I have got Idle Rootkit infection on my laptop. Yesterday I scanned my laptop for rootkits and it alerted a hidden file named IDLE. The scan report said that it need to be deleted before more damages but it seems that I failed. I have tried to remove it for many times, but it’s not gone. It keeps coming back to my laptop after a fully restart. What is this hidden “IDLE” Rookit virus? Should I be concerned and is there an effective way to get rid of it successfully?
Idle Rootkit is vicious rootkit virus which disguise as a normal system hidden file. It is a malignant virus which spreads widely, the networked world. The virus belongs to the popular Trojan virus family which attracts people to download it, and then open the portal of the infected computer to allow other viruses’ entrance. Quite dislike other kinds of viruses, this virus will replicate malicious registry entries and deliberately infected files stored in the infected system. This nasty virus replaces system files to a leaky one. Then it starts to disable task manager; inactivate anti-virus program; removed executable program in a USB thumb drive after you have inserted into the infected computer to make sure that no security programs can remove it completely. Allowing remote control from cyber criminals drops the entire computer into a dangerous situation.
The Rootvirus is a data theft and a Botnet on the mainstream server. The main purpose of this kind of Trojan is stealing some computer data from target users. It is hard to be avoid if we don’t have good on-line habit. It hides behind some malicious resources like unsafe website, pirated freeware, spam mail attachment or unsafe downloading links. Because of it is able to track computer activity to collect sensitive information it wants such as credit card number or password information on the infected PC. it is rated as one of the most dangerous virus on world wide web. Critical system files will be corrupted by this virus. it will run itself automatically and allow other malicious software getting into the infected computer to work together, because we all know the Trojan virus always bring other malware to aggravating the infection. Not all the attachments in the emails are safe, if you click on unknown spam mail attachments incautiously, it will bring the virus into the victim’s PC and add to the system registry. However, if the computer has been infected and you have no way to remove it, please try to use manual removal method. This method is the most effective way to remove Idle Rootkit in yourPC.
Idle Rootkit allow cyber-criminals to break into the infected computer without noticed and disables executable program and cause system crash. It changes important computer settings to allow remote control from cyber criminals. It will modify your registry settings and important key value to make it difficult to be removed. It accesses your data, your tabs and browsing activity on all websites and is able to cause system crash and disable your executable programs. Meanwhile, it drops some other threats including malware, adware parasites and spyware into your computer.
Manual removal is a complicated and risky process, so please back up all important data before making any changes on your computer. Here are some instructions to handle with the Trojan horse manually, and be cautious when going through the following steps.
1 Clear all the cookies of the affected browsers.
* Google Chrome: Click on the Tools menu → select Options → Click “Under the bonnet” tab → locate “Privacy” section → browsing data” button → “Delete cookies and other site data” to delete all cookies from the list.
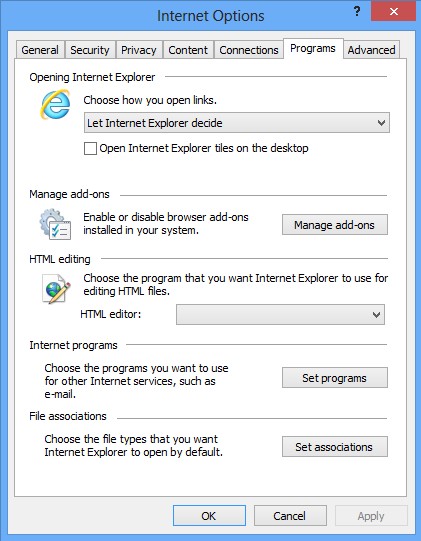
* Internet Explorer: Click “Tools” → Click “safety” → “delete browsing history” → Tick “cookies” box and click delete
* Firefox:: Click “Tools” → Click “Options” → Click “Privacy” → Click “remove individual cookies”
