Recently, you notice that the performance of your computer is becoming increasingly worse. Some files disappear without rhyme or reason and computer often shuts down suddenly. At the same time, antivirus program keeps reporting to you that your computer has been contaminated by Trojan horse ZeroAccess.UG but cannot completely remove it, which drives you crazy. Trojan horse ZeroAccess.UG enters the computer through what way? You don’t want to lose your computer because there are a lot of valuable information in the computer. Then what to do to make computer back to normal?
Trojan horse ZeroAccess.UG is a new computer virus designed by cyber criminals which aims to invade your computer and collect your important information. It is spread to the rest of the world through the Internet. The Trojan is implanted into some fishing websites. If you are careless to visit these sites, it is automatically downloaded to your computer without showing you any notice or going through your license. In addition, it is able to access your computer through malicious programs or adware.
Once installed, Trojan horse ZeroAccess.UG immediately drops some malicious files into the registry entries of the target computer and self-replicates rapidly. Computer will suddenly shut down or restart, which causes damages to the hard drive. This virus may even cause blue screen and then result in loss of system data. As a Trojan virus, it can hide deeply in your computer and start a background download without your consent. At the very beginning when the computer just gets infected, the computer performance won’t change much so that you don’t realize the existence of the virus. However, as time goes on, you will be able to find that the computer running speed is slower and slower because more and more unfamiliar and unnecessary programs have been poured into the infected computer. The vast majority of those programs are malware, spyware and other files bundled with potential threats. You may note that some personal files are missing, and some new files with weird names appear. Other infections and viruses will also be able to invade the computer system easily resulting in greater damages. Worse still, by adding spyware on your computer, the cyber criminals who create the Trojan can monitor your online activities and collect your information for illegal use. The private information you put in the computer is not safe because those evil guys is able to steal these information arbitrarily. The Trojan is a high risky threat. In order to protect your computer, you need to remove it as soon as possible. Generally speaking, the antivirus program can detect its existence, but cannot fully kick it out of your computer. The locations and names of the infectious files change frequently to avoid the antivirus program. In this case, manual removal is the most effective way to deal with this problem.
