You do not know when the computer is infected with Win32.ZAccess.ewjg until the anti-virus program pops up a warning to tell you that your computer is at risk? You try to use the automatic removal function of the antivirus program directly, but this Trojan still appears again and again? What kind of harmful things can it bring? Can you use your computer safely? If you want to know more, please read this article.
Win32.ZAccess.ewjg is a notorious Trojan virus. The virus makers adopt advanced technology in making it so that it is able to hide deeply in the infected computer and evade antivirus software’s removal. The Internet brings convenience to people who want to save time, but there still are some bad guys who spread bad things via taking the advantage of the universality of the Internet. If the computer user visits fishing websites accidentally, clicks on unknown links, downloads free software released by hackers and opens spam email attachments, the computer will be infected with this virus. Furthermore, the Trojan is so rampant that it can take initiative attack to computers.
Once landing into the computer successfully, Win32.ZAccess.ewjg begins to create chaos. You will find that your computer becomes very weird suddenly. No doubt, this is caused by the Trojan. Its running needs a large amount of system resources, which will greatly weaken the computer performance. Running programs will shut down suddenly or even become disabled. By the way, if a new computer becomes very slow abruptly, you should realize that something is wrong and check the whole system immediately. In addition, the Trojan virus has the ability to make the system vulnerable to other viruses’ invasion. With more and more dangerous viruses being implanted into the computer, the computer faces the risk of collapse. What’s worse, it can record your operating traces, which enables the cyber criminals to get your personal privacy and use some of your some valuable information