2 Remove all the add-ons and extensions.
* Google Chrome:
(1). Click the Customize and Control menu button →Tools→ click Extensions
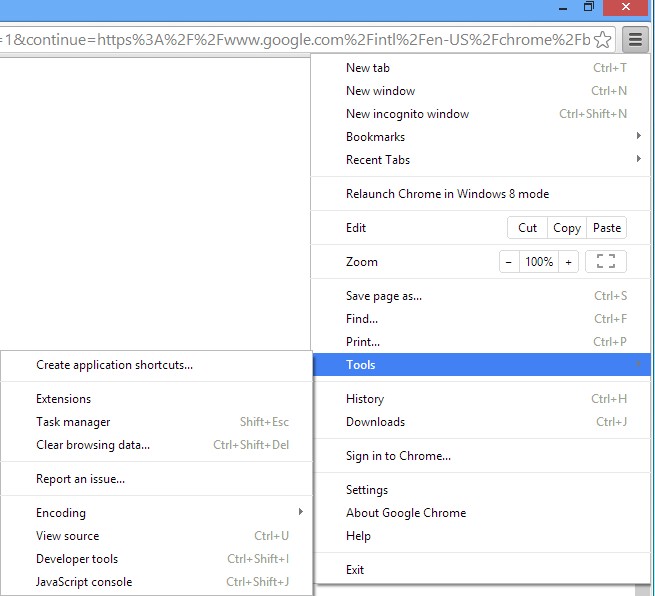
(2). Select the related Extension and click Disable.
* Internet Explorer:
(1). Click Settings → Click Manage Add-ons
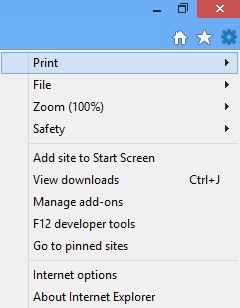
(2). Click Programs tab → Click Manage Add-ons → Disable all the suspicious add-ons.
* Firefox:
(1). Click the Firefox menu and click Add-ons
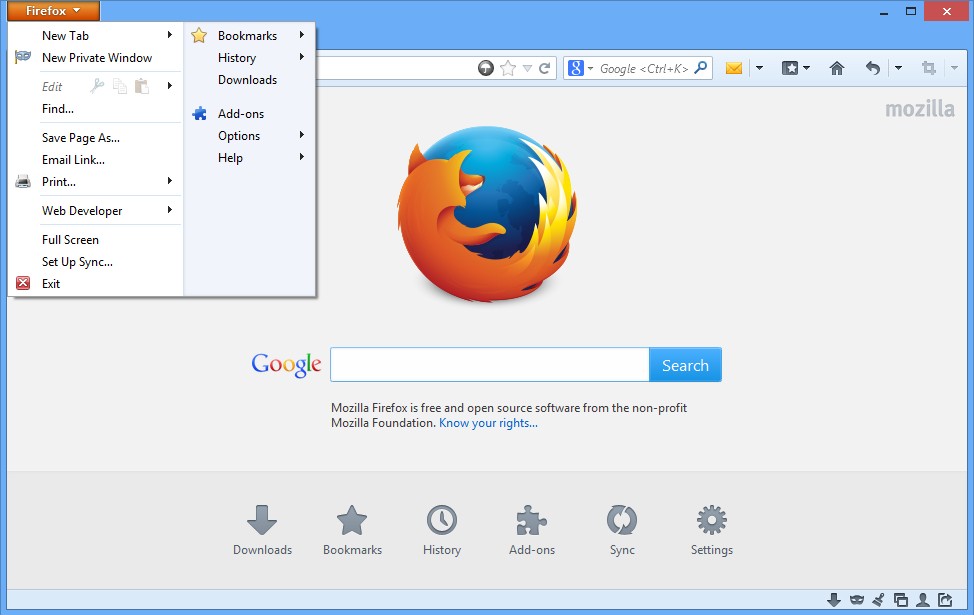
(2). Click Extensions, select the related browser add-ons and click Disable.
