Is your browser not very cooperative? You are always redirected to a website called Websearch.fixsearch.info while surfing the Internet? Why does it stop you from visiting those websites you often go to? How do you maintain a normal and safe browser?
Websearch.fixsearch.info is actually a browser hijacker. Most of us think that it is a common site containing a search engine. However, this special domain has the ability to control the browser completely, which has angered many computer users from all over the world. Similar to Start.Facemoods.com and Findpages.net, it plays the same trick to deceive computer users. Once you start online activities from the web site, your online behaviors will be recorded and transmitted to its developers. So, it is not a reliable site.
Do you want to know where you pick up the Websearch.fixsearch.info browser hijacker? It is found to be together with some unfriendly programs, spam email attachments and suspicious website plug-ins. You should not think that it is still safe to access these unsafe online resources with an antivirus program installing in your computer, because the hijacker is specially designed by the developers who is proficient in computer tech skills. In fact, it is able to bypass antivirus programs and dive into the computer system without permission from the computer user. Once it is installed successfully, it will show up as the default homepage and search engine in your browser. It forces you to start online activities from its domain. However, the search results it provides are unauthentic. There may be many other viruses including Trojans and malware hiding in those search results and waiting for the opportunity to infect your computer. In addition, you will have to watch many pop-up ads when you are working on the computer, some of which can be closed while others stuck on the screen unless you restart the computer. Therefore, you should remove the hijacker as soon as possible.
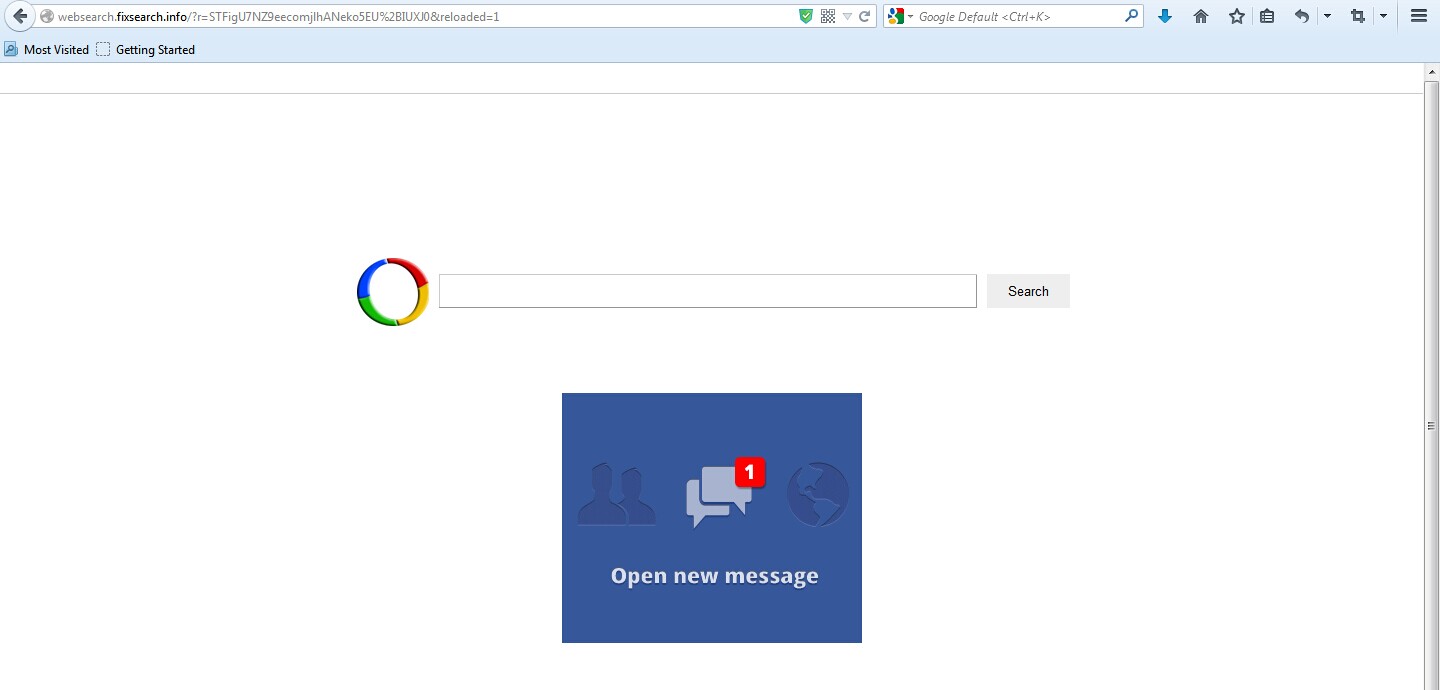
1. It is able to become the startup page of your web browser via modifying browser settings. No matter which browser you are using (Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera), you can see the browser is occupied by it completely.
