Can’t get rid of TR/Downloader.Gen? Don’t know how to remove Trojan horse virus completely? Does antivirus work fine when dealing with this virus? How can it run with the system automatically? How can it hide behind system files? If you want to know more about Trojan horse virus, this post would be a good post to know.
TR/Downloader.Gen is a dangerous virus that can get into your computer secretly. It would stay in the infected computer to steal your files and hack your account to send virus links you to your contacts. The outbreak of a large number of Trojan horses in your computer now is because of that the virus opens loopholes in your computer, constantly looks for opportunities to intrude its companies in. Therefore, more and more Trojan virus has been brought into to the infected computer. This Trojan works with other viruses to expand the threat and it is not an exaggeration to say that the Trojan horse is set as a thief to get sensitive data in your computer. Once your bank account and password had been stolen, it has been too late to prevent financial loss. Killing PC viruses become indispensable needs to every PC user.
Trojan horse is a backdoor virus programs. As we mentioned before, it can be settled in secret to remote control your computer without permission. If you have let it in accidentally, you have nothing to do but prevent further loss. Like the Greek soldiers opened the door to let the horse in, Trojan virus will open the “door” in your system. And that is the reason why people named this nasty virus as Trojan horse virus. Hacking into your computer through this special “back door” program, then activate the remote control permission of your computer would give hacker permission to do what you can do to the infected computer. We can say, they can do everything you can do on your own computer. If you can write a file, they can; if you can open the pictures in your computer, they can see; they can open it. Shortly, they can get whatever they want to do, such as opening your photos, and transfer it to hacked server. More importantly, it also can control your mouse and keyboard to get your privacy, your password through even every mouse click. In order to prevent further threat, you need to delete it as soon as possible.
TR/Downloader.Gen allow cyber-criminals to break into the infected computer without noticed and disables executable program and cause system crash. It changes important computer settings to allow remote control from cyber criminals. It will modify your registry settings and important key value to make it difficult to be removed. It accesses your data, your tabs and browsing activity on all websites and is able to cause system crash and disable your executable programs. Meanwhile, it drops some other threats including malware, adware parasites and spyware into your computer.
Manual removal is a complicated and risky process, so please back up all important data before making any changes on your computer. Here are some instructions to handle with the Trojan horse manually, and be cautious when going through the following steps.
1 Clear all the cookies of the affected browsers.
* Google Chrome: Click on the Tools menu → select Options → Click “Under the bonnet” tab → locate “Privacy” section → browsing data” button → “Delete cookies and other site data” to delete all cookies from the list.
* Internet Explorer: Click “Tools” → Click “safety” → “delete browsing history” → Tick “cookies” box and click delete
* Firefox:: Click “Tools” → Click “Options” → Click “Privacy” → Click “remove individual cookies”
2 Remove all the add-ons and extensions.
* Google Chrome:
(1). Click the Customize and Control menu button →Tools→ click Extensions
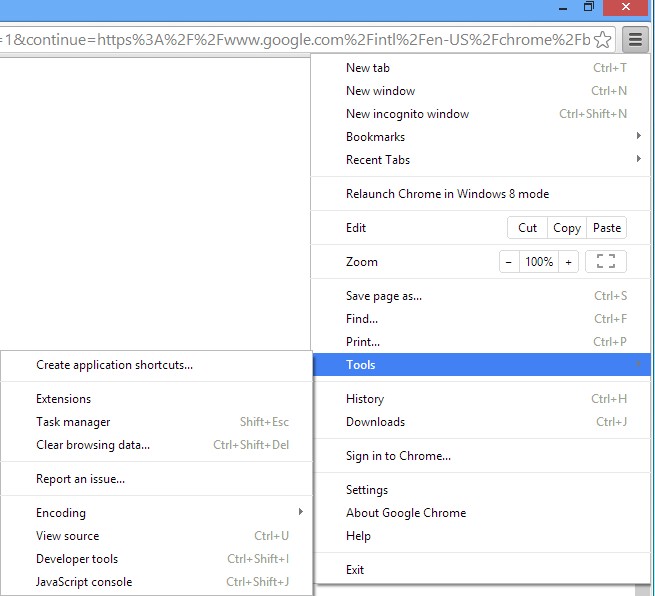
(2). Select the related Extension and click Disable.