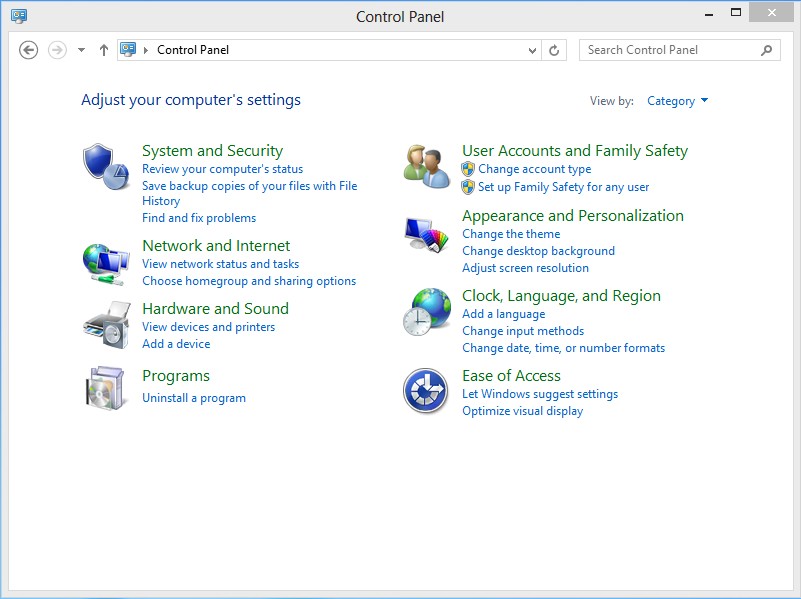
3. Show Hidden Files
(1). Press Win+R to get run option
(2). Type in Control Panel and hit enter to get Control Panel
(3). Click on Appearance and Personalization link
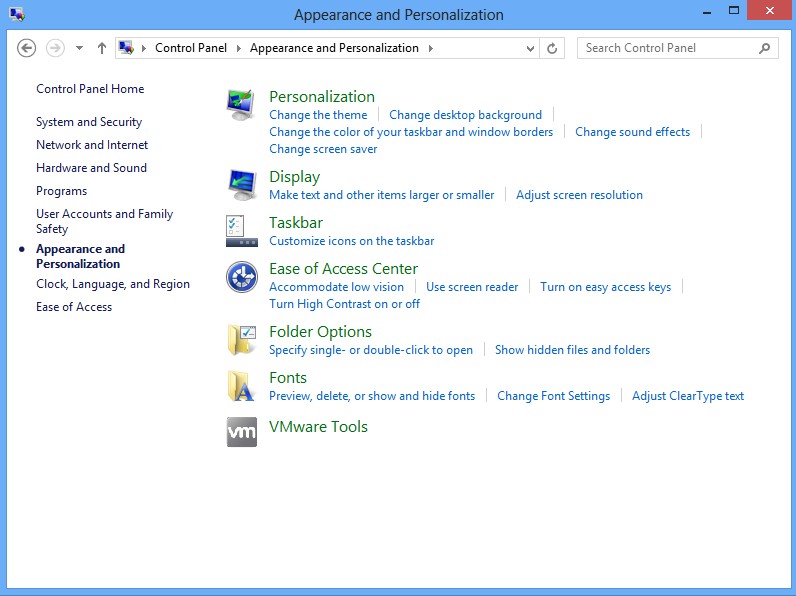
(3). Click on Folder Options link
(4). Click on View tab in Folder Options window
(5). Tick Show hidden files, folders, and drives under Hidden files and folders tab
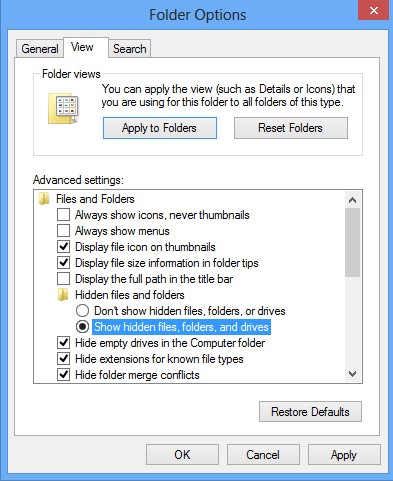
(6). Click Apply to effect, then click OK at the bottom of the Folder Options window.
