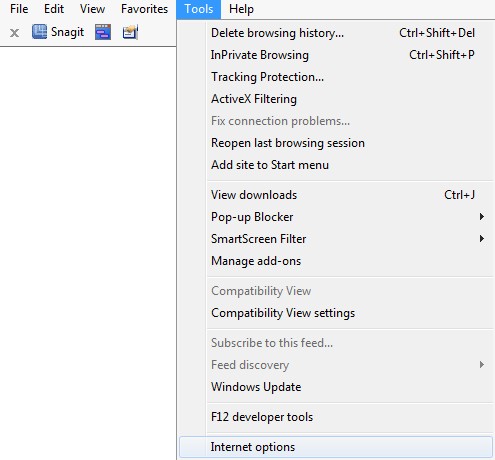
(3). Click Programs tab, click Manage add-ons and disable the suspicious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
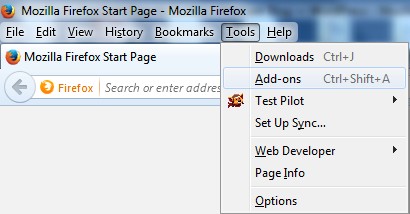
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
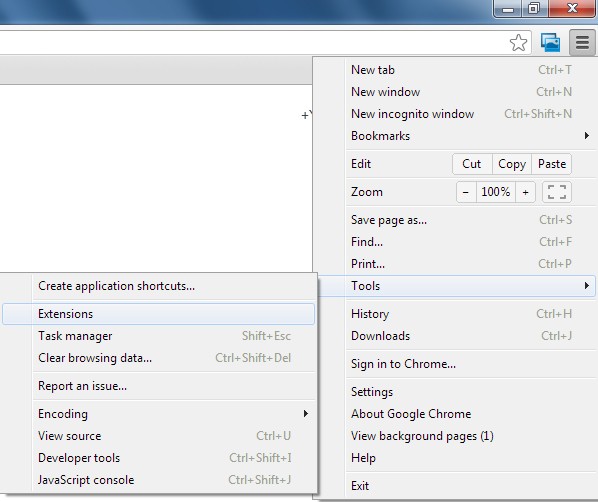
(2). Disable the extensions of Istsearch.com
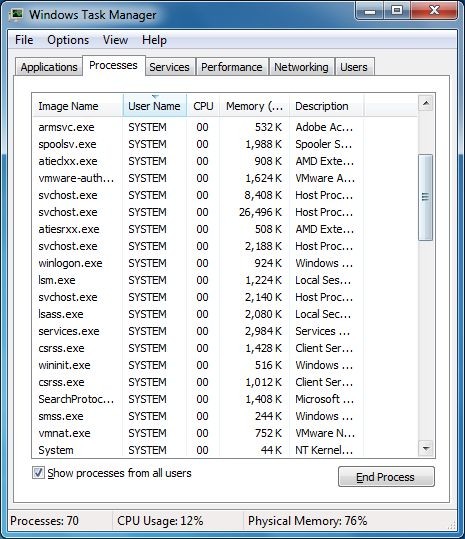
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
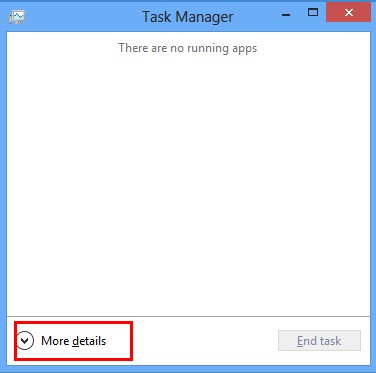
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
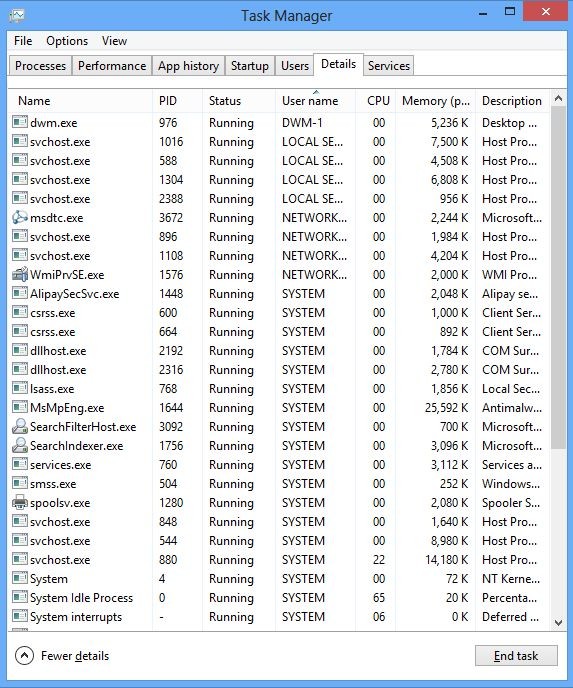
(2). Find out and end Istsearch.com’s processes
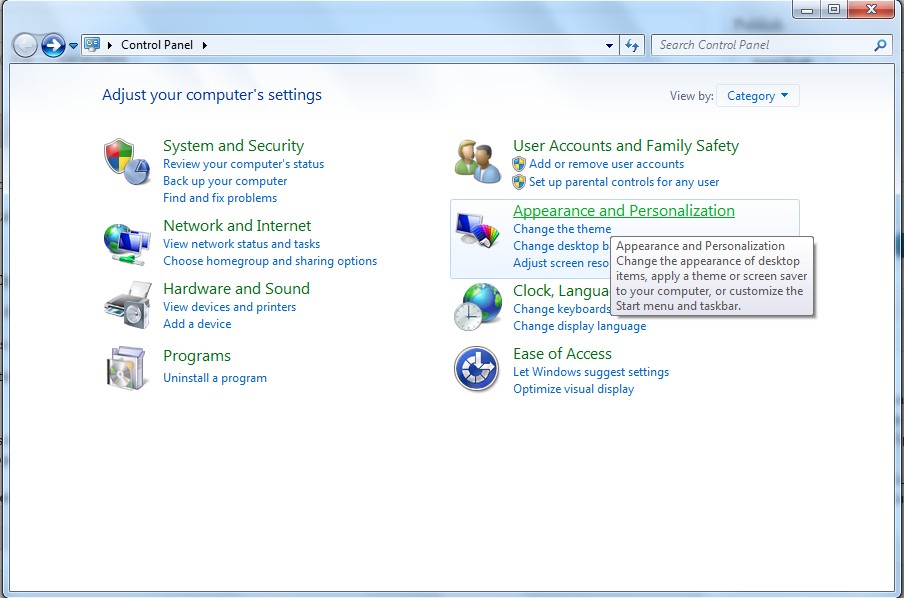
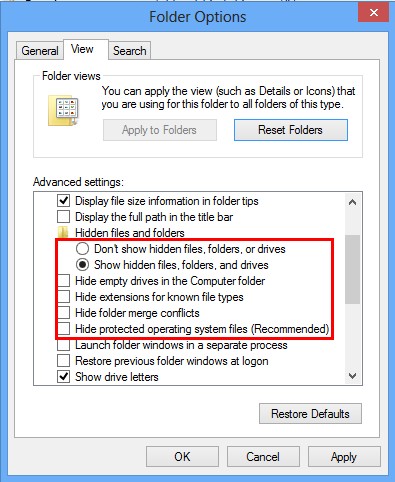
3. Show Hidden Files
(1). Click on Start button and then on Control Panel
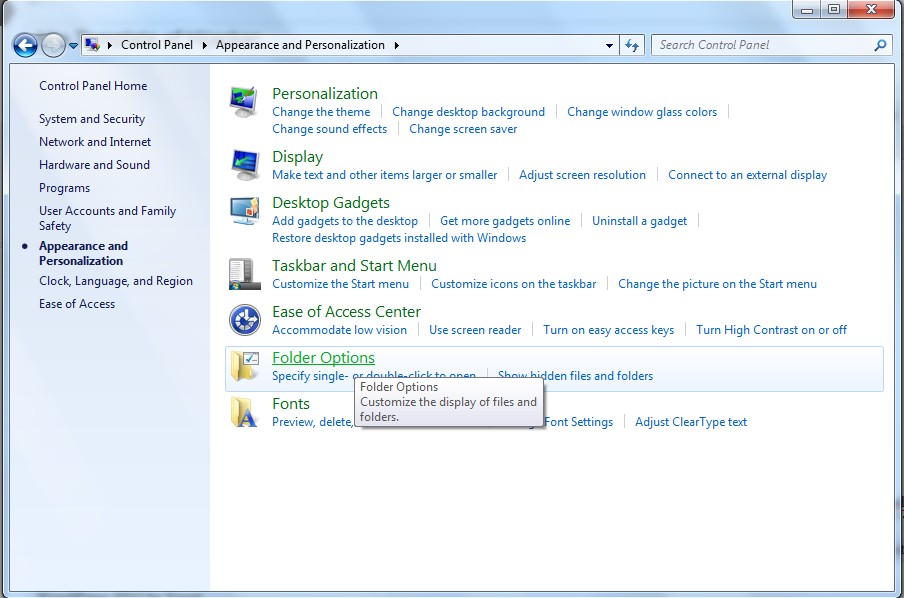
