Your browser is redirected to Default-Search.net? It takes over your homepage as well as search engine? You have no way to browse web pages normally? All of these annoying problems are caused by this browser hijacker. Why does it appear on your computer suddenly? What kind of impact will it bring to your browser and system? If you do not want to use it, what can you do in the case that the antivirus software cannot help?
Default-Search.net is a notorious browser hijacker that has the ability to tamper with browser settings and replace your default homepage as well as search engine with its own website. As a new member of the browser hijacker family, it is also able to disguise as or hide in some free third party software, website plug-ins and attractive advertisements, which gives it a chance to entice users to download it to the computer. It is busy in making a lot of troubles and degrading system performance on the target computer. The most obvious symptom is that you cannot use your favorite website as the homepage and cannot search for information successfully. Whenever you want to access web pages or search for information, you will be redirected to other suspicious websites. It also shows you many advertisements. You must be wondering why the advertisements it brings are just related to the things you are concerned about. That is because it has the ability to collect your search records and track your browsing history quietly.
First of all, many annoying problems will occur on the target computer constantly including slow Internet speed and bad computer performance. Keeping waiting and waiting when you are using the browser becomes inured to the unusual. Many users have emergency work that needs to be handled urgently such as receiving and sending emails, but they just can go crazy because this hateful Default-Search.net browser hijacker controls the browser completely. Besides, the search results it provides mostly are dangerous things. Although you always remain circumspect, but if you accidentally click on these search results, your computer will be invaded by other threats such as spyware, keyloggers and Trojan viruses easily. Obviously, the data you store in the computer including files, pictures, programs and online banking information are not safe. To keep your computer safe, you should remove this browser hijacker timely. With its advanced technology, it can always bypass the antivirus programs. Therefore, if your computer is affected, you need to clean it up manually.
1. It is able to become the startup page of your web browser via modifying browser settings. No matter which browser you are using (Internet Explorer, Safari, Google Chrome, Mozilla Firefox or Opera), you can see the browser is occupied by it completely.
2. It may also install plug-ins, extensions and toolbars in the browser so as to record your search history as well as cookies.
3. You need to wait for a long time when visiting websites because the browser always gets stuck and is slow in reaction.
4. This annoying redirect may also result in unstable Internet connection and system freezes frequently.
5. You are forced to receive many advertisement windows when the computer is connected to the Internet.
Default-Search.net has the ability to change the default browser settings and redirect you to random sites (usually sites playing unreliable advertisements or even containing virulent Trojan viruses, spyware and other infections). You may have noticed that most browser hijackers won’t be detected by antivirus programs. The same goes to this one. Its considerable visitor volume benefits numerous product manufacturers, freeware developers and website promoters, thus, they are willing to maintain long-term relationship with it. Actually, the main reason for the failure detection of antivirus programs is its successful disguise. Through making use of advanced technology, it maintains the ability to combine its components with system files or to generate fake system files, which confuses computer users as well as antivirus programs. They cannot identify it accurately and timely, let alone remove it thoroughly. Therefore, manual removal is the best choice to drive it away from your computer. In this case, you are advised to delete every file generated by it manually so as to spare all later trouble. The manual removal needs to be handled carefully so as to avoid any subsequent damages. Users can follow the manual guide here to have the hijacker removed instantly.
