All of these three viruses should be regarded as nasty browser hijacker infection. They are affiliated with browser hijackers and the ZeroAccess Rootkit that can infect a computer by exploiting security vulnerabilities. Generally speaking, such dangerous viruses are known to attack Firefox, Chrome and Internet Explorer, and can function in most versions of Windows, including Windows XP, Vista and Windows 7. It poses huge risk for all the compromised computers. Also these viruses are related to the notorious ” Welcome to nginx/404 not found Malware.”
This type of virus is able to compromise your web browser and change your default search engine and homepage. Once infected, the antivirus program you have installed such as Avast will start warning you with messages such as:
URL: hxxp://37.220.36.44/x/
Process: C:\Windows\System32\svchost.exe
Infection: URL:Mal
URL: hxxp://espeak911.com/x/
Process: C:\Windows\System32\svchost.exe
Infection: URL:Mal
URL: hxxp://colexity777.com/x/
Process: C:\Windows\System32\svchost.exe
Infection: URL:Mal
However, even these warnings keeps popping up every few seconds, you still can’t get rid of them completely. Tricky as these viruses, they all have the same ability to disguises themselves in root of the system and disable antivirus programs. Thus, it becomes complicated for anti-virus software to detect and remove it. A part of users may even encounter blue screen or system crash randomly after infected. Moreover, users may have a hard time while browsing online since everytime they go to google and search up something, it lags and then when they click a link, it redirects them to a different site. If your browser keeps redirecting you to espeak911.com, colexity777.com, even 37.220.36.44, or Antivirus showing any evidence about these viruses, you must immediately remove them from your computer quickly in case it brings more troubles harming your computer further.


Homepage is changed without any permission.
Desktop background is gone somehow.
Browser setting is modified.
Browsers like IE and Firefox work slowly.
Registry files are corrupted.
Borwser Hijacker Infected Ways:
1. Most of time you may get espeak911, colexity777, and 37.220.36.44 viruses installed from unsafe freeware, shareware or advertising-supported programs such as various browser add-ons or toolbars.
2. This browser hijacker may get into the system even by clicking malicious code or distribute unsafe advertising pop-ups, visiting pornographic website or downloading attachment from spam emails.
3. If the virus has successfully hacked some famous social online communicate websites such as Facebook, Twitter, Yahoo and sites like that, it may be the reason you get this virus while you are surfing these websites.
Hence, no matter what way does the viruses access your computer, bear in mind all these three viruses are highly dangerous malware that are created for commercial, advertising or marketing purposes only. They have no benefit for your computer but bring harm to it. Remove them as quickly as you can.
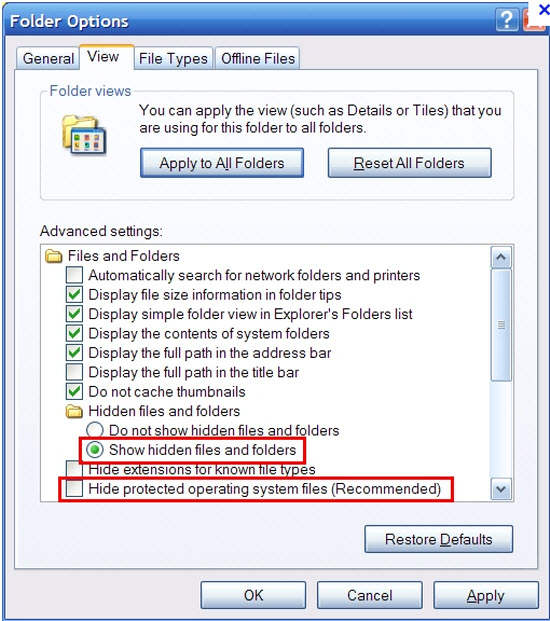
1. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
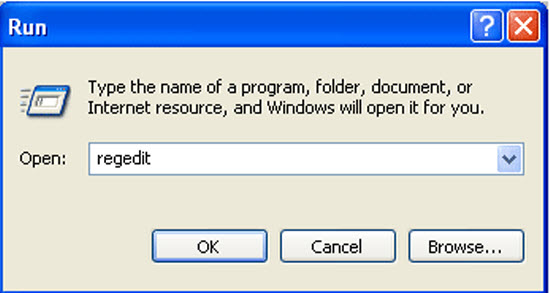
2. Open Registry entries. Find out the malicious files and entries and then delete all.
Attention: Always be sure to back up your PC before making any changes.
a. Press the “Start” button and then choose the option “Run”. In the “Open” field, type “regedit” and click the “OK” button.
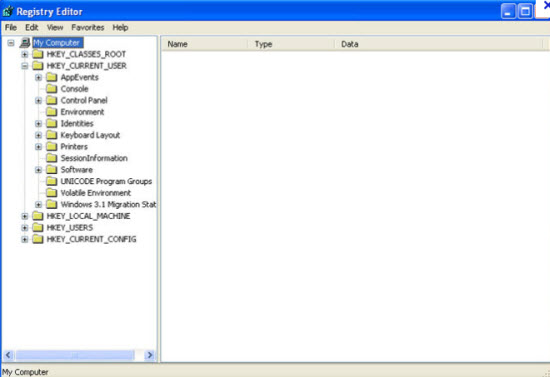
b. All malicious files and registry entries that should be deleted:
%Documents and Settings%\[UserName]\Application Data\[random]
%AllUsersProfile%\{random}\
%AppData%\Local\[random].exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[RANDOM]”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run “[RANDOM].exe”
Dangerous consequences of espeak911, colexity777, and 37.220.36.44 viruses are included: 1. change your browser and the overall Internet default settings without your approval. 2. Cause blue screen of death or random crash down. 3. Tremendous ads pop up your computer screen. 4. Browsers are directed randomly without your approval. In a word, when these viruses successfully installed, they can degrade overall web browser stability and performance as they waste too much computer resources. For no reason should you leave them on your computer. Users can follow the manual guide above to handle with those disgusting viruses.
If you have no idea how to do about that, you are welcome to contact experts from YooCare Online Tech Support for further help.
Published by on August 19, 2012 8:07 am, last updated on August 19, 2012 8:07 am



Leave a Reply
You must be logged in to post a comment.