* Internet Explorer:
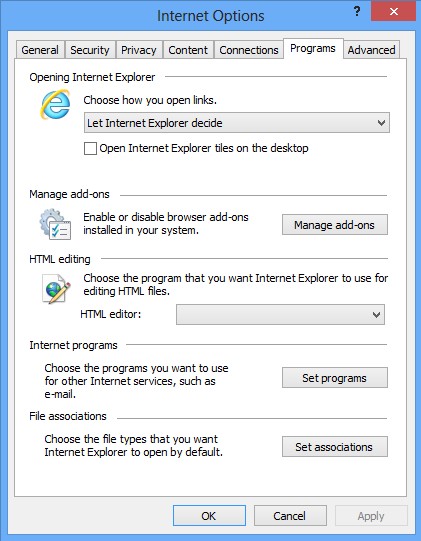
(1). Click Settings → Click Manage Add-ons
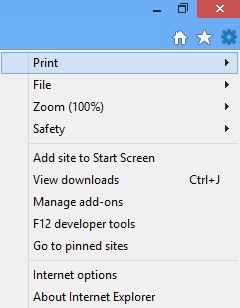
(2). Click Programs tab → Click Manage Add-ons → Disable all the suspicious add-ons.
* Firefox:
(1). Click the Firefox menu and click Add-ons
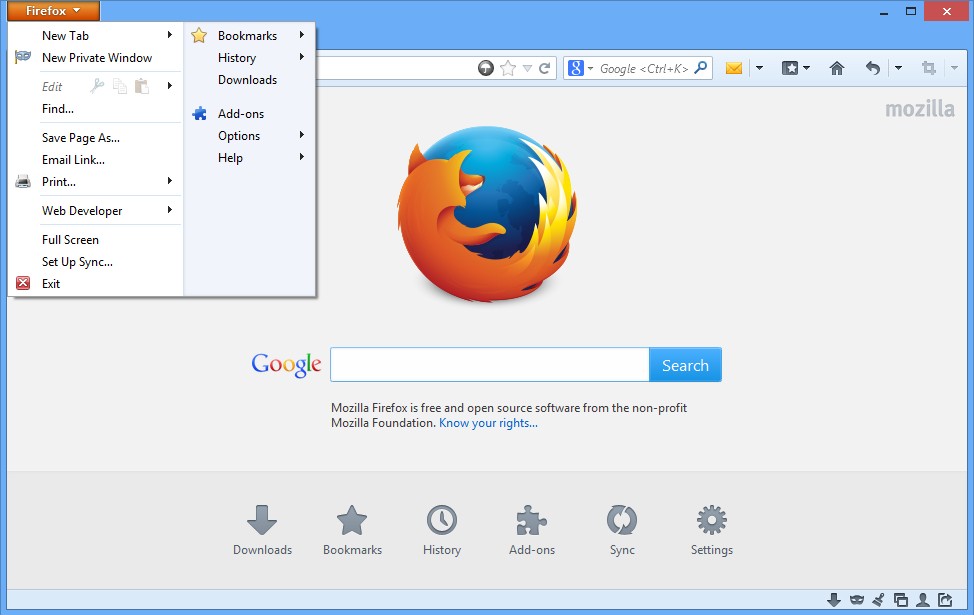
(2). Click Extensions, select the related browser add-ons and click Disable.