(2). Click on Appearance and Personalization
(3). Click on Folder Options
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
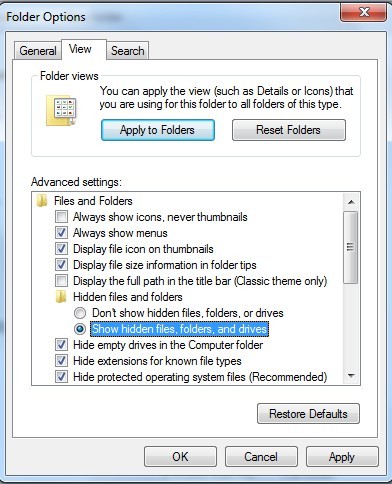
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
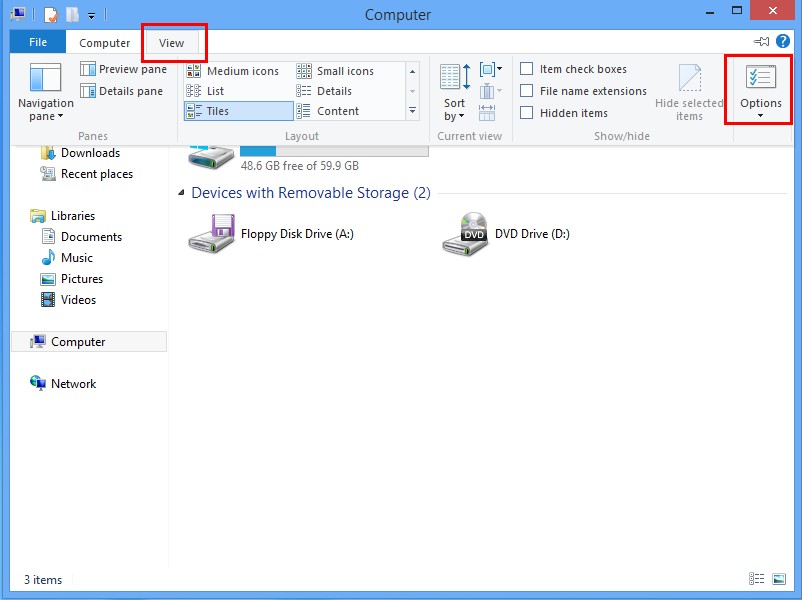
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to Istsearch.com through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
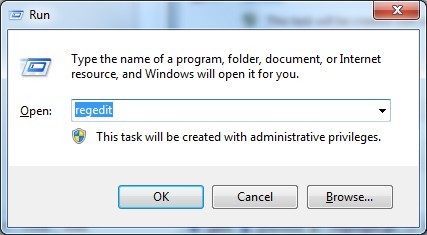
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\~random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Browser hijackers are very common in these days. Many computer users from different countries have reported that browser hijackers are in the computer. Generally speaking, you can notice that a browser hijacker like this Istsearch.com affects your computer at the beginning from the modified homepage. And you will have to watch many pop-up ads persuading you to spend money in buying unreliable products. The reasons you hate the Istsearch.com hijacker include 1) redirect you to hacked websites online; 2) share your information with the developers such as browning history and search keywords; 3) show you pop-up windows constantly. Therefore, you should be cautious when you surfing the Internet and input any key information. Suggestions on avoiding Istsearch.com: 1) stick to one or two familiar search engines; 2) be careful when opening strange emails; 3) do not install unknown free programs and browser add-ons.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on September 16, 2014 9:04 am, last updated on September 22, 2014 9:13 am



Leave a Reply
You must be logged in to post a comment.