Got infected with Trojan Horse Backdoor.Generic15.BYNL and do not know how to remove it completely? Does your anti-virus software perform normally to delete the virus entirely? If not, how to delete this nasty virus successfully and completely? Learn from this post and follow removal guide below to remove the Trojan horse safely.
Trojan Horse Backdoor.Generic15.BYNL is a very dangerous virus that can bring high risk to your infected computer. As its name suggested, it is mainly used to open a backdoor on the infected computer so that it can drop lots of adware or spyware into the infected computer and link up with hacker for further illegal purpose. It may permit to contact remote servers to download more harmful threats items to install into your system and enables hackers to use these to monitor the compromised computer remotely. t is created by remote attackers to violate your privacy and compromise your security by remembering your browsing history and computer data.
It may lead you to suffer a financial loss when it has successfully got into the infected computer, it starts to collect confidential information such as full name, email address, phone number and financial data. At the same time, it loads many evil progresses to run out of memory and has already reset the system default settings to allow its re-appearance constantly. Once installed, it will change your desktop background and show various fake security messages. It prevents normal programs from taking effective by destroying them. It can be able to redirect the users to malicious websites while you are surfing internet as well. Knowing its features can help you to explain why it always successfully escape from the removal of your antivirus tools and sneaked into your computer again and again.
Note: The following instructions require certain levels of computer skills. If you’re not sure how to delete this harmful Trojan, you can start a live chat with YooCare experts now.
※ It will allow cyber-criminals to break into the infected computer without noticed
※ It disables executable program and cause system crash
※ It will change your registry settings and key value which makes it hard to be removed
※ It will display numerous fake infections of exaggerated security threats
※ It violates your privacy and records your data in the infected computer.
Manual removal is a complicated and risky process, so please back up all important data before making any changes on your computer. Here are some instructions to handle with the Trojan horse manually, and be cautious when going through the following steps.
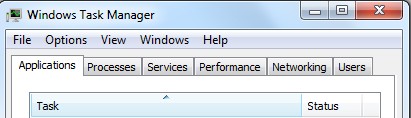
1. Press Ctrl+Alt+Del keys together and stop processes of this virus in the Windows Task Manager.
2. Go to Folder Options from Control Panel. Under View tab, select Show hidden files and folders and uncheck Hide protected operating system files (Recommended), and then click OK. Remember to back up beforehand.

3. Press Windows+ R keys and search for regedit in Run. Delete associated files and registry entries related to Trojan Horse Backdoor.Generic15.BYNL from your PC completely as follows:
%APPDATA%\[RANDOM CHARACTERS].js
%APPDATA%\[RANDOM CHARACTERS].pad
%USERPROFILE%\Start Menu\Programs\StartUp\runctf.lnk
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” = ’0′
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments “SaveZoneInformation” = ’1′
4. Reboot the computer normally to take effective, when the above steps are done.
Trojan Horse Backdoor.Generic15.BYNL is believed that once this infection is done, it will start messing with your computer and bringing more viruses and malicious programs to generally damage your computer. Once it has been detected on your computer, please be cautious and try to delete it as soon as possible. And please notice that it is not easy to find an effective way to remove because it is able to mess up the system files without trouble. What is worse, it is hard to be removed by anti-virus program. So PC user should consider manual way which is the most effective method to remove it.. It is designed by hackers to invade your computer remotely and aggressively.
Friendly Reminder:If you still find it hard to follow the removal guide above smoothly, please contact YooCare: PC experts 24/7 online will offer you the most effective tech support to remove infection completely.
Published by on June 9, 2013 5:17 pm, last updated on June 9, 2013 5:17 pm



Leave a Reply
You must be logged in to post a comment.