illegally. Therefore, please remove the Trojan horse virus. It is able to disperse its files and registry entries into the infected computer with the purpose of preventing the antivirus software from deleting its components completely. As a result, most antivirus programs cannot handle it. In this case, only manual removal can solve the problem.
1. It has the ability to download additional components and other infections in the target computer in order to fully complete its penetration.
2. It is able to cause system crash and destroy some of your programs in the infected computer.
3. It facilitates the virus makers to intrude your computer remotely without letting you know.
4. It is capable of collecting your browsing history and other private data.
The malicious Win32.ZAccess.ewjg can install itself into the computer system without your consent and awareness. It makes your computer work slowly and implants other nasty infections into the computer. To make things worse, this Trojan is a tool for the cyber criminals to invade the infected computer to steal your information. Through making use of advanced technology, it maintains the ability to combine its components with system files or to generate fake system files, which confuses computer users as well as antivirus programs. They cannot identify it accurately and timely, let alone remove it thoroughly. Therefore, manual removal is the best choice to drive it away from your computer. In this case, you are advised to delete every file generated by it manually so as to spare all later trouble. The manual removal needs to be handled carefully so as to avoid any subsequent damages. Users can follow the manual guide here to have the hijacker removed instantly.
1. End Relevant Processes
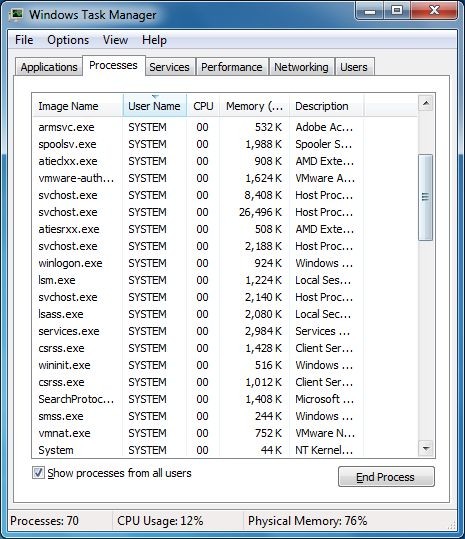
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
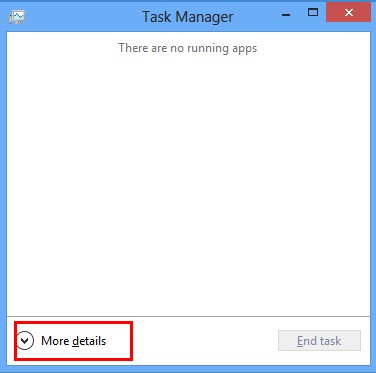
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
