Don’t know how to remove Trojan agent2.bhto when you find that it is in your computer? What is Trojan agent2.bhto and how dangerous would it be? The infected computer works weirdly and very slowly like a snail? All versions of antivirus programs can detect the Trojan but cannot remove it completely? Learn more details about it from this post.
Trojan agent2.bhto is a destructive Trojan virus released by cyber criminals, which is able to attract computers all over the world and steal user’s confidential information via implanting more and more other threats into the computer. It may infiltrate into your computer via some unsafe free software, spam email attachments or malicious websites. You have no idea of the attack of this Trojan until you see the warning from the antivirus program.
Once installed successfully, Trojan agent2.bhto can modify important system settings and Windows Registry settings, which will keep itself active in the background every time you start the infected computer. It slows down the performance of the computer considerably by consuming system resources, which will greatly influence your work in the computer. What’s more terrible, this Trojan can implant some other threats into the computer which opens a backdoor for cyber criminals to monitor your online traces and collect your important data including bank account and credit card details. Therefore, you shall keep alert if you see it in your computer and take actions to have it removed as soon as possible before it destroys the computer.
Trojan agent2.bhto is tricky. It can root deep in the computer system, regenerate fast and inject its code into the legitimate antivirus programs to prevent itself from being removed. Though some antivirus programs may be able to block it temporarily, it will pop up again if it has not been removed completely. Thus, it needs and only can be removed manually with expert skills.
Trojan agent2.bhto is a malicious Trojan virus which can install itself into the computer system without your consent and awareness. It makes your computer work slowly and implants other nasty infections into the computer. To make things worse, this Trojan is a tool for the hacker to invade the infected computer to steal your information. It is recommended to remove it as quickly as possible. Users can follow the manual guide here to have this virus removed instantly.
1. Show hidden files
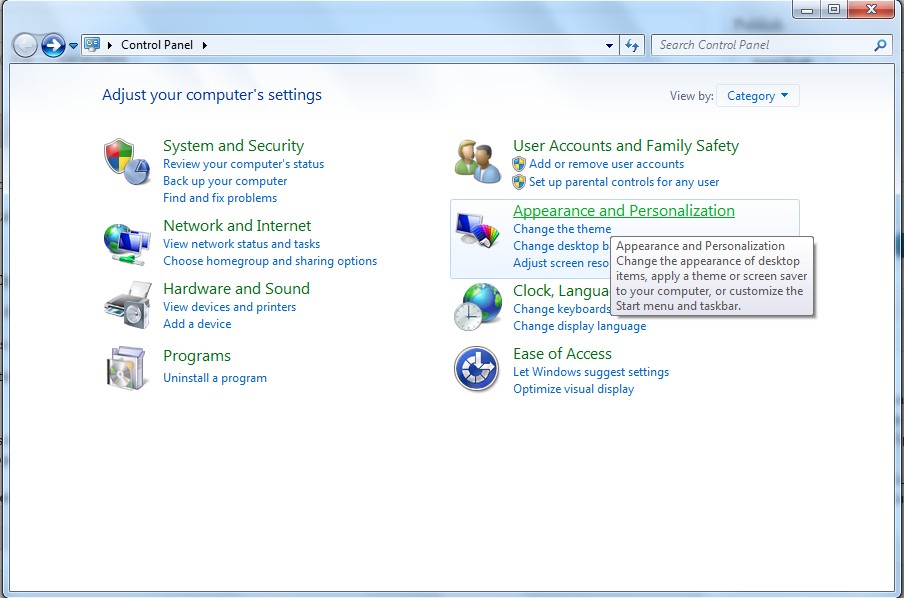
(1). Click on the Start button and then on Control Panel
(2). Click on the Appearance and Personalization link
(3). Click on the Folder Options link
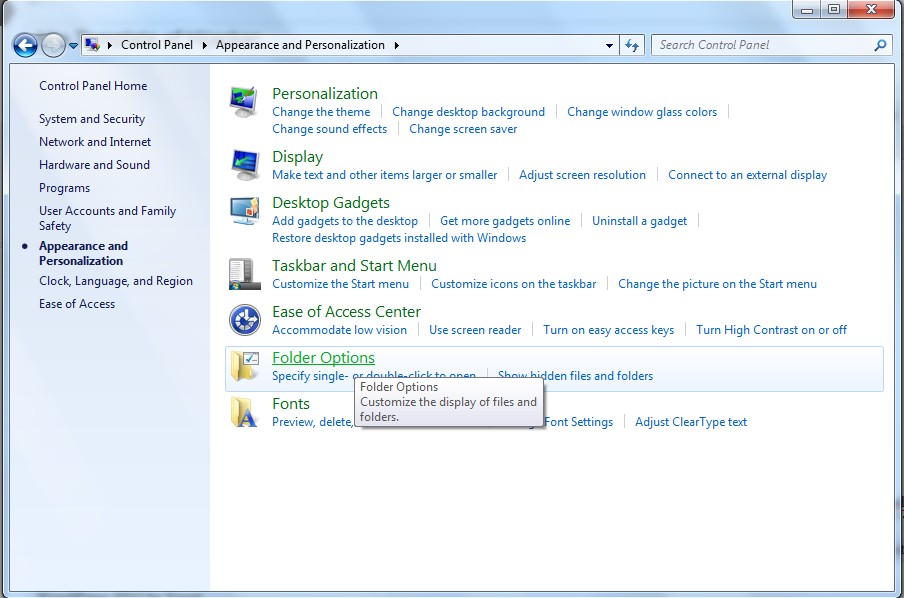
(4). Click on the View tab in the Folder Options window
(5). Choose the Show hidden files, folders, and drives under the Hidden files and folders category

(6). Click OK at the bottom of the Folder Options window.
2. Delete virus files
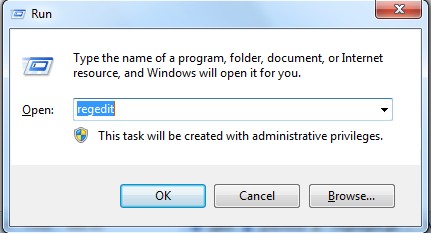
(1). Delete the related registry entries through Registry Edit
Guides to open registry editor: Click “Start” menu, hit “Run”, then type “regedit”, click “OK”
While the Registry Editor is open, search and delete the following registry entries listed below:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\[RANDOM CHARACTERS].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ‘Random’
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “CertificateRevocation” =Random
(2). Find out and remove the associated files of this Trojan virus.
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\.dll HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Random “.exe”
In summary, Trojan agent2.bhto is a malicious Trojan virus which can install itself into the computer without user’s awareness. It is quite hard for antivirus programs to remove this Trojan completely. It makes your computer perform slowly and implants other high-risk viruses into the computer. Besides, it allows the cyber criminals to access the infected computer to monitor your online behaviors and steal your sensitive information. We suggest you to get rid of it as soon as possible before more damages and losses.
If you have no idea of how to do that, please contact experts from YooCare Online Tech Support for further help.
Published by on May 28, 2013 10:08 pm, last updated on May 30, 2013 11:22 am



Leave a Reply
You must be logged in to post a comment.