2. It may also install plug-ins, extensions and toolbars in the browser so as to record your search history as well as cookies.
3. You need to wait for a long time when visiting websites because the browser always gets stuck and is slow in reaction.
4. This annoying redirect may also result in unstable Internet connection and system freezes frequently.
5. You are forced to receive many advertisement windows when the computer is connected to the Internet.
Here are some steps to help you delete Websearch.fixsearch.info manually. Because the hijacker in the browser is able to change with the passage of time, manual removal needs expertise so as to check the whole system. Therefore, it is best to do a backup in advance.
1. Clean Add-ons and Extensions
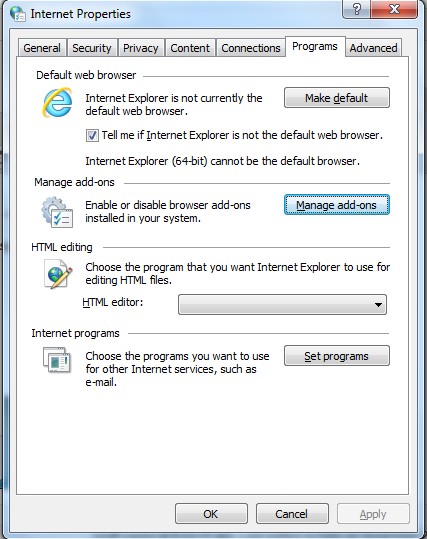
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
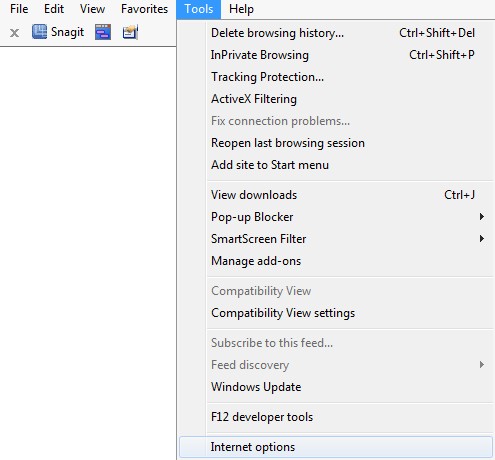
