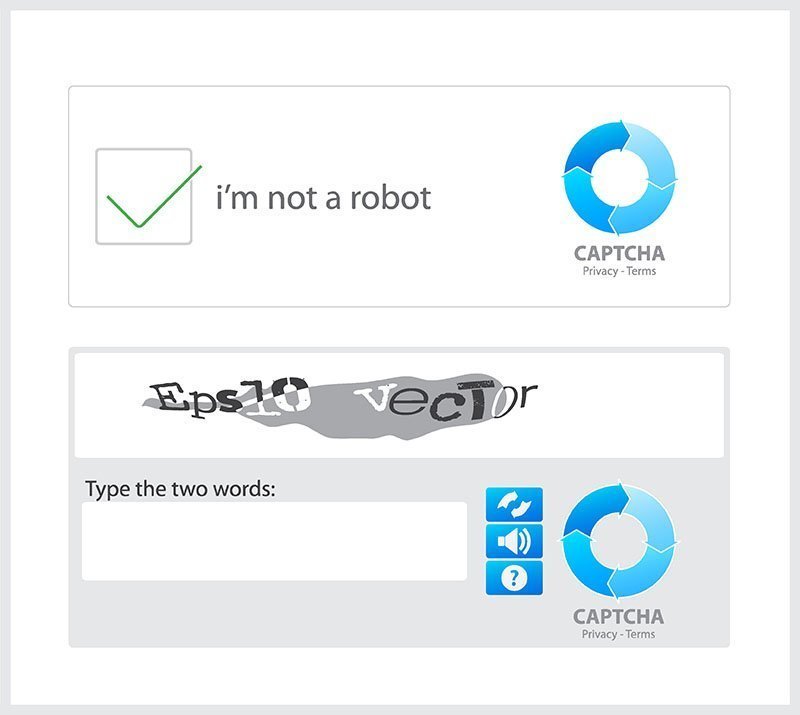
The Captcha verification code mechanism (a method for identifying real humans or network robots by identifying the letters in the picture) is familiar for most Internet users. However, this mechanism is no longer safe. Security researchers have found that hackers are using it to take victims to phishing pages. According to researchers, the phishing campaign uses captcha boxes to hide a fake Microsoft account login page from secure email gateways (SEGs) into order to trick victims into providing sensitive information.
It is reported that the hacker will carry a voice file in the email. Once the recipient presses the play button, a Captcha verification code page will pop up, and the Secure Email Gateway (SEG) scan cannot detect malicious components. Next, it will continue to lead the recipient to a Microsoft certificate phishing page with input requirements. Recipients may think it is a legit process to log them in, and enter login detail or personal information to proceed.
Researchers say that both the Captcha page and the phishing page are hosted by Microsoft architecture, and both pages use legitimate Microsoft top-level domain names. Hence, all are “safe” responses when compared to the domain blacklist.
“The SEG cannot proceed to and scan the malicious page, only the CAPTCHA code site. This webpage doesn’t contain any malicious items, thus leading the SEG to mark it as safe and allow the user through.,” the Cofense researchers said.
According to statistics, in all phishing activities, 75% are to steal the victim’s certificate. And in these attacks, more than 91% of the attacks are trying to bypass the SEG. In short, users should be especially careful when opening unsolicited emails, or accessing various websites through links, and being asked to enter a certificate.
Published by on September 27, 2019 2:29 am, last updated on September 27, 2019 2:29 am



Leave a Reply
You must be logged in to post a comment.