3. Show Hidden Files
(1). Press Win+R to get run option
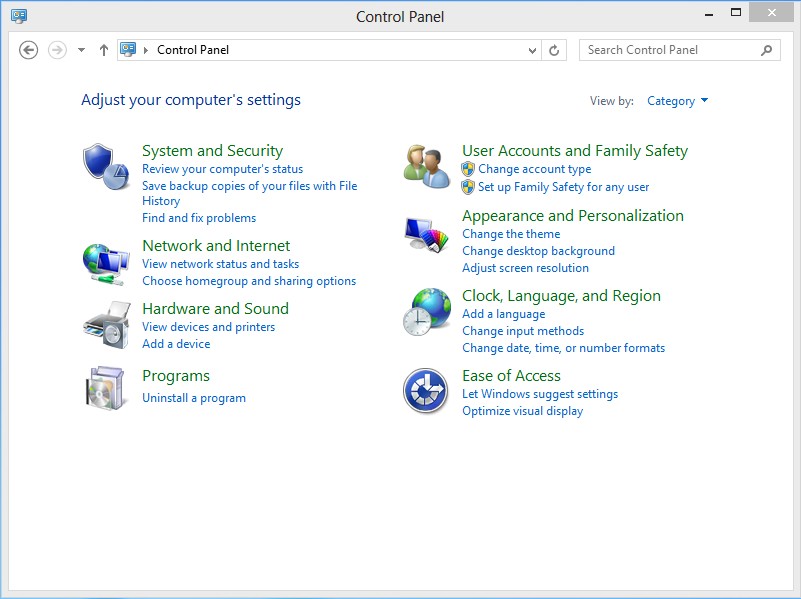
(2). Type in Control Panel and hit enter to get Control Panel
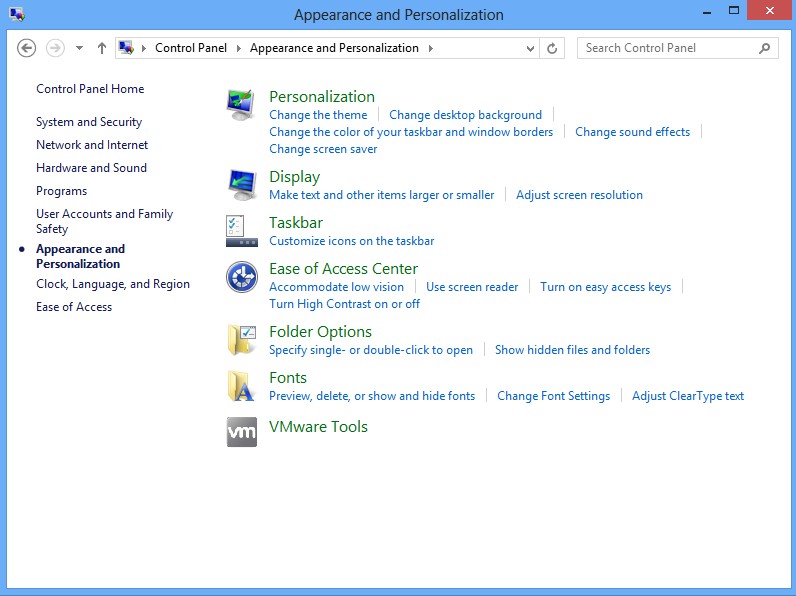
(3). Click on Appearance and Personalization link
(3). Click on Folder Options link
(4). Click on View tab in Folder Options window
(5). Tick Show hidden files, folders, and drives under Hidden files and folders tab
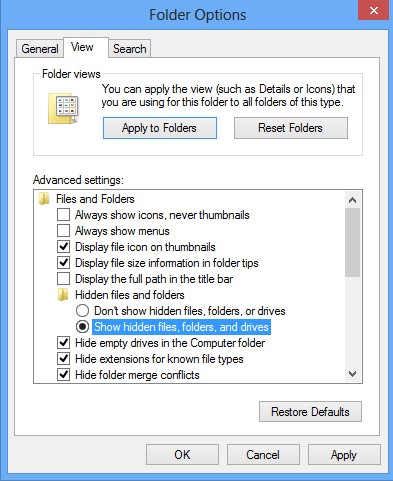
(6). Click Apply to effect, then click OK at the bottom of the Folder Options window.