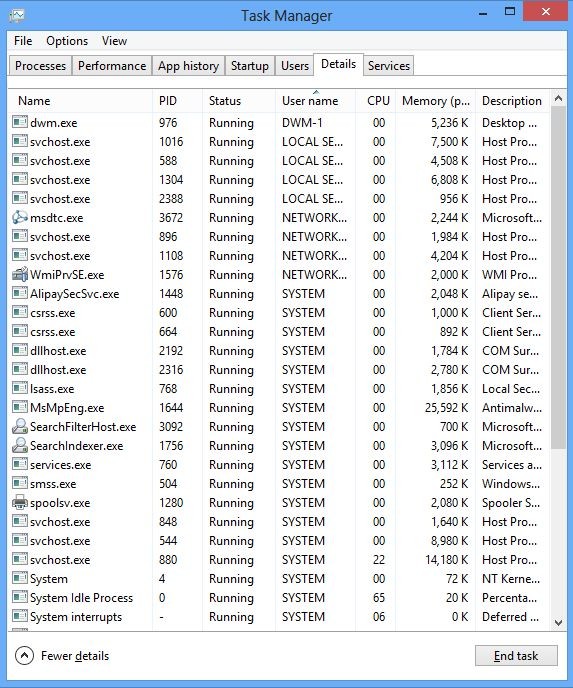
(2). Find out and end the processes of Win32.ZAccess.ewjg
2. Show Hidden Files
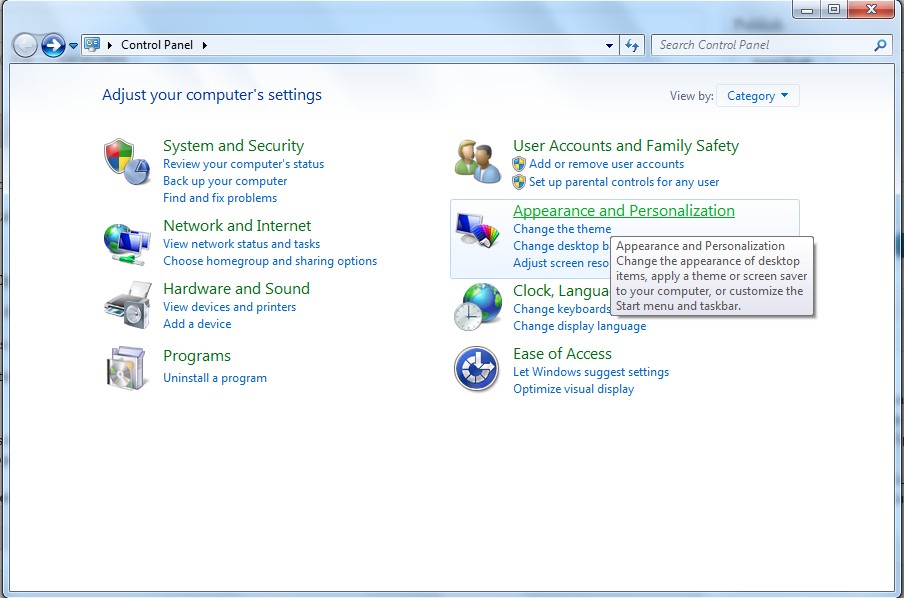
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
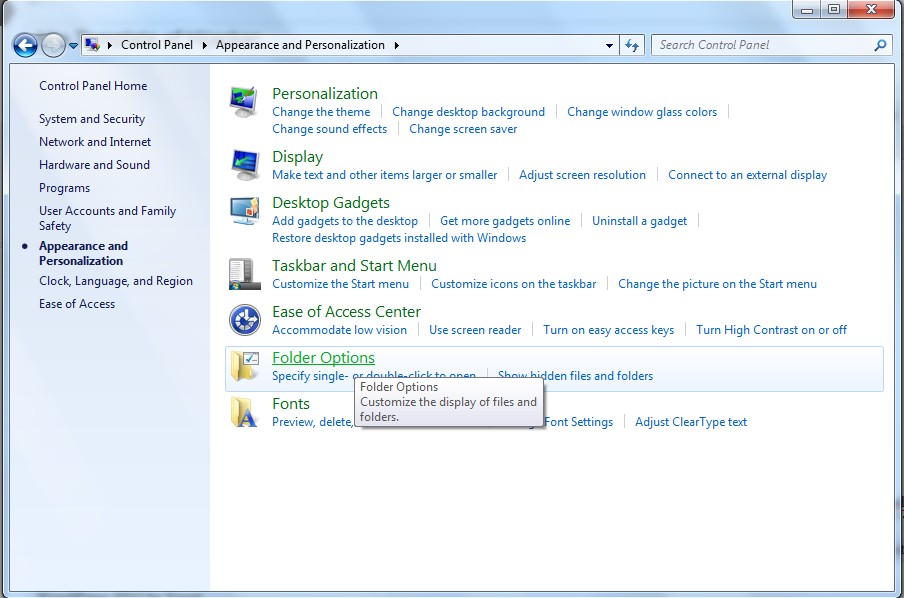
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
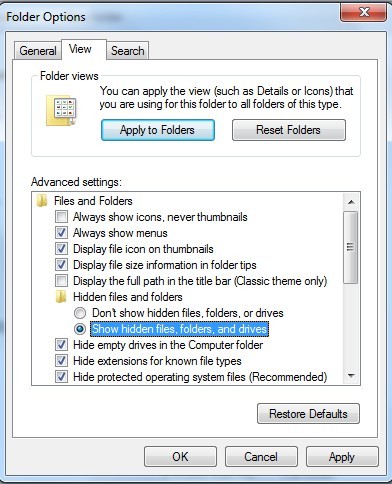
(6). Click OK at the bottom of the Folder Options window
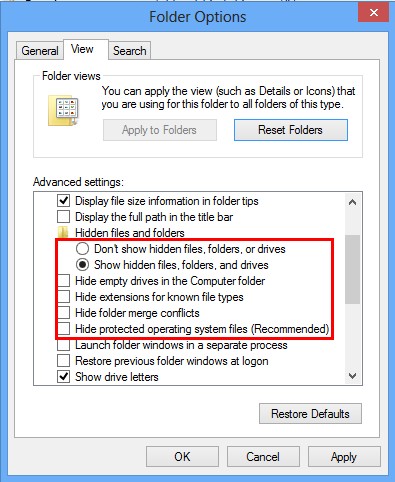
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
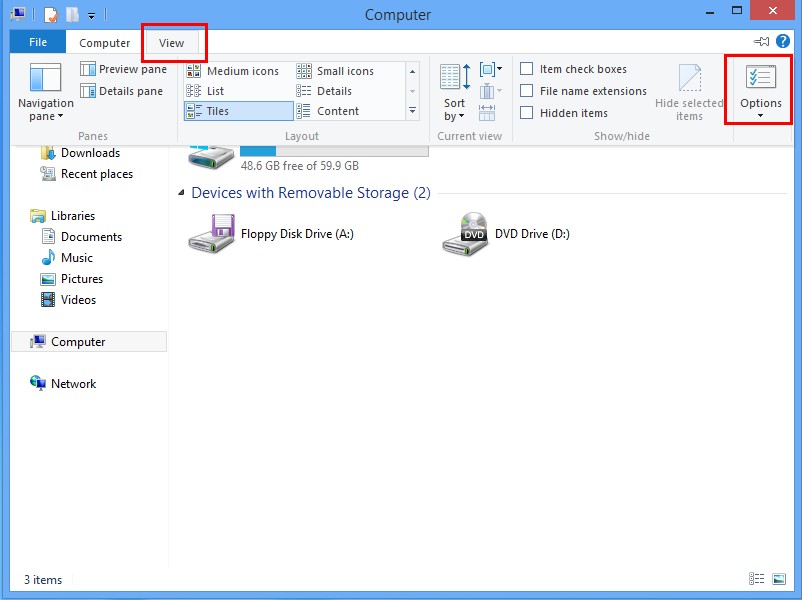
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
3. Delete Relevant Registry Entries and Files
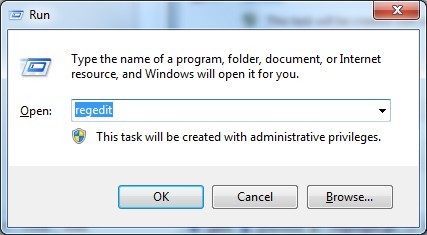
(1). Delete the registry entries of Win32.ZAccess.ewjg through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
While the Registry Editor is open, search and delete the related registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files.
%AllUsersProfile%\random.exe
%AllUsersProfile%\Application Data\random
%AllUsersProfile%\Application Data\~random
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
In short, Win32.ZAccess.ewjg is a high risky Trojan virus. It is designed by cyber criminals that spreads around the world and damages the target computer seriously. If you are not careful when surfing on the Internet, you will make the computer stay in danger. It is so complex and stubborn that no antivirus program can solve it. Computer and Internet are indispensable tools for modern people in learning, entertainment and work, so there are a lot of valuable data in the computer. The cyber criminals are interesting in these valuable data. The computer that is infected with this Trojan is not safe anymore. Therefore, in order to protect your computer and privacy, please get rid of it as soon as possible.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on December 26, 2013 1:39 pm, last updated on December 26, 2013 1:39 pm



Leave a Reply
You must be logged in to post a comment.