Having Trojan Horse Back Door.Generic122.BQZD in my computer, what can I do? This virus is severely disturbing my daily life because it takes over the entire free room of the RAM that stops almost all the programs in my computer so I cannot run them correctly. I cannot use programs to remove it, is there any other effective way to remove it completely?
Trojan Horse Back Door.Generic122.BQZD is categorized as a nasty back-door virus of Trojan horse family which has a notorious repute. Its main function is to open a back door on the target PC to allow hackers steal important personal information on the victim system. If it is successfully allowed to open a loophole on the infected system, it will secretly connect the infected PC with certain malicious servers to allow malicious remote controlling and allow hacked program being installed. If you let this happen, it is just like opening a back door to invite thieves into your house.
As a nasty virus, it is created by the hacker to degrade security levels and intrudes more threats into the victim computer. It changes computer settings secretly to allow it to hide in registry entries which would makes it more difficult to be removed by software and allow it to act automatically as the system launches. It may lead you to unsafe site to bring in other members in Trojan family. It makes you suffer from financial losses when it has successfully changes your data back to its creators. It creators may copy your bank info and password and record each key stroking so that they can use your credit card to scam money. It’s Primary function is to violate your privacy and steal your personal info so that hackers can earn money from your important files. Leaving this virus in your computer would not only damage your computer but also makes you losing money so it would be a wise choice to have it removed before further damages.
Trojan Horse Back Door.Generic122.BQZD allow cyber-criminals to break into the infected computer without noticed and disables executable program and cause system crash. It changes important computer settings to allow remote control from cyber criminals. It will modify your registry settings and important key value to make it difficult to be removed. It accesses your data, your tabs and browsing activity on all websites and is able to cause system crash and disable your executable programs. Meanwhile, it drops some other threats including malware, adware parasites and spyware into your computer.
Manual removal is a complicated and risky process, so please back up all important data before making any changes on your computer. Here are some instructions to handle with the Trojan horse manually, and be cautious when going through the following steps.
1 Clear all the cookies of the affected browsers.
* Google Chrome: Click on the Tools menu → select Options → Click “Under the bonnet” tab → locate “Privacy” section → browsing data” button → “Delete cookies and other site data” to delete all cookies from the list.
* Internet Explorer: Click “Tools” → Click “safety” → “delete browsing history” → Tick “cookies” box and click delete
* Firefox:: Click “Tools” → Click “Options” → Click “Privacy” → Click “remove individual cookies”
2 Remove all the add-ons and extensions.
* Google Chrome:
(1). Click the Customize and Control menu button →Tools→ click Extensions
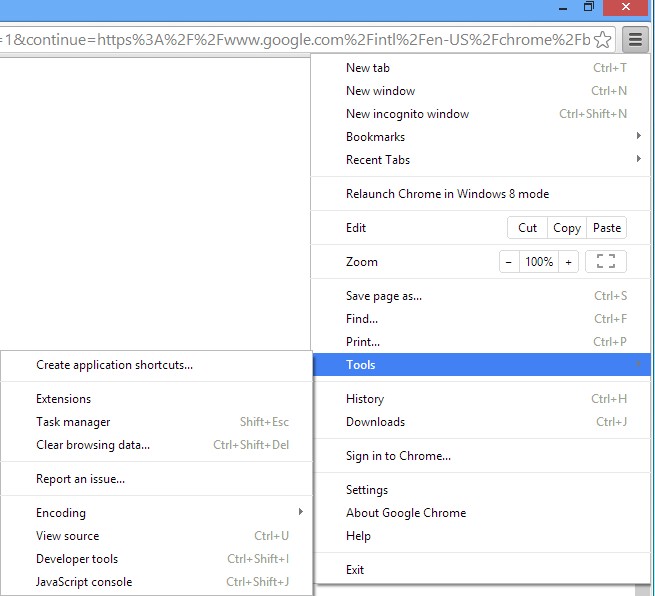
(2). Select the related Extension and click Disable.