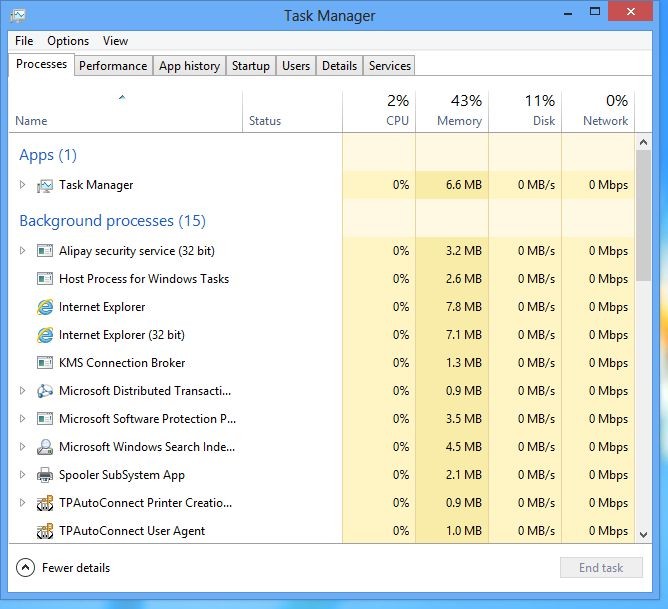
4 stop virus processes in the Windows Task Manager.
(1). Press Ctrl+Alt+Del keys together to get Windows Task Manager
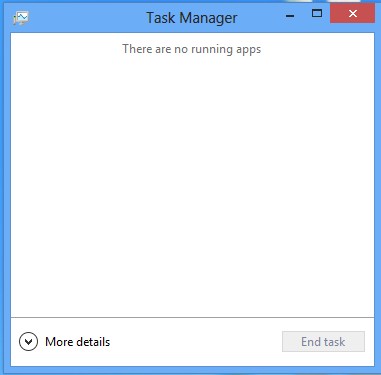
(2). Click More details
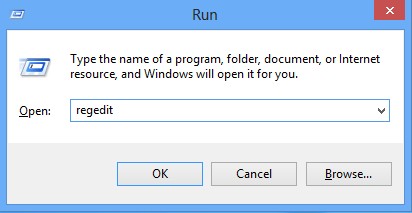
5. Remove all the malicious files registry entries through Registry Edit.
*TR/Downloader.Gen is a malicious Trojan virus which implants itself to the infected computer secretly and makes your computer and other working process slowly during infection. It can install the itself into the computer system without your awareness and consciousness. To make matters worse, the Trojan is used as a tool for hackers to achieve hacking purpose to steal your information. It is recommended to remove it with a complete and fast procedure. Users can follow instruction here to have it manual deleted instantly.
(1). Using Registry Editor to delete all the related registry entries.
*Guides to open Registry Editor:
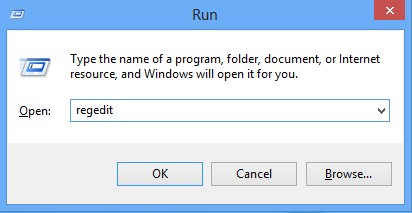
Press Win+R key together then Registry Editor will pop up.
(2). Find out and remove the associated files of TR/Downloader.Gen.
TR/Downloader.Gen is a stubborn virus which can be a big threat to the infected computer and files in the infected computer. It will change the settings of the victim system to keep safe from security detection and virus removal. If you can’t delete it completely, it will run again in the next time you turn on the infected computer. Keeping the virus in your computer is not correct because it can steal your confidential information in the infected computer.. A wise choice is to remove it completely. you will have to face the situation and list an instant removal on your top priority list as all your activities taken on the infected computer is watched by hackers too. According to our investigation, we can draw a conclusion that the best method of dealing with this virus is manually removal that will stop all the malicious actions because of antivirus application might not be able to complete the full removal.
Friendly Reminder:
If you still find it hard to follow the removal guide above, please contact YooCare: PC experts 24/7 online will offer you the most effective tech support to remove infection completely.
Published by on February 27, 2014 9:26 pm, last updated on February 27, 2014 11:01 pm



Leave a Reply
You must be logged in to post a comment.