1. Clean Add-ons and Extensions
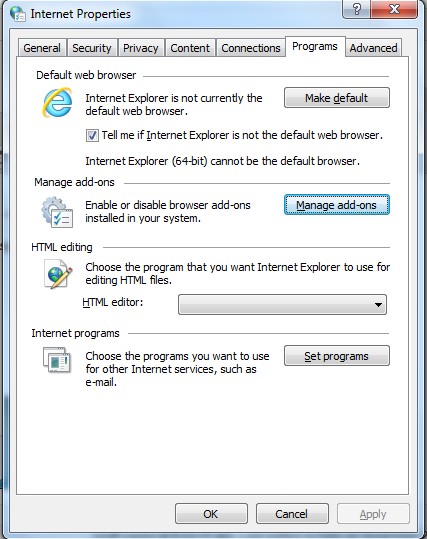
* Internet Explorer:
(1). Click Tools in the Menu bar and then click Internet Options
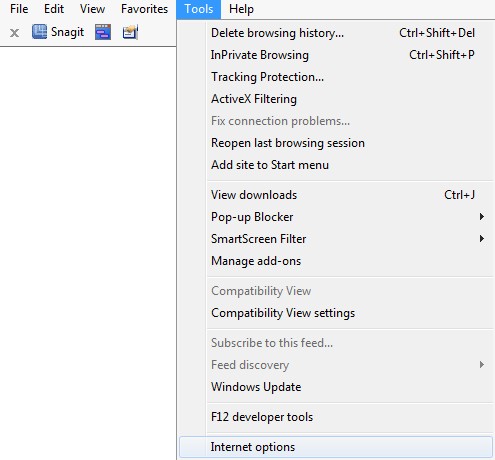
(3). Click Programs tab, click Manage add-ons and disable the suspicious add-ons
* Firefox:
(1). Click Tools in the Menu bar and then click Add-ons
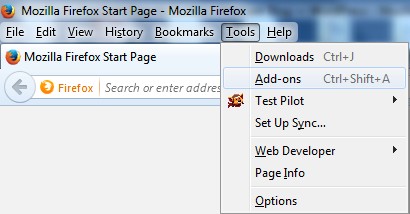
(2). Click Extensions, select the related browser add-ons and click Disable
* Google Chrome:
(1). Click Customize and control Google Chrome button → Tools → Extensions
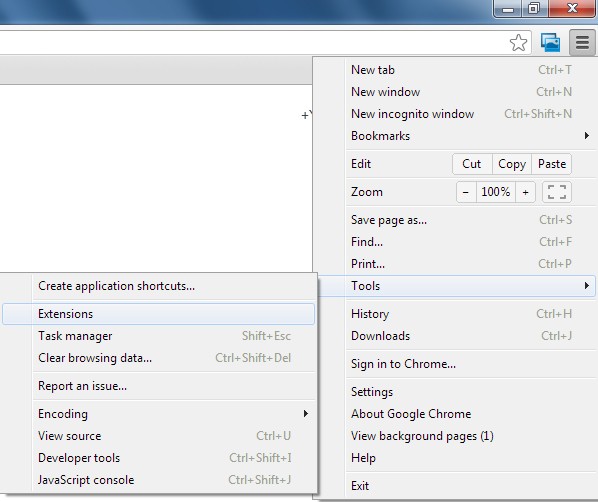
(2). Disable the extensions of Default-Search.net
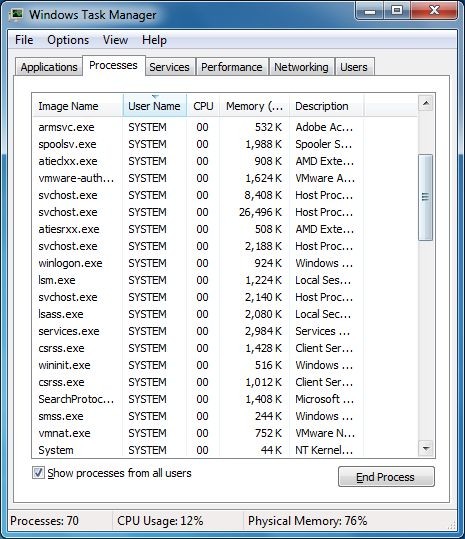
2. End Relevant Processes
(1). Press Ctrl+Shift+Esc together to pop up Windows Task Manager, click Processes tab
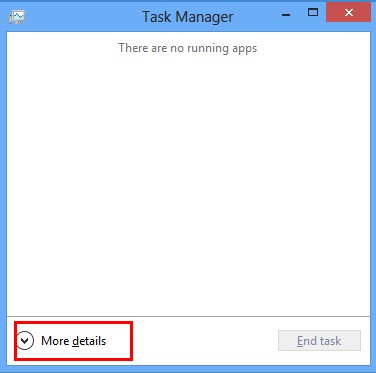
*For Win 8 Users:
Click More details when you see the Task Manager box
And then click Details tab
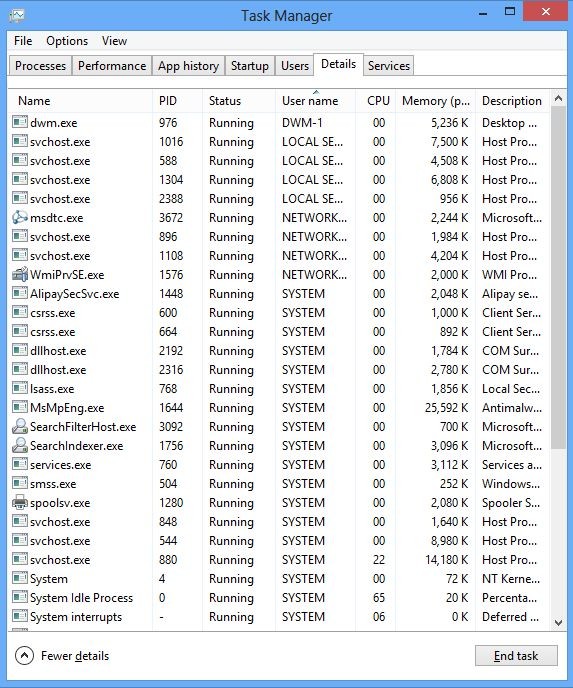
(2). Find out and end the processes of Default-Search.net
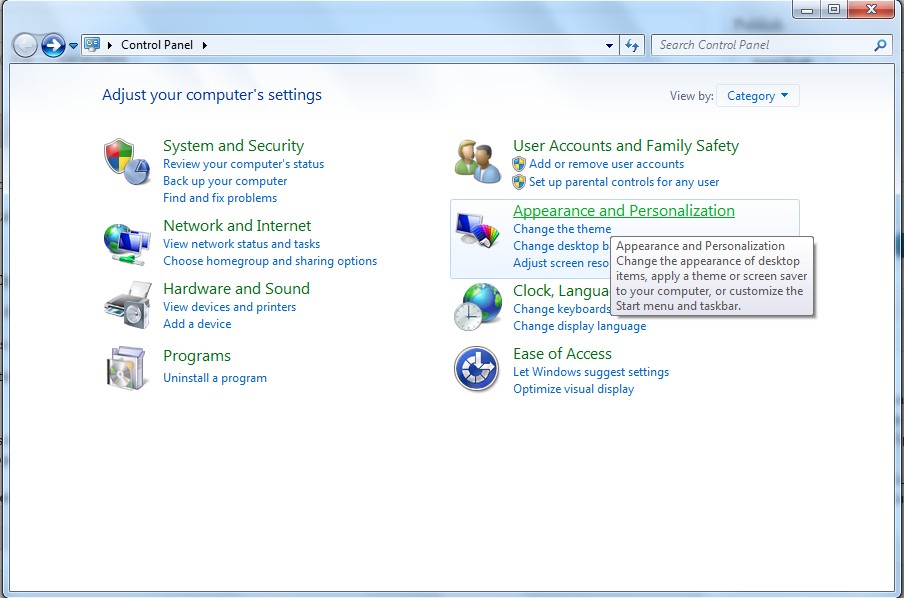
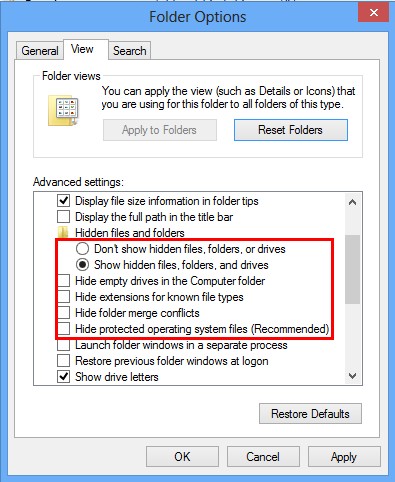
3. Show Hidden Files
(1). Click on Start button and then on Control Panel
(2). Click on Appearance and Personalization
(3). Click on Folder Options