* Internet Explorer:
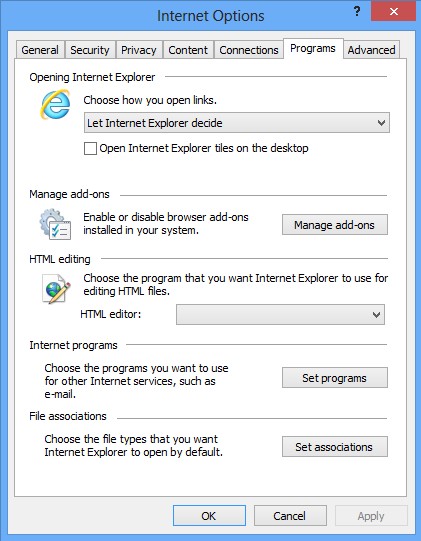
(1). Click Settings → Click Manage Add-ons
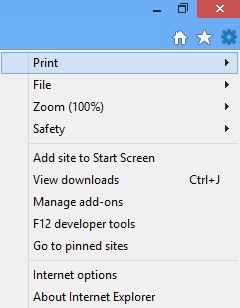
(2). Click Programs tab → Click Manage Add-ons → Disable all the suspicious add-ons.
* Firefox:
(1). Click the Firefox menu and click Add-ons
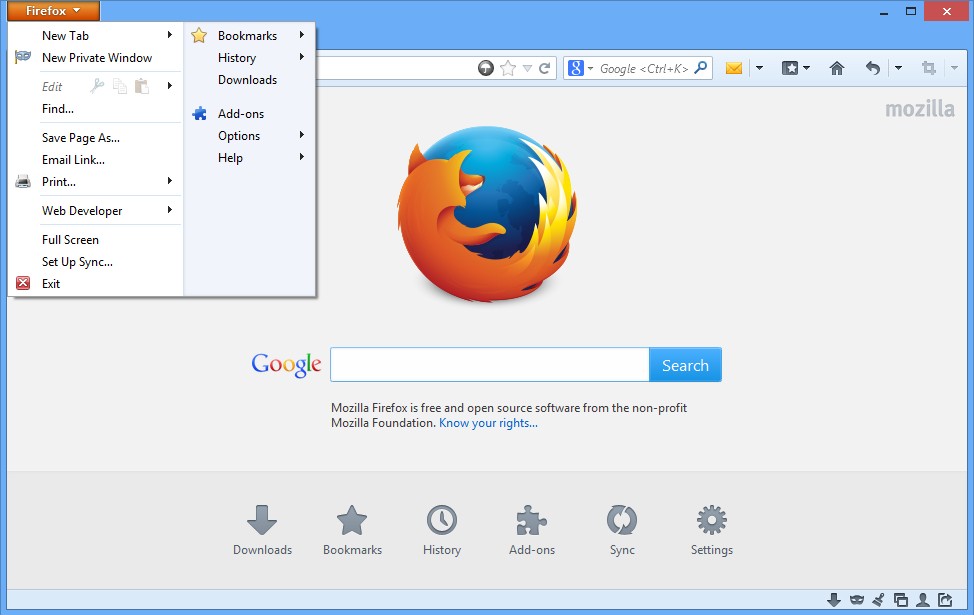
(2). Click Extensions, select the related browser add-ons and click Disable.