(3). Click Programs tab, click Manage add-ons and disable the suspicious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
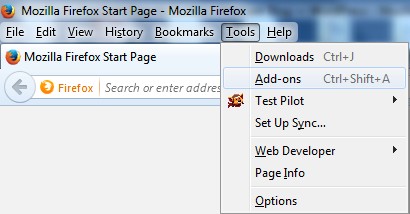
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
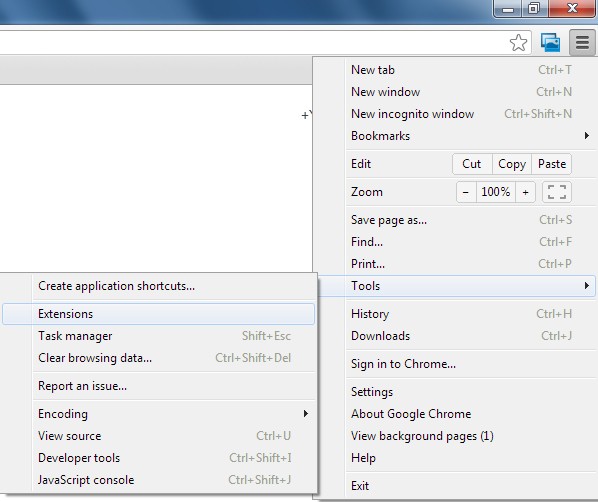
(2). Disable the extensions of Websearch.fixsearch.info
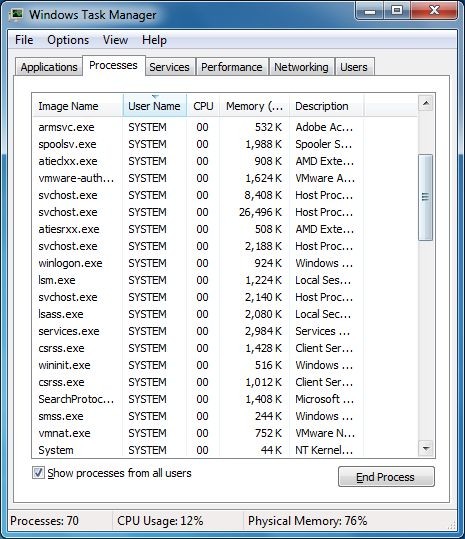
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
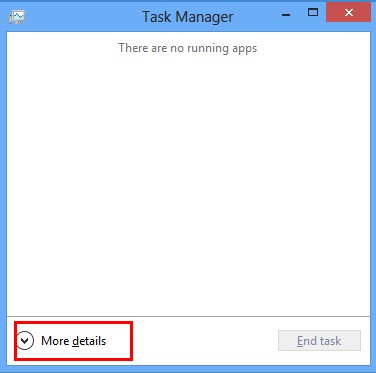
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
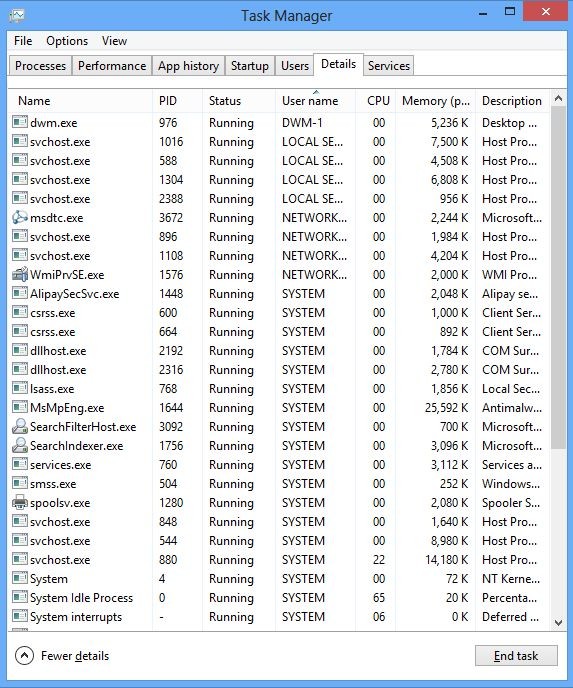
(2). Find out and end Websearch.fixsearch.info’s processes
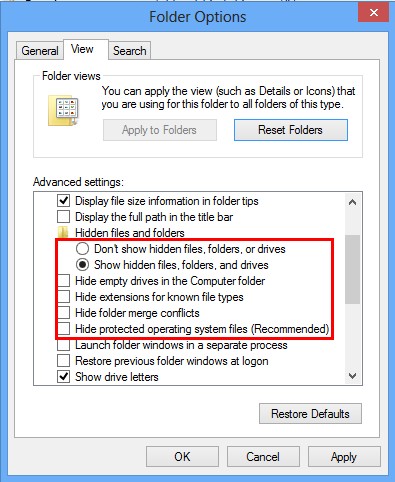
3. Show Hidden Files
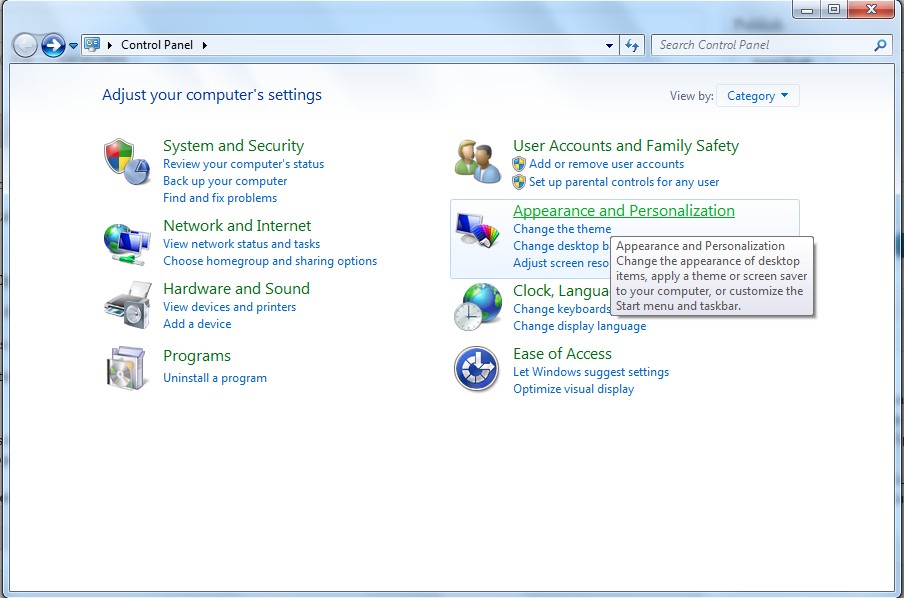
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
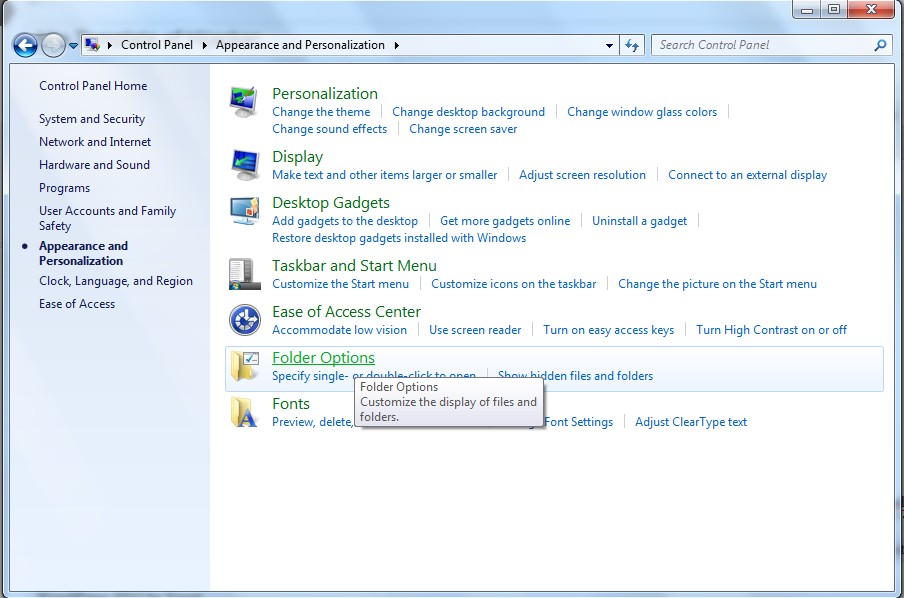
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
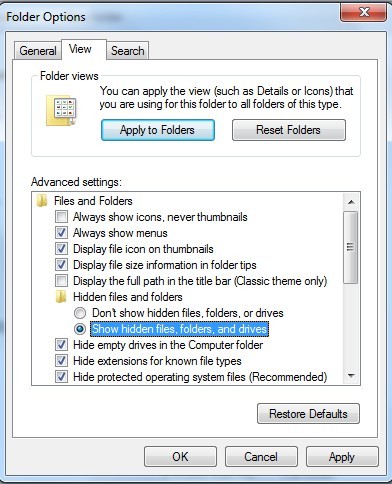
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
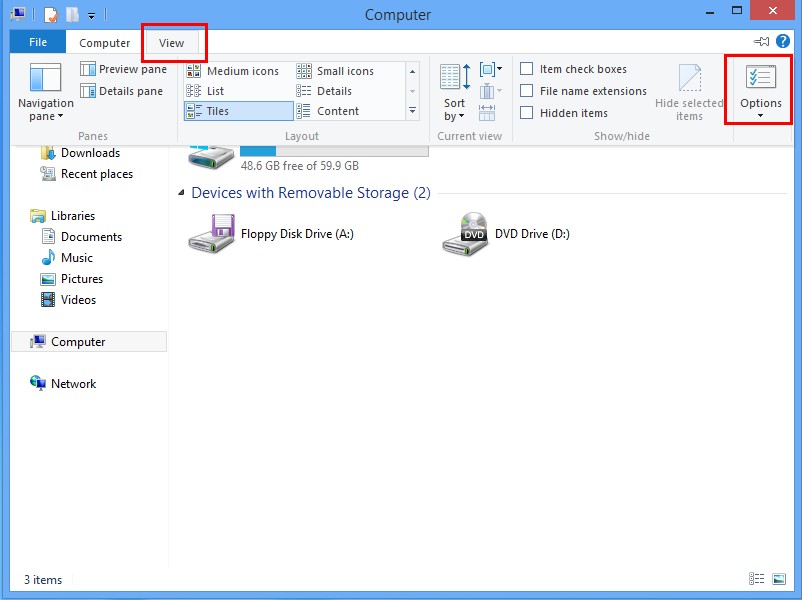
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries related to Websearch.fixsearch.info through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
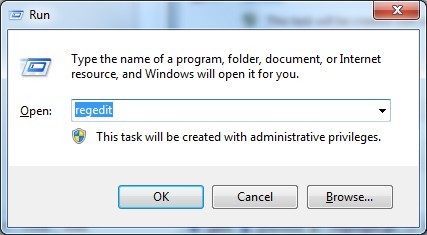
While the Registry Editor is open, search and delete its registry entries
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
(2). Find out and remove the associated files
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%AllUsersProfile%\Application Data\~random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Websearch.fixsearch.info is a browser hijacker which has affected many computers from every corner of the world and annoyed computer users severely. It is not a useful search engine that offer accurate search results. Though it looks similar to other legit search providers including Yahoo, Bing and Google, it is indeed a browser hijacker. Normal sites won’t take over the browser completely without computer user’s permission. Why can’t the antivirus program deal with this problem successfully? Because it is created by a group of people who know much about computer tech. The hijacker can reset the default settings and change registry keys to root deep in the computer. You should not use this false search engine. All the results and links it shows are to promote its sponsors or even contain a lot of vicious viruses and malicious software. Pop-up ads and a lot of useless notices will take over your screen and harass your activities in the computer. Thus, there is no doubt that you should remove this Websearch.fixsearch.info as early as possible.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on September 2, 2014 8:37 am, last updated on September 22, 2014 10:09 am



Leave a Reply
You must be logged in to post a comment.