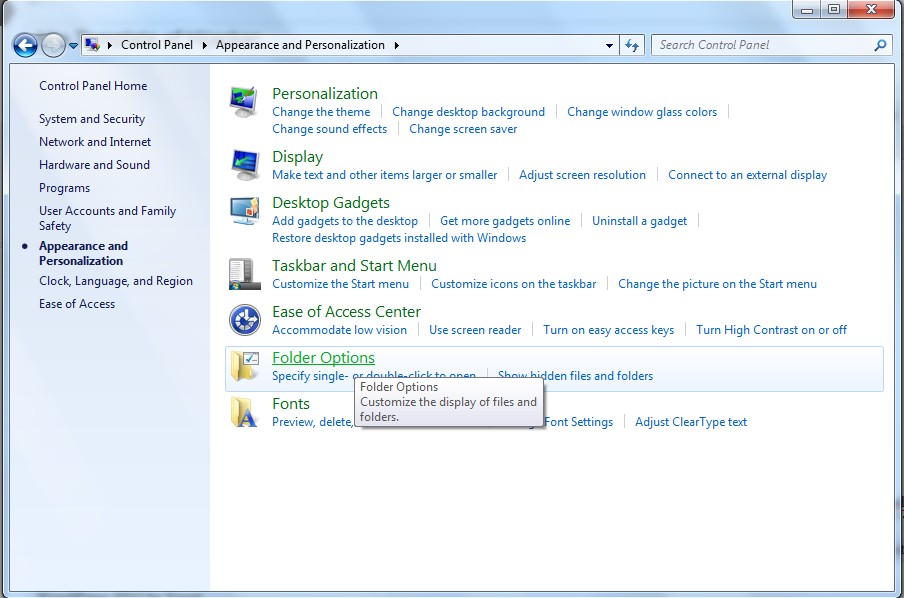
(4). Click on the View tab in the Folder Options window
(5). Choose Show hidden files, folders, and drives under the Hidden files and folders category
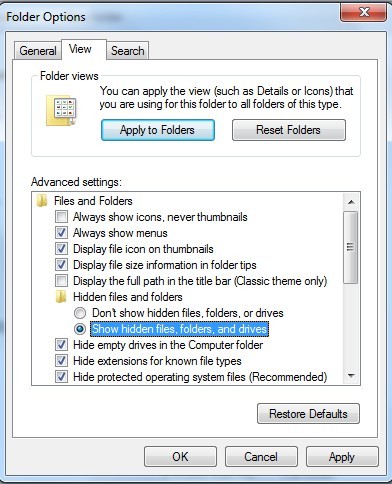
(6). Click OK at the bottom of the Folder Options window
*For Win 8 Users:
Press Win+E together to open Computer window, click View and then click Options
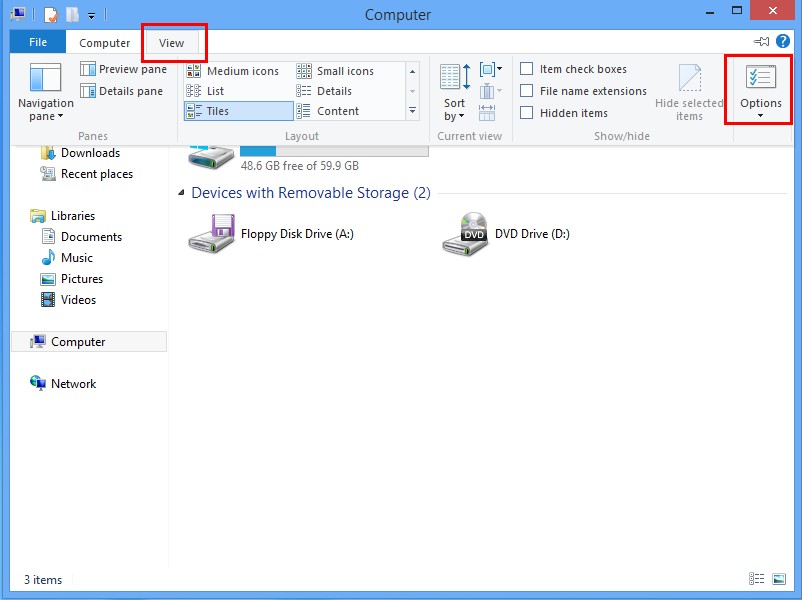
Click View tab in the Folder Options window, choose Show hidden files, folders, and drives under the Hidden files and folders category
4. Delete Relevant Registry Entries and Files
(1). Delete the registry entries of Default-Search.net through Registry Editor
Press Win+R to bring up the Run window, type “regedit” and click “OK”
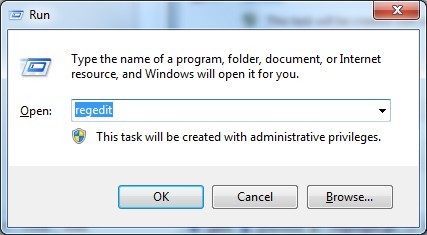
While the Registry Editor is open, search and delete the related registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\run\Random.exe
(2). Find out and remove the associated files.
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Default-Search.net is a browser hijacker which disguises as a search engine. It focuses on hunting careless computer users for their computer has huge loopholes. Furthermore, we do not deny that there are many other computer users who treat their own computer seriously still becoming its targets because it is very tricky. It is hidden in some unsafe free programs. When you install these programs, it is able to access to your computer and the installation process is catfooted. After embedding in the target computer, it will create a lot of troubles to disturb your online activities. It changes some of the main features of the computer, including the DNS settings. In this case, your browser will be redirected to its own website and many other unknown malicious domains. Then, unfamiliar advertisements and fake alarms may appear on your screen suddenly. If you want to use your computer safely, you should keep Default-Search.net out of your computer.
The above manual removal is quite dangerous and complicated, which needs sufficient professional skills. Therefore, only computer users with rich computer knowledge are recommended to implement the process because any errors including deleting important system files and registry entries will crash your computer system. If you have no idea of how to process the manual removal, please contact experts from YooCare Online Tech Support for further assistance.
Published by on December 24, 2013 1:50 pm, last updated on December 24, 2013 1:50 pm



Leave a Reply
You must be logged in to post a comment.