3. Show Hidden Files
(1). Press Win+R to get run option
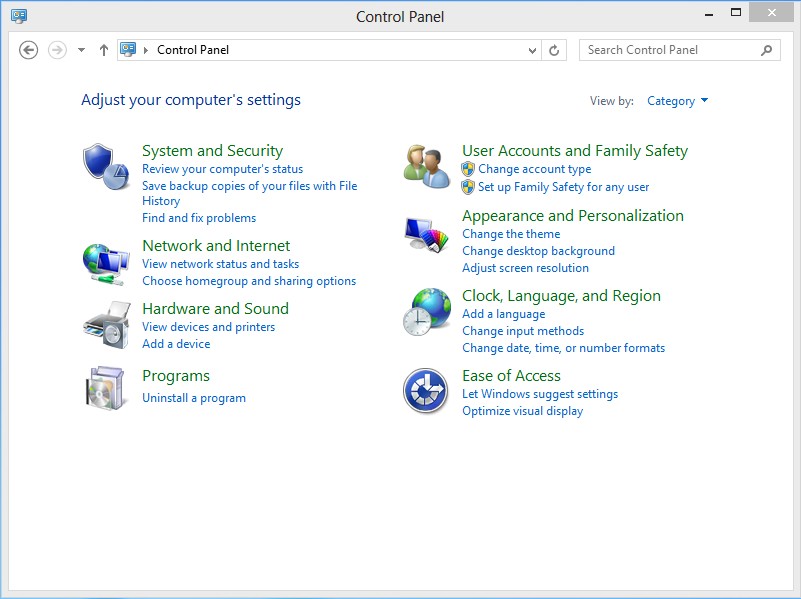
(2). Type in Control Panel and hit enter to get Control Panel
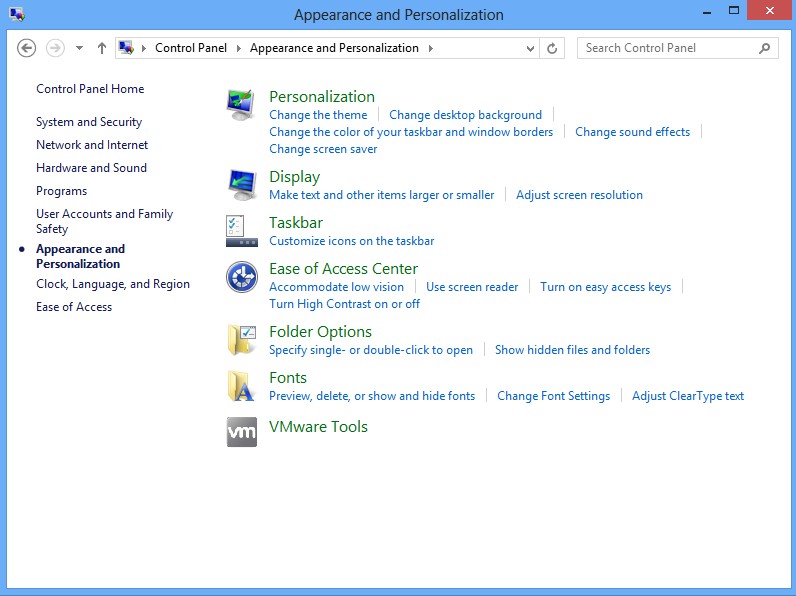
(3). Click on Appearance and Personalization link
(3). Click on Folder Options link
(4). Click on View tab in Folder Options window
(5). Tick Show hidden files, folders, and drives under Hidden files and folders tab
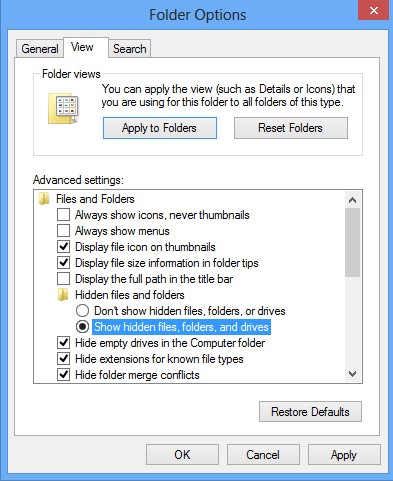
(6). Click Apply to effect, then click OK at the bottom of the Folder Options window.
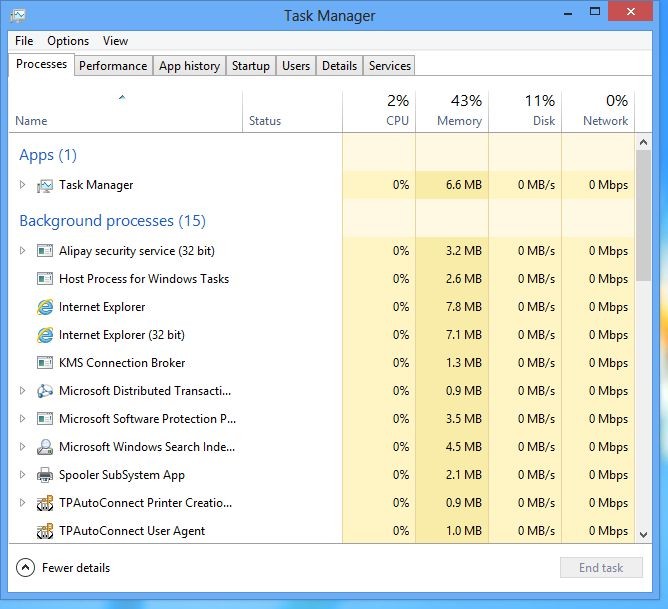
4 stop virus processes in the Windows Task Manager.
(1). Press Ctrl+Alt+Del keys together to get Windows Task Manager
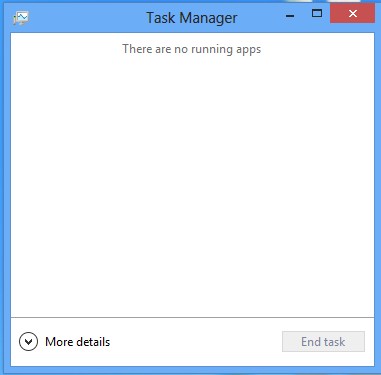
(2). Click More details
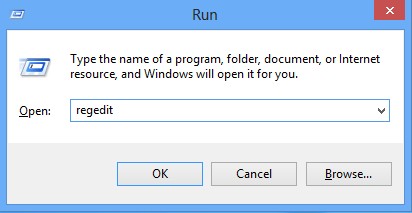
5. Remove all the malicious files registry entries through Registry Edit.
*Trojan Horse Back Door.Generic122.BQZD is a malicious Trojan virus which implants itself to the infected computer secretly and makes your computer and other working process slowly during infection. It can install the itself into the computer system without your awareness and consciousness. To make matters worse, the Trojan is used as a tool for hackers to achieve hacking purpose to steal your information. It is recommended to remove it with a complete and fast procedure. Users can follow instruction here to have it manual deleted instantly.
(1). Using Registry Editor to delete all the related registry entries.
*Guides to open Registry Editor:
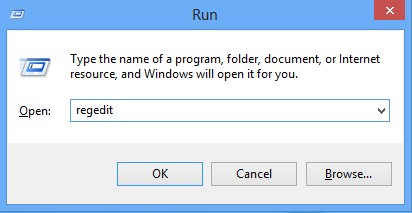
Press Win+R key together then Registry Editor will pop up.
(2). Find out and remove the associated files of Back Door.Generic122.BQZD.
Under normal circumstances, Trojan Virus Back Door.Generic122.BQZD will sneak into the target computer secretly via malicious files or spam mail attachment or forbidden access from hacked website. It will hide in the registry of the infected system to make sure that no programs can detect it trait. In addition, this Trojan horse virus can record the user’s on-line activities, such as the screen shot, browsing history so as to collect the victim’s valuable personal information on the infected computer then sent to an unknown network hacker that people cannot trace to. If you have seen the virus is working on your system, you need to completely remove Trojan Horse Back Door.Generic122.BQZD and its related files immediately because instant removal is very important and urgent.
Friendly Reminder:
If you still find it hard to follow the removal guide above, please contact YooCare: PC experts 24/7 online will offer you the most effective tech support to remove infection completely.
Published by on December 23, 2013 10:10 am, last updated on December 23, 2013 10:10 am



Leave a Reply
You must be logged in to post a comment.