1. It allows the virus makers to access your computer remotely without letting you know.
2. It is able to cause system crash and disable your executable programs.
3. It drops some other threats including malware, adware parasites and spyware into your computer.
4. It is capable of collecting your browsing history and other important data.
Trojan horse ZeroAccess.UG is a malicious Trojan virus which can install itself into the computer system without your consent and awareness. It makes your computer work slowly and implants other nasty infections into the computer. To make things worse, this Trojan is a tool for the hacker to invade the infected computer to steal your information. It is recommended to remove it as quickly as possible. Users can follow the manual guide here to have it removed instantly.
1. Show Hidden Files
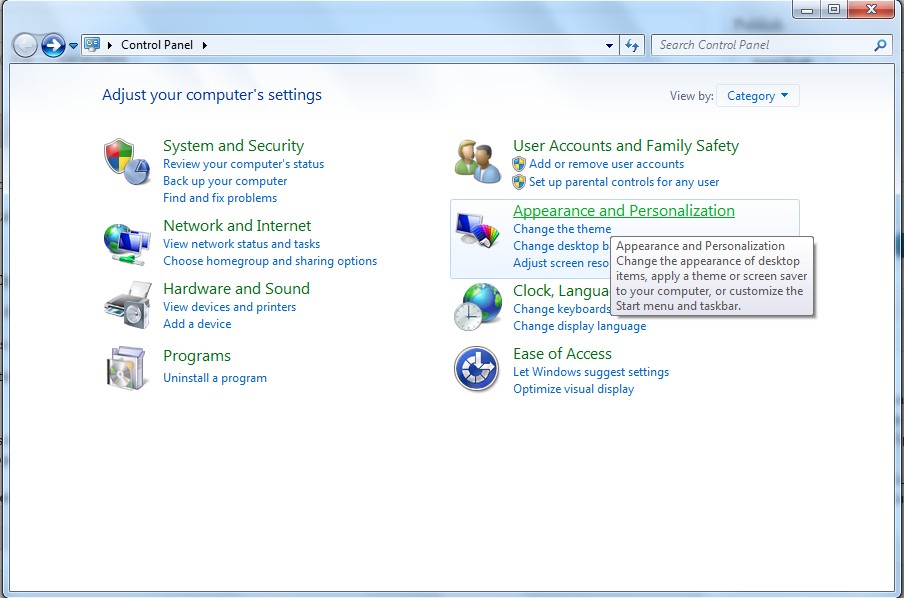
(1). Click on the Start button and then on Control Panel
(2). Click on the Appearance and Personalization link
(3). Click on the Folder Options link
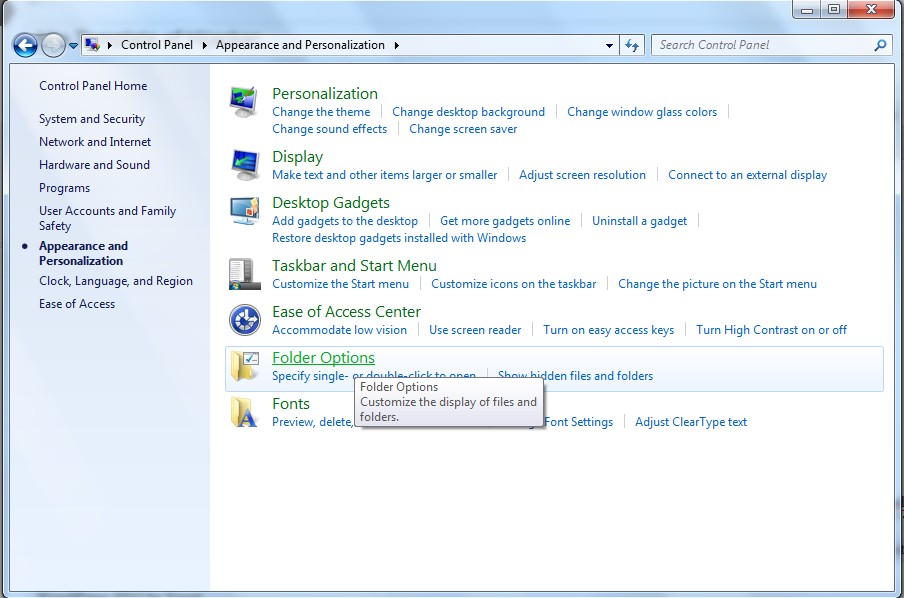
(4). Click on the View tab in the Folder Options window
(5). Choose the Show hidden files, folders, and drives under the Hidden files and folders category

(6). Click OK at the bottom of the Folder Options window.
2. Delete Virus Files
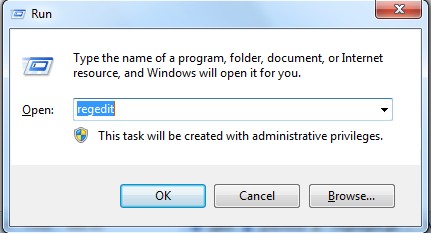
(1). Delete the related registry entries through Registry Edit
Guides to open registry editor: Click “Start” menu, hit “Run”, then type “regedit”, click “OK”
While the Registry Editor is open, search and delete the following registry entries listed below:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Random
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
(2). Find out and remove the associated files of this virus.
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
Trojan horse ZeroAccess.UG is a Trojan virus which has the ability to open a backdoor in the infected computer and cause many other problems. It connects the infected computer to the remote server, through which the cyber criminals is able to control your computer and steal your personal data. It is often bundled with some unknown free programs, which means the virus can enter a computer when you are downloading or installing these unknown programs from the Internet. In addition, spam email attachments and some unsafe websites including advertising sites or pornographic sites also contain the Trojan. It won’t be removed by antivirus programs since it is hiding in the computer system. In this case, manual removal is worth trying.
If you have no idea of how to do that, please contact experts from YooCare Online Tech Support for further help.
Published by on September 30, 2013 12:47 pm, last updated on September 30, 2013 12:48 pm



Leave a Reply
You must be logged in to post a comment.