My computer gets Win32/bitcoinminer.AF Trojan horse virus infection when I open a spam E-mail attachment, my AVG warns me this virus infection and removes it immediately, however, when I restart my computer, this Trojan horse appears again. It seems that the anti-virus program can not handle this virus infection completely. How can I remove it from my computer? Any help will be appreciated.
Win32/bitcoinminer.AF Trojan horse is a malicious process attacks the PC users’ computers by many ways, usually free program, spam E-mail attachment and .exe process can be planted to this Trojan horse, once the PC users open these infected file, Win32/bitcoinminer.AF will be able to invade the infected machine easily. The PC users wouldn’t notice the virus infection unless anti-virus program warns them, however, it has the ability to escape from the tracking of the anti-virus program, anyway, this Trojan horse is extremely dangerous that the PC users need to remove it completely.
In general, this nasty Win32/bitcoinminer.AF Trojan horse can infect Windows XP, Vista, 7 and 8, once it has been installed to the infected PC, it can modify the system settings like homepage, desktop image and even the default browser. The infected PC will suffer other virus infection like browser hijack redirect, worm and even rough program due to this Trojan horse, it can even cause a slow performance including running slowly and freezing at all. Some PC users may face the blue death screen when they try to run some big programs or games, that is the reason this Trojan horse can be one of the most dangerous viruses on the Internet.
#The Trojan allows cyber criminals to visit your computer remotely without your consent.
#The Trojan is related to system crash and files fragmentation, and it can disable your executable programs.
#The Trojan redirects your specified websites to other harmful websites and changes your computer settings at random.
#It brings other types of threats to your computer such as malware, adware parasites and spyware.
#It records your browser history and computer data to violate your privacy and compromise security.
Malicious as the Trojan horse is, it takes your computer at great risk by damaging your system, files and programs. Also, this malicious Trojan corrupts your computer along with other types of threats like malware and spyware. Moreover, you will come across many unexpected troubles when surf the web, for example, the Trojan can redirect your web search results to hazardous contents. Even the best anti-virus software is also disabled and difficult to take effective to delete any type of viruses entirely. If you haven’t sufficient skills of handling with system files, please don’t delete anything that you are not sure. In this situation, manual removal is appreciated. Also, PC professionals online will help you delete the Trojan completely at a quick time.
Manual removal is a complicated and risky process, so please back up all important data before making any changes on your computer. Here are some instructions to handle with the Trojan horse manually, and be cautious when going through the following steps.
1. Press Ctrl+Alt+Del keys together and stop virus processes in the Windows Task Manager.
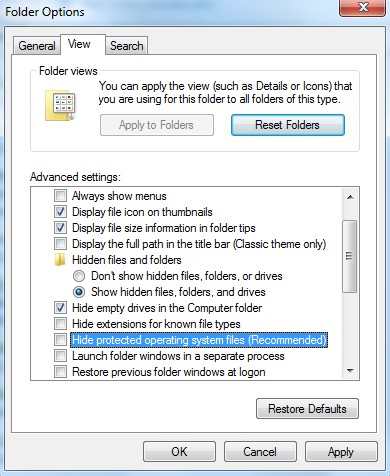
2. Go to Folder Options from Control Panel. Under View tab, select Show hidden files and folders and uncheck Hide protected operating system files (Recommended), and then click OK. Remember to back up beforehand.
3. Press Windows+ R keys and search for regedit in Run. Delete associated files and registry entries related to the virus from your PC completely as follows:
%AllUsersProfile%
%AllUsersProfile%\Application Data\~r
%AllUsersProfile%\Application Data\~dll
4. Reboot the computer normally to take effective, when the above steps are done.
As the above mentioned, Win32/bitcoinminer.AF is a high-risk process attacks the victims online, it can cause terrible situation on the infected PC. This nasty virus can run a backdoor process automatically so that the virus maker can get into the infected PC to collect information, important data like account’s number, password, Word and Excel can be stolen. Your history, cookies and even favorite can be viewed by the hijacker. If you see this virus on your PC, do not hesitate, there is one thing you need to do, that is to remove the virus immediately and completely.
If you have no idea how to do with that, please to contact experts from Yoocare Online Tech Support for further help.
Published by on November 14, 2013 4:04 am, last updated on November 14, 2013 4:04 am



Leave a Reply
You must be logged in to post a comment.