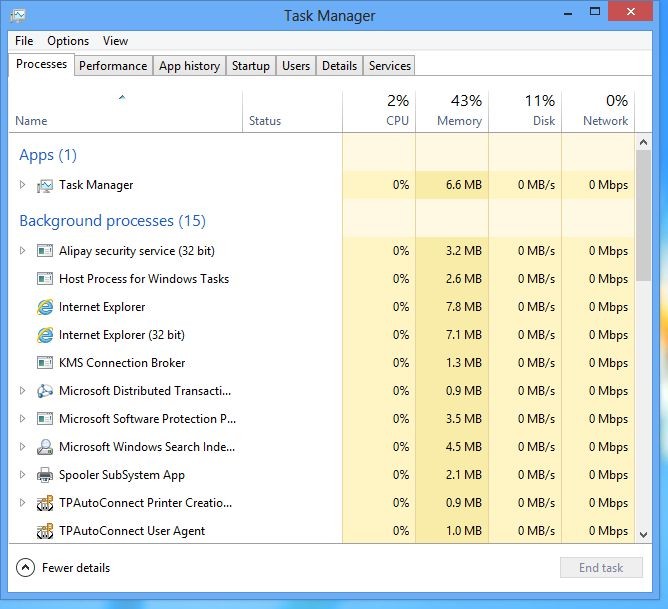
4 stop virus processes in the Windows Task Manager.
(1). Press Ctrl+Alt+Del keys together to get Windows Task Manager
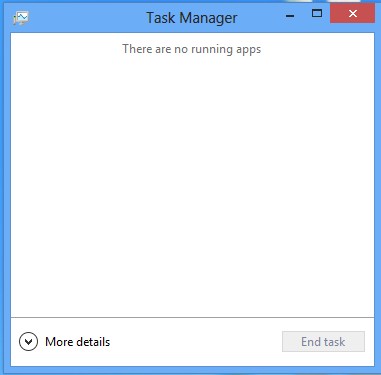
(2). Click More details
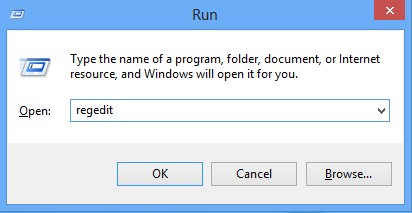
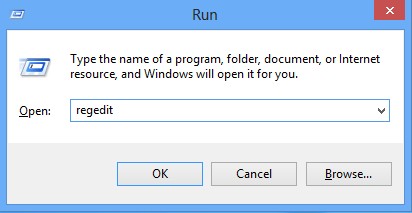
5. Remove all the malicious files registry entries through Registry Edit.
*Idle Rootkit is a malicious Trojan virus which implants itself to the infected computer secretly and makes your computer and other working process slowly during infection. It can install the itself into the computer system without your awareness and consciousness. To make matters worse, the Trojan is used as a tool for hackers to achieve hacking purpose to steal your information. It is recommended to remove it with a complete and fast procedure. Users can follow instruction here to have it manual deleted instantly.
(1). Using Registry Editor to delete all the related registry entries.
*Guides to open Registry Editor:
Press Win+R key together then Registry Editor will pop up.
(2). Find out and remove the associated files of XX.
Friendly Reminder:
Idle Rootkit is a malicious process that can damage the infected computer by different way, not only can it modify the system settings but also download other viruses from the unsafe website. The cyber criminals have the ability to invade the infected machine to steal the information and personal data, the security programs can be closed completely due to this nasty process. Since the anti-virus program can not handle this malicious process well, it is strongly suggested that PC users should remove it quickly and manually.
If you still find it hard to follow the removal guide above, please contact YooCare: PC experts 24/7 online will offer you the most effective tech support to remove infection completely.
Published by on December 13, 2013 1:50 pm, last updated on December 13, 2013 1:50 pm



Leave a Reply
You must be logged in to post a comment.