AppRiver Security found that Azure Cloud Services still has security issues from phishing templates to malware and command and control services. Research found that its root cause is in Microsoft’s Azure infrastructure.
According to Bleeping Computer, two Azure-related malware attacks occurred in May.
Since May 10, nearly 200 websites hosted on the Azure App Services platform have been used to deploy inexpensive web hosting to maintain scams.
On May 28th, a new form of phishing activity appeared on the network. The attacker disguised the phishing content as an Office 365 warning email, claiming that the user had triggered an intermediate threat alert and used the fake login interface to send the user information to the specified website.
The latest findings from security researchers MalwareHunterTeam and JayTHL indicate that the above events are not independent attacks. After sample analysis, malware and other samples uploaded later are still present in Microsoft’s Azure infrastructure.
“Obviously, Azure has not detected malware residing on Microsoft servers.”
AppRiver’s David Pickett said that one of the examples ‘searchfile.exe’ was indexed by the VirusTotal scan service on April 26 when researching the attack sample. Windows Defender detected it when the user tried to download a malicious file on the computer. And prevent further actions of malicious files.
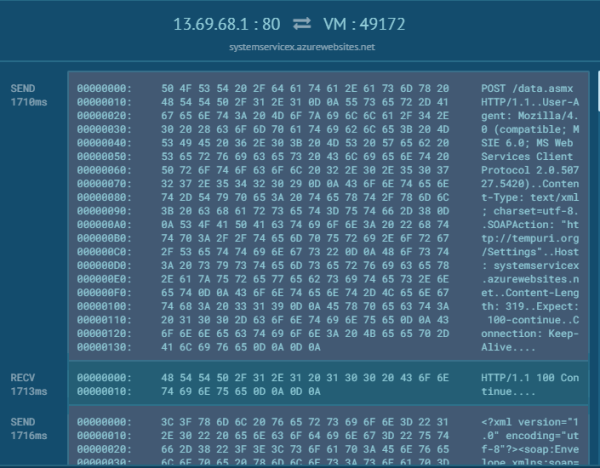
“Once run, this malicious agent generates an XML SOAP request every 2 minutes to check in and receive commands from the malicious actor Azure command and control site: systemservicex [.] azurewebsites [.] net / data [.] asmx.”
Researcher JayTHL said that the sample being crawled appears to be a simple agent that runs any commands received from the command and control server. If the attacker’s ID number is generated in order, it is determined that up to 90 computers can be controlled.
It is reported that Microsoft Azure is not the first platform to be abused to store malicious information, and similar situations have occurred in Google Drive, Dropbox and Amazon.
Often, cybercriminals can ruin legitimate websites and use them to host malicious content, and attackers can start a new round of action with little risk and cost.
Published by on June 6, 2019 2:26 am, last updated on June 6, 2019 2:26 am



Leave a Reply
You must